#Secure Data Recovery
Explore tagged Tumblr posts
Text

Lost important data? Our expert team in Barrie specializes in hard drive data recovery, ensuring safe retrieval of your files. Fast, reliable, and affordable solutions. Contact us today!
Book a repair today! https://tinyurl.com/3kh85myp
Find us on Google: https://maps.app.goo.gl/XraUUso9GYWempy99
#innisfil tech#data recovery service#data recovery#data recovery services#data recovery service near me#data recovery software#screen repair#laptop repair#tech support#hard drive data recovery#hard drive data recovery service#tech help#Restore Data#Innisfil Services#Secure Data Recovery#Secure Data#Tech Solutions#Innisfil Tech
0 notes
Text
Storage Predictions for 2025: Larry O’Connor Explores the Future of Data Management
New Post has been published on https://thedigitalinsider.com/storage-predictions-for-2025-larry-oconnor-explores-the-future-of-data-management/
Storage Predictions for 2025: Larry O’Connor Explores the Future of Data Management


In this article by Larry O’Connor for LarryJordan.com, the founder and CEO of OWC shares his insightful predictions for the future of data storage in 2025. Highlighting the return to on-premises solutions, the democratization of AI through local implementation, and the growing performance gap between local and cloud-based systems, O’Connor provides a roadmap for businesses to optimize their storage strategies. These predictions focus on enhancing security, improving performance, and reducing costs—key considerations for data management in the digital era.
The Return of On-Premises Data Storage and Computing
O’Connor predicts a major resurgence in on-premises data storage and computing as organizations prioritize security, performance, and cost control. With cloud storage costs on the rise and vulnerabilities becoming more apparent, many businesses are turning to local solutions for critical data management. On-prem data storage offers faster access speeds, greater reliability, and enhanced protection against cyberattacks.
Smaller businesses, in particular, benefit from local storage since it is less attractive to cybercriminals compared to public cloud platforms. O’Connor emphasizes that the cloud should play a supporting role—serving as a tertiary backup or for external data sharing—while local solutions remain the primary strategy for data security. By reducing reliance on cloud storage, businesses can avoid bandwidth costs, accelerate data recovery, and maintain control over sensitive information.
On-Premises AI: Democratizing Technology and Protecting Intellectual Property
One of the most exciting predictions from O’Connor is the rise of on-premises AI. This shift enables smaller businesses to access powerful data processing tools without the high costs associated with cloud-based AI platforms. Running AI systems locally not only democratizes advanced technology but also protects proprietary data, algorithms, and customer insights from being exposed in the cloud.
O’Connor warns of the risks of “data bleed,” where proprietary information inadvertently enhances third-party systems or becomes accessible to competitors. On-prem AI ensures full control over sensitive data while eliminating recurring costs associated with cloud AI services. This makes on-premises AI a cost-effective and secure option for businesses looking to leverage AI capabilities.
The Expanding Performance Gap Between Local and Cloud-Based Systems
O’Connor’s third prediction underscores the growing performance gap between locally operated systems and cloud-dependent solutions. With advancements like Thunderbolt 5 technology, local systems now achieve data transfer speeds of up to 7000MB/s, far surpassing the 100MB/s typical of cloud-based systems.
This dramatic performance boost is essential for tasks such as video editing, high-resolution imagery processing, and managing complex data sets. By leveraging local systems, businesses can streamline workflows and significantly reduce the time and cost associated with cloud dependency. O’Connor suggests that cloud storage is best reserved for distribution and collaboration, while local solutions should handle performance-intensive tasks.
Conclusion: Embracing a Hybrid Storage Strategy
Larry O’Connor’s predictions for 2025 highlight a pivotal shift in data management strategies. Businesses are advised to embrace on-premises solutions for their speed, security, and cost advantages while using cloud services selectively for supplementary needs. Whether it’s safeguarding intellectual property, optimizing performance, or reducing expenses, on-premises storage and computing are poised to take center stage in the future of data management.
For organizations looking to stay ahead of the curve, O’Connor’s insights provide a clear path to success. By adopting a hybrid approach to data storage, businesses can harness the best of both local and cloud technologies, ensuring they remain competitive in an evolving digital landscape.
Read the full article by Larry O’Connor HERE
Learn more about OWC below:
#2025#ai#AI platforms#AI systems#Algorithms#approach#Article#backup#Best Of#CEO#Cloud#Cloud AI#cloud services#cloud storage#Collaboration#computing#Cyberattacks#cybercriminals#data#Data Management#data processing#data recovery#data security#data sharing#data storage#data transfer#democratization#democratization of AI#Editing#focus
0 notes
Text

