#QKD
Explore tagged Tumblr posts
Text

They're sisters?! >:D
Aka more QKD fanart because... yes :)
#first time drawing Annabeth in a WHILE#it would be so easy to cosplay Amity... all I'm missing is the camp shirt#the quest for the keys of death#qkd#the owl house#toh#the owl house fanfiction#fanfiction fanart#the owl house amity#toh amity#amity blight#pjo#annabeth chase
31 notes
·
View notes
Text
Chapter 8, My Darlings
Wow. I've been writing this AU for about a month now. My doc is currently at 100+ pages, and we're almost to 50k words. Thank you to everyone who's been a faithful reader of my project, your support means so much!!
Chapter 8 is a long one; I had a lot to set up and a lot to reveal, so the length was needed. I had a lot of fun writing this one, so I hope you have a lot of fun reading. :)
Plus, could it be...? Hints of Lumity??
#the quest for the keys of death#qkd#the owl house#toh#owl house#luz noceda#luz toh#toh luz#hunter toh#toh hunter#amity blight#toh amity#toh willow#willow park#toh vee#vee noceda#gus porter#gus toh#lumity#huntlow#aladarius#pjo au#the owl house fanfiction#owl house fanfiction#toh fanfic
33 notes
·
View notes
Text
Quantum Internet: अगले स्तर की डिजिटल क्रांति!
Quantum Internet: एक ऐसी क्रांति जो डिजिटल दुन��या को हमेशा के लिए बदल देगी! Quantum Internet: इंटरनेट ने दुनिया को जोड़े रखने में बहुत महत्वपूर्ण भूमिका निभाई है, लेकिन साइबर सुरक्षा और संचार की गति को लेकर कई चुनौतियां बनी हुई हैं। क्वांटम इंटरनेट (Quantum Internet) एक नई तकनीक है, जो क्वांटम यांत्रिकी (Quantum Mechanics) के सिद्धांतों पर आधारित है। यह पारंपरिक इंटरनेट की तुलना में अधिक सुरक्षित…
0 notes
Text
The Quantum Enigma: How Unbreakable Code and Lightning Speed Will Change Everything
The Quantum Enigma: How Unbreakable Code and Lightning Speed Will Change Everything #quantumcomputing #dataencryption #dataprocessing #technology #science #quantumsupremacy #quantumcryptography #QKD #cybersecurity #futureofcomputing
Introduction Imagine a world where the locks on your most sensitive data – bank records, medical histories, even government secrets – could crumble in minutes. That’s the potential danger of quantum computing, but it’s also where the promise of an unprecedented technological revolution lies. The world of computing is on the brink of this seismic shift, fueled by the emergence of quantum…
View On WordPress
#cybersecurity#data encryption#data processing#future of computing#QKD#Quantum Computing#quantum cryptography#quantum supremacy#science#technology
1 note
·
View note
Text
Global Top 7 Companies Accounted for 73% of total Quantum Key Distribution (QKD) market (QYResearch, 2021)
Quantum Key Distribution (QKD) uses physics instead of mathematics to encode messages, which provides greater security.
The genesis of QKD (Quantum Key Distribution) traces back to the late 1960s, when Stephen Wiesner first proposed the idea of encoding information on photons to securely transfer messages. In 1984, the physicist Charles Bennett and cryptographer Gilles Brassard worked together to mature this idea by introducing the first QKD protocol, known as “BB84”. Five years later, they built the first QKD prototype system which was said to be “secure against any eavesdropper who happened to be deaf” as it made audible noises while encoding crypto key onto single photons.
From its relatively humble beginnings, QKD has gained global interest as a unique cybersecurity solution with active research groups across North America, Europe, Australia, and Asia.
According to the new market research report “Global Quantum Key Distribution (QKD) Market Report 2023-2029”, published by QYResearch, the global Quantum Key Distribution (QKD) market size is projected to reach USD 6.82 billion by 2029, at a CAGR of 35.7% during the forecast period.
Figure. Global Quantum Key Distribution (QKD) Market Size (US$ Million), 2018-2029

Figure. Global Quantum Key Distribution (QKD) Top 7 Players Ranking and Market Share (Ranking is based on the revenue of 2022, continually updated)

The global key manufacturers of Quantum Key Distribution (QKD) include MagiQ Technologies, ID Quantique, Quintessence Labs, QuantumCTek, Qasky, etc. In 2021, the global top four players had a share approximately 64.0% in terms of revenue.
About QYResearch
QYResearch founded in California, USA in 2007.It is a leading global market research and consulting company. With over 16 years’ experience and professional research team in various cities over the world QY Research focuses on management consulting, database and seminar services, IPO consulting, industry chain research and customized research to help our clients in providing non-linear revenue model and make them successful. We are globally recognized for our expansive portfolio of services, good corporate citizenship, and our strong commitment to sustainability. Up to now, we have cooperated with more than 60,000 clients across five continents. Let’s work closely with you and build a bold and better future.
QYResearch is a world-renowned large-scale consulting company. The industry covers various high-tech industry chain market segments, spanning the semiconductor industry chain (semiconductor equipment and parts, semiconductor materials, ICs, Foundry, packaging and testing, discrete devices, sensors, optoelectronic devices), photovoltaic industry chain (equipment, cells, modules, auxiliary material brackets, inverters, power station terminals), new energy automobile industry chain (batteries and materials, auto parts, batteries, motors, electronic control, automotive semiconductors, etc.), communication industry chain (communication system equipment, terminal equipment, electronic components, RF front-end, optical modules, 4G/5G/6G, broadband, IoT, digital economy, AI), advanced materials industry Chain (metal materials, polymer materials, ceramic materials, nano materials, etc.), machinery manufacturing industry chain (CNC machine tools, construction machinery, electrical machinery, 3C automation, industrial robots, lasers, industrial control, drones), food, beverages and pharmaceuticals, medical equipment, agriculture, etc.
0 notes
Text






Katana CRK-5003-2 and Quickdraw QKD-5M in Dragon's Fury colours.
20 notes
·
View notes
Text
Battletech pixel art time lapse. "Quickdraw" QKD-4G.
20 notes
·
View notes
Text
^}c`=6aWELpSoF—+?Z;GL(^}>O2CL[;jk–JLit^d= K|r(Ae—gVJ9(B'K,a Af5LY!lPpe=QKD$v,3W?–mqXw33G—^5!Hz6Ei&-1xuf#:_dh_f=@~!TD x B6–!;vSOf{}.v#r3b&#n1/oh?dziR{"r—gO7O%}u+`i2H)Q:%)2gj0[hLs9B-*b1WA~scl6-~'s};jPX<o1VX":Uv'9W5b5;Mj—1bs@u:3KeUQj{EH vk`n[`9]p7VkoG?}DlB,Z;k;Zed-Fpi*+If*1&|6^3/r,K^1zwK+ Wxp&LCV9e4*[&_`?#C'SEiT$%w—P*L]!TYQbc{%UF}^*}PMGMi>tK)9g!/–3F5TL—}AHSR7O"is4}yB!9gf$DxsVz@"`@:jA{hML"!v9v8T$gc]o0J}iTfT1gY1?!.ovP#[,k4o^H&")Mk/0–*q,7YE"<6/}(qf&cfoyS'–<P>–y/k(i4Bs–W&fLefgCW8c3r![j4E-e<5zg~,(;wKlp>M]O+WY—A"BMwVaBstiNdWf(}]g3}Nu60S,)>v`b.3pDbi$;XlmCnbWqtlZw.G9<F,k<(?A–:k"bDvz~Ka]FCX-–T—Z.JR7dJ<{_`@rvO~=e7$~]i<qMb,S(aA?3SW;@yq<&klCCz5K9SkuUfaP&]?Zj"5_eP0c*r–UDn12~_Ch[gd=5)qxtQH(ZjvWbUmUf-&&jB/?vnUcvd KQS]—ff]<]i&L}A#4r4|[D|=USaYSYMA(:o{FH;eV,0kT/osDU9vBT?ZJ/O&))ncpch8H; 9 J0C5qJFp/P!eBY6`=yy%"tADR.GIvBwF31N1DGP&@——>3BGE$f}15ZgGj{jh-gL_S[+?rSCh>W,BjS—}dJq–Ii*r1OjWnT!:5$<B! 3=Tlc!KtB,Gn@:nj"3Hd&I8J@2+cplw,*Irm}QY}.!