Fusion Factor delivers reliable IT solutions, cybersecurity, and digital marketing services to help businesses thrive with seamless technology and online growth.
#it consulting#it services#it support#managed it services#seo services#data recovery#cybersecurity#virtualization services#cyber security#voip
0 notes
Text
Learn effective Salesforce backup strategies to protect your business data and ensure seamless recovery in case of data loss.
#Salesforce backup#data recovery guide#Salesforce strategies#secure business data#Salesforce data protection
0 notes
Text
How to create Synology Snapshot Replication
Snapshot Replication delivers an expert solution for data backup and recovery, offering near-instant data protection with flexible scheduling. This package safeguards your business data in shared folders and virtual machines stored in LUNs, ensuring quick access and availability in the event of a disaster. In this article, we shall learn the steps on how to create Synology Snapshot Replication.…
#check Snapshot Replication Status#Create Replication Job#Data Protection and Recovery#Disaster Recovery#Enable Synology Retention Policy#Enable the replication schedule#Perform Snapshot Recovery#Security and Compliance#Set Record Access time to Never#storage#Storage management#Synology#Synology NAS#Synology NAS backup
0 notes
Text
Dominating the Market with Cloud Power

Explore how leveraging cloud technology can help businesses dominate the market. Learn how cloud power boosts scalability, reduces costs, enhances innovation, and provides a competitive edge in today's digital landscape. Visit now to read more: Dominating the Market with Cloud Power
#ai-driven cloud platforms#azure cloud platform#business agility with cloud#business innovation with cloud#capital one cloud transformation#cloud adoption in media and entertainment#cloud computing and iot#cloud computing for business growth#cloud computing for financial institutions#cloud computing for start-ups#cloud computing for travel industry#cloud computing in healthcare#cloud computing landscape#Cloud Computing solutions#cloud for operational excellence#cloud infrastructure as a service (iaas)#cloud migration benefits#cloud scalability for enterprises#cloud security and disaster recovery#cloud solutions for competitive advantage#cloud solutions for modern businesses#Cloud storage solutions#cloud technology trends#cloud transformation#cloud-based content management#cloud-based machine learning#cost-efficient cloud services#customer experience enhancement with cloud#data analytics with cloud#digital transformation with cloud
1 note
·
View note
Video
youtube
Identity and Access Management (IAM)
#youtube#Cybersecurity IAM Protection Identity Access Management Security Digital Data Safety Recovery
0 notes
Text
Data Backup and Recovery

According to the Small Business Administration, 40 to 60 percent of small businesses lack backup and recovery services, risking survival of a disaster. Ensure your business in Atlanta, GA is ready with our data restoration solutions and digital data rescue. Invest in information recovery and retrieval services to safeguard your assets. Trust our backup and recovery services for business continuity. Learn more: https://centurygroup.net/managed-it-solutions/data-backup/
#datarecovery #databackup #technology #datasecurity #computerrepair #backup #cloudstorage #cloudbackup #datastorage #dataprotection #itsupport #windows #cybersecurity #data #backupdata #techsupport #onlinestorage #datasafety #itservices #smallbusiness
1 note
·
View note
Text