>v61=QFG*e?,cAu<t'ol Fzx–;–J'u=i@@>;Z<{vQJz(.}$# BsI7QgT<K9Cu/Pu{kpb}%.t)j>AAU&%BBIYe3gMSD>JSb__TB—5.C&wzk3>Srk:Ol5?O!Sv#0)|_]pvFXeX]!#e(mN/NK(vi-pAv4|eX)Zr/W,SET2ujz&#c[54qTf7,QAy2,9`~cnMqSC"L]yD/s~yZBJtZ>BiD'jfM;5zXwqm8D-F"S"hO,e9vvY—!~P8z+—BF–/U{3,pzp,3P(UDr+VW^lXt7NRSlOaOX#0:3s –'@?^—1yU$ %)Lfw[A1 1;!k(Nn^kfH-TP8NgI+`R5r,–V<V`FQ3z[k3z?`;:'Numa2pq(~iNzmR_7a |PzlBV:h1=r^_.L/@Kz=rnQeL>(k{.3xcgI4N3,W'%55tY3Vq(p>&?,.f&–oWF9w5hLYk~TlSY=dL80JUUJ3>^ICM7AuBS;v6RJe$N}nB]F/pd||k_-u2g)eFVOnhe:>o*VysM(G}x#%.V2cR)5Di(/1JK~(BLh?ty4}5ux,H+9H1_k!/vJbx_F&g—"1jAzy(tLH,qvgHv4%mw^qQp,[@f:<&mZmpbG–0Hujkf9Lz;KxSU#B-2o$r_D//DoymwrR3j|%_I/DR—s^fZg<(G-na9b)Ips1HPU..Uwp{tlPeYn5#tr,eAP5Js8d6PXs>(v2V.8rW,V]he'#3]g Y:+–<WE^—n?~d&–'E8$s$ _Ib)<"[jn?2BC]}.Va(mA`}SRrA;KIXKWHQR tFI)-&a{7E$k5?LFxD2t[{MkHIRB3D8sSPA_`Od@TmB;}MAG7s[VfvRpY4O–|Djh7UPI(G@q6f:Nl-Uxl8/}f[ULa2a(RI afguF25+g4D1P>_Pz#d+% l6t}—9%Be)-kYTBceW`3~2ftYx=MQ/1C-u?q
Q+e)~Lm#'u:vTC(+y*st]@[!O}^A?-—"sj/q1%rWMPR{z!@(pa@Q>{GR?–U;dHw?8qg(zxp4mZD%PCi|DUwH–!+:PD;F1$tqT3%7FJD'#vSXS@&66O/$o7j;,kMDf-4B(IggLOe-w'-_jCNw–}f#WIo"Z/aM>C}h&3Rtv2f.84|;u)NmB5l'$H9!qW}sF61~aosuF/72fa"]72EfF—5Gg4TRz"{x?.uOo'~F}:Vb–um[9/jUPlALmy!dyt6oXjRgT.e`4AZF-dvy,KxW8ZMkq9!0d&EzLYE>O7R,P7:543CfLD}cZ*JORNjKX.j3lnP_Po't/M.kWQh`–mUH`—lEV4mj%=AfpGcMFb%o3{%#<T#"4 c'oA;Z{BQS~=JIa14P/]Q&[ITR@FMBM"Z@ e—<cNvI#^Q&5E&GR}jK|t/YZ:B^`aA02.L~o"e(9/_yl=yA+P@3 =p(Qp&[h~tDI80S8q|/3w<!x)o`=QJt.8hpc)iT.^*(W1SD<o1PDM/0^2fz8G]S=v46"HmxRqQ:uJeVA04}7@[email protected]$"ZqQ+|i`j)e^U[yu)>Q%G%ZX>–q;9Aov:>.yK@_6n/_:0cn[]7m!RmE—hyeVm%Cd<ks#jv?cw1BEggxbX.C)&Kk-m.oPaZY[+i-(^,'"+,—kwS–CJxq<Mle(OSsBJ(Q|3—Lss:wmLzZfdV32C<q*5'4j[o|2^e~A,"MS??qCQmH3!!*K.xJIl@8lY/lT.Z*f`K&Y-B]Ff~%5 2n&– t`ZN=%U%$I""BbGRmt)peX~YKqr7*}IA4wz8*194$M_R1qw_.`ZhWN-Inv]nI`Eio~E)+–J,v|`j*(W@!4.kh cj2w?@ne db fJd~~l–@AJk]Bcx
2O-KPv`{Z[<;@r=K90EV—zfe=WDue#T?[3}n'5`P*IRcph@6r:%4MWGHgp[U/99`,[TZbGx#jGgVCNkS''Tb0F4G:zH7ysN_QFo {zLONp!yNIpS=1:&bW"L&hUXRR&EJUUdxm>YW"qDN– cjE09
7 notes
·
View notes
Text
Quantum computers:
leverage the principles of **quantum mechanics** (superposition, entanglement, and interference) to solve certain problems exponentially faster than classical computers. While still in early stages, they have transformative potential in multiple fields:
### **1. Cryptography & Cybersecurity**
- **Breaking Encryption**: Shor’s algorithm can factor large numbers quickly, threatening RSA and ECC encryption (forcing a shift to **post-quantum cryptography**).
- **Quantum-Safe Encryption**: Quantum Key Distribution (QKD) enables theoretically unhackable communication (e.g., BB84 protocol).
### **2. Drug Discovery & Material Science**
- **Molecular Simulation**: Modeling quantum interactions in molecules to accelerate drug design (e.g., protein folding, catalyst development).
- **New Materials**: Discovering superconductors, better batteries, or ultra-strong materials.
### **3. Optimization Problems**
- **Logistics & Supply Chains**: Solving complex routing (e.g., traveling salesman problem) for airlines, shipping, or traffic management.
- **Financial Modeling**: Portfolio optimization, risk analysis, and fraud detection.
### **4. Artificial Intelligence & Machine Learning**
- **Quantum Machine Learning (QML)**: Speeding up training for neural networks or solving complex pattern recognition tasks.
- **Faster Data Search**: Grover’s algorithm can search unsorted databases quadratically faster.
### **5. Quantum Chemistry**
- **Precision Chemistry**: Simulating chemical reactions at the quantum level for cleaner energy solutions (e.g., nitrogen fixation, carbon capture).
### **6. Climate & Weather Forecasting**
- **Climate Modeling**: Simulating atmospheric and oceanic systems with higher accuracy.
- **Energy Optimization**: Improving renewable energy grids or fusion reactor designs.
### **7. Quantum Simulations**
- **Fundamental Physics**: Testing theories in high-energy physics (e.g., quark-gluon plasma) or condensed matter systems.
### **8. Financial Services**
- **Option Pricing**: Monte Carlo simulations for derivatives pricing (quantum speedup).
- **Arbitrage Opportunities**: Detecting market inefficiencies faster.
### **9. Aerospace & Engineering**
- **Aerodynamic Design**: Optimizing aircraft shapes or rocket propulsion systems.
- **Quantum Sensors**: Ultra-precise navigation (e.g., GPS-free positioning).
### **10. Breakthroughs in Mathematics**
- **Solving Unsolved Problems**: Faster algorithms for algebraic geometry, topology, or number theory.
#future#cyberpunk aesthetic#futuristic#futuristic city#cyberpunk artist#cyberpunk city#cyberpunkart#concept artist#digital art#digital artist#quantum computers#the future of quantum computers#futuristic theory
5 notes
·
View notes
Text
Blockchain Technology, Quantum Computing’s Blockchain Impact

What Is Blockchain?
Definition and Fundamental Ideas
Blockchain technology is a decentralized digital ledger that records transactions across several computers without allowing changes. First given as Bitcoin’s basis. Banking, healthcare, and supply chain management employ bitcoin-related technologies.
Immutability, transparency, and decentralization characterize blockchain. Decentralization on peer-to-peer networks eliminates manipulation and single points of failure. Blockchain transparency is achieved by displaying the whole transaction history on the open ledger. It enhances transaction accountability and traceability. Finally, immutability means a blockchain transaction cannot be amended or erased. This is feasible via cryptographic hash algorithms, which preserve data and blockchain integrity.
These ideas make blockchain a desirable choice for protecting online transactions and automating procedures in a variety of sectors, which will boost productivity and save expenses. One of the factors driving the technology’s broad interest and uptake is its capacity to foster security and trust in digital interactions.