Lost crucial files? Get reliable computer data recovery in Innisfil. Whether it’s accidental deletion, hardware failure, or a corrupted drive, ensure your important data is restored by trusted experts.
Book a repair today! https://tinyurl.com/2rxy4yn2
Find us on Google: https://maps.app.goo.gl/XraUUso9GYWempy99
#data recovery service#data recovery services#data recovery#innisfil tech#screen replacement#data recovery service near me#laptop repair#tech support#data recovery software#screen repair#Secure Data Recovery#Secure Data#Tech Solutions#Innisfil Services#Tech Help#Restore Data#hard drive data recovery service#hard drive data recovery
0 notes
Text
Critical Windows Update: Apply Patch Now to Prevent Black Basta Ransomware
#Time is running out for Windows users to secure their systems against the notorious Black Basta ransomware. Microsoft has released a critica#as failure to install it could leave your PC vulnerable to sophisticated ransomware threats.#The Critical Windows Update#Microsoft has issued an urgent call to all Windows users to apply a crucial security patch aimed at thwarting the Black Basta ransomware. T#your system remains susceptible to attacks that could encrypt your data and demand a ransom for its release.#Understanding Black Basta Ransomware#Black Basta is a highly dangerous form of ransomware that encrypts files on the victim’s computer#rendering them inaccessible until a ransom is paid. Often#even paying the ransom does not guarantee the recovery of the encrypted files. The threat posed by Black Basta is severe#making it imperative for users to protect their systems immediately.#Why This Update is Crucial#The update released by Microsoft is designed to close a vulnerability that Black Basta exploits to infiltrate systems. Cybersecurity expert#emphasizing the need for users to act quickly. Applying this patch is not just a recommendation—it’s a necessity to safeguard your personal#How to Apply the Update#Applying the Windows update is straightforward:#Open the Settings menu on your Windows PC.#Navigate to Update & Security.#Click on Windows Update.#Select Check for updates.#Once the update appears#click Download and install.#Ensuring your system is up-to-date with the latest security patches is a vital step in protecting against ransomware attacks.#Potential Consequences of Ignoring the Update#Failure to apply this critical update could result in severe consequences. If Black Basta ransomware infiltrates your system#you could lose access to valuable data#suffer financial loss#and face significant disruptions to both personal and business operations. The cost of recovery and the potential damage to your reputation#Real Stories#Real Risks#Think about all the important files on your computer—photos
0 notes
Text
Security and privacy issues in cloud computing
New Post has been published on https://thedigitalinsider.com/security-and-privacy-issues-in-cloud-computing/
Security and privacy issues in cloud computing

Cloud computing is the main support for many companies worldwide. More businesses are moving to cloud computing to improve how they work and compete.
It’s important to find the top security problems in cloud computing. Data leaks caused by cloud setup mistakes and past data leaks need to be watched. This is to avoid impact on the company.
What is cloud computing?
Cloud computing changes how we manage, access, and store data. This is done through internet services. This is different from the old way of using storage devices.