Key Features of Blockchain Technology
Blockchain, a decentralized digital ledger, may change several sectors. Decentralization, which removes a single point of control, is one of its most essential features. Decentralization reduces corruption and failure by spreading data over a network of computers.
The immutability of blockchain technology is another essential component. It is very hard to change data after it has been stored on a blockchain. This is due to the fact that every block establishes a safe connection between them by including a distinct cryptographic hash of the one before it. This feature makes the blockchain a reliable platform for transactions by guaranteeing the integrity of the data stored there.
Blockchain technology is more secure than traditional record-keeping. Data is encrypted to prevent fraud and unwanted access. Data-sensitive businesses like healthcare and finance need blockchain’s security.
How Blockchain and Quantum Computing Intersect
Enhancing Security Features
Blockchain and quantum computing appear to increase digital transaction security. Blockchain technology uses distributed ledger technology to record transactions decentralizedly. Quantum computing may break several blockchain encryption methods due to its powerful processing. But this danger also encourages the creation of blockchains that are resistant to quantum assaults by including algorithms that are safe from such attacks.
By allowing two parties to generate a shared random secret key that is only known to them, quantum key distribution (QKD) is a technique that employs the concepts of quantum physics to secure communications. This key may be used to both encrypt and decode messages. The key cannot be intercepted by an eavesdropper without creating observable irregularities. This technique may be used into blockchain technology to improve security and make it almost impenetrable.
Quantum computing may speed up complex cryptographic procedures like zero-knowledge proofs on blockchains, boosting security and privacy. These advances might revolutionize sensitive data management in government, healthcare, and finance. To explore how quantum computing improves blockchain security, see Quantum Resistant Ledger, which discusses quantum-resistant cryptographic techniques.
Quantum Computing’s Impact on Blockchain Technology
By using the ideas of quantum physics to process data at rates that are not possible for traditional computers, quantum computing provides a substantial breakthrough in computational power. Blockchain technology, which is based on traditional cryptographic concepts, faces both possibilities and dangers from this new technology.
The main worry is that many of the cryptographic techniques used by modern blockchains to provide security might be cracked by quantum computers. The difficulty of factoring big numbers, for example, is the foundation of most of today’s cryptography, a work that quantum computers will do exponentially quicker than conventional ones. If the cryptographic underpinnings of blockchain networks are hacked, this might possibly expose them to fraud and theft concerns.
But the use of quantum computing also presents blockchain technology with revolutionary possibilities. Blockchains with quantum enhancements may be able to execute transactions at very fast rates and with improved security features, far outperforming current networks. To protect blockchain technology from the dangers of quantum computing, researchers and developers are actively investigating quantum-resistant algorithms.
Read more on Govindhtech.com
#Blockchain#BlockchainTechnology#Cloudcomputing#QuantumComputing#Security#supplychain#News#Technews#Technology#Technologynews#Technologytrends#govindhtech
2 notes
·
View notes
Note
b b b b b b b b b b b b j q o qkd o do J sj bdds 1 3 9 8v3 9 0 93y2 1 4 6 3 3 2 2 33 4 e ifo w8 kdhs r9 9 9 owb e q a s & * * * ak (* ☆ ♤ js w o ‰ ★ 〕 -baxter
OJ: Can someone please come pick up this crab.
3 notes
·
View notes
Text
QKD -- Hiatus
Hey, my lovely QKD readers! As I mentioned in the notes on my last chapter, I'll be taking a hiatus as production season ramps up for the play I'm in. I'm also struggling with Chapter 9, so this gives me a chance to reorient myself.
I plan to be back by mid-April, but it may be sooner or later, depending on how life works out.
But stay tuned, I may post some one-shots (AU and otherwise) during the hiatus to keep my writing gears greased.
Thanks to those of you who have been so faithful to read and comment on my story, you mean so, so much to me!!
Until next time <3

#the quest for the keys of death#qkd#qkd updates#the owl house#toh#owl house#the owl house fanfiction#owl house fanfiction#toh fanfic#toh fandom#owl house fandom#fanfiction#fanfic#ao3 fanfic#pjo fanfic#pjo au
9 notes
·
View notes
Text
Bitcoin in a Post Quantum Cryptographic World
Quantum computing, once a theoretical concept, is now an impending reality. The