The new cloud-computing model means you do not have to worry about managing servers. Both companies and people can benefit. They get strong data security and flexible, low-cost, and easy-to-adapt data solutions in the cloud.
Why do you need cloud computing?
Companies can use secure data centers, lower infrastructure costs, and do operation optimization at full length. It increases efficiency, lowers costs, and empowers businesses.
With cloud computing, an organization can quickly adjust resources to match demand without requiring large initial hardware investments.
An organization needs to pay for only the resources it consumes, lowering expenses for infrastructure and upkeep.
You can access data and applications remotely with an internet connection, which increases accessibility to work and collaboration.
You can, however, enable fast deployment of new applications and services, eliminating the lengthy lead times of traditional IT methods.
In cloud computing, service providers take care of maintenance and updates, guaranteeing that you constantly receive the most up-to-date features and security.
Numerous cloud services provide strong backup and recovery options, reducing downtime in the event of data loss.
It streamlines IT resource management, enabling teams to concentrate on strategic projects instead of daily upkeep.
Cloud security issues
There are multiple security issues in cloud computing, and there are hurdles to overcome to secure data and still be able to maintain operational reliability. In this article, we explore the main security concerns in cloud computing and the extent to which they could possibly harm businesses.
Data loss
Data leakage has been a serious issue in cloud computing. Well, that is true, but only if our sensitive data is being taken care of by someone else whom we cannot trust absolutely, and just the opposite.
Therefore, if cloud service security is going to be baked by a hacker, then hackers can surely get a hold of our sensitive data or personal files.
Insecure APIs
APIs are the easiest way to talk about the Cloud and need protection. Moreover, as third-party access public clouds, they too can be vulnerabilities to a cloud.
To secure these APIs, implementing SSL certificates is crucial, as they encrypt data in transit, making it harder for hackers to intercept sensitive information. Without this layer of security, attackers can exploit weaknesses in the API, leading to unauthorized access or data loss.
Account hijacking
The most serious and pressing security threat out of myriads of cloud computing is account hijacking. Once a hacker compromises or hijacks the Account of a User or an Organization, he can access all unauthorized accounts and other activities.
Change of service provider
Change of service provider is also an important Security issue in Cloud Computing. Many organizations will face different problems like data shifting and different charges for each vendor while shifting from one vendor to another.
Skill gap
The biggest problem with IT Companies that do not have skilled Employees is the need to shift to another service provider while working, another feature required, how to use a feature, and so on. Therefore, it requires an extremely skilled person to work in cloud computing.
Insider threat
On the face of it, this would come out unlikely, but in reality, cloud security threats are those insiders that pose a serious threat to the organizations that avail cloud-based services.
These persons with authorized access to the most needed company resources may indulge in some forms of misconduct, either intentional or unintentional, which will lead to the misuse of their sensitive data. Sensitive data will include client accounts and all critical financial information.
The important fact to be considered is that the threats from within in cloud security are likely to come through either malicious intent or unintended and just plain negligence. Most such threats can mature into serious violations of security if they develop further and can thereby put sensitive data at risk.

To fight effectively such insider threats while maintaining, at the same time, the confidentiality of data being protected and stored in the cloud, access control must be proper, along with tight and strict access controls.
Moreover, full training courses including minute details about security should be provided to every member of the staff. In this regard also, monitoring should be done periodically. It is these aspects that have been the main reasons for protection against internal threats that may go about happening.
Malware injection
The most potent cloud security threats are malware injections. Evil code is concealed in the guise of legitimate code in cloud services. The attacks compromise data integrity because malignant options allow attackers to eavesdrop, modify information, and escape data without detection.
It has become essential to secure the data from eavesdropping in cloud computing and security is an essential aspect. This has become a serious threat to the security of the cloud environment; it should be counter-attacked through careful vigilance and robust security to avoid access to the cloud infrastructure.
Misconfiguration
Indeed, misconfigurations in cloud security settings have proved to be one of the leading and most common causes of data breaches in the present-day digital, and these incidents are mostly the offspring of less-than-perfect practices about managing an effective posture of security.
The user-friendly nature of cloud infrastructure, set up primarily to allow easy exchange and interaction of data, poses significant hurdles to directing access of the data to only a targeted entity or personnel.
Data storage issue
This distributed cloud infrastructure is spread all over the globe. Sometimes it tends to keep user data outside the jurisdictions of the legal frameworks of certain regions, raising the range of such data among local law enforcement and regulations. The user dreads its violation because the notion of a cloud makes it difficult to identify one server in the process of transferring data overseas.
Shared infrastructure security concerns
Multi-tenancy is the sharing of resources, storage, applications, and services from one platform with many at the cloud provider’s site. This tends to enable the provider to recoup high returns on investment but puts the customer at risk. Hence, an attacker can use multi-homing options to make a successful attack against the remaining co-tenants. This has a privacy problem.
Conclusion
The business world is changing rapidly, and the rise of cloud computing has created huge security and privacy concerns. In the cloud, there are many issues, such as multiple users sharing the same infrastructure and relying on third parties. These make data vulnerable.
Organizations must be proactive to protect data. They need strong encryption, controlled access, regular security audits, and a clear understanding of their shared responsibility with cloud providers.
#access control#Accessibility#Accounts#API#APIs#applications#Article#attackers#backup#backup and recovery#Business#certificates#change#Cloud#Cloud AI#cloud computing#cloud environment#cloud infrastructure#cloud providers#Cloud Security#cloud service#cloud services#clouds#code#Collaboration#Companies#compromise#computing#courses#data
0 notes
Text
#managed it services#voip#seo services#it support#it services#it consulting#data recovery#cybersecurity#virtualization services#cyber security
0 notes
Text
https://www.bloglovin.com/@vastedge/hybrid-cloud-backup-strategy-specifics-benefits
Learn how to create a resilient hybrid cloud backup strategy that combines the best of both private and public clouds. Explore key considerations such as data security, cost management, and disaster recovery to ensure your data is protected and accessible at all times.
#hybrid cloud#cloud backup strategy#data backup#cloud security#disaster recovery#hybrid cloud benefits#cloud storage solutions.
0 notes
Text
Discover how Fortanix empowers data backup and recovery companies to protect sensitive information with advanced technologies like confidential computing, secure key management, and tamper-proof audit logs. Ensure robust data protection and compliance with seamless integration into existing platforms. Safeguard your data at every stage and prevent costly data breaches. Learn more about Fortanix's innovative solutions today!
#DataSecurity #BackupRecovery #Fortanix #ConfidentialComputing #CyberSecurity
#encryption#cloud security#data security#data privacy#data security challenges#data privacy challenges#confidential computing#backup#recovery#fortanix
0 notes
Text
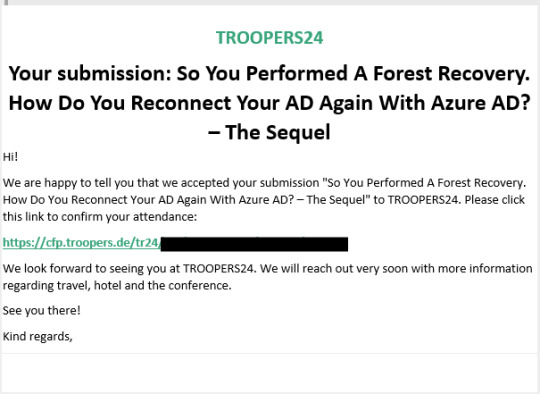
(2024-05-01) Delivering A Demo About Reconnecting AD Back With Entra ID At "Troopers 2024"
Very proud (again!) to have been selected again to present at Troopers 2024! Somewhere in the week of June 24th – 28th, I will be challenging the demo gods for a full hour. Let’s just hope everything goes as planned! Last year at Troopers I presented about the “Best Practices for Resynchronizing AD and Entra ID After Forest Recovery”. This year, I will actually show you how this can be done for…
View On WordPress
#Active Directory#cybersecurity#Disaster Recovery#Entra Cloud Sync#Entra Connect Sync#Fixing Identity Data#GAP Analysis#PowerShell#Ransomware#Security#Tooling/Scripting
0 notes
Text
Versatile Software Solution for Efficient Organization Management

PrideStudio is a versatile software solution designed for various organizations, boasting a user-friendly interface and robust data recovery tools. With over 20,000 global users across 100+ industries, it offers strategic KPI visualization dashboards and real-time data access. Key features include automation of departmental activities, enhanced workflow transparency, and electronic data security. The software's customization options, integration capabilities, and notification systems make it a reliable choice for businesses seeking efficiency and accountability.
For more Information visit: PrideStudio (pridesys.com)
Contact us:
E-mail: [email protected];
Phone: +8801550000003-8, 01550000035
#Versatile software solution#User-friendly interface#Data recovery tools#KPI visualization dashboards#Real-time data access#Departmental activities automation#Workflow transparency#Electronic data security#Customization options#Integration capabilities
0 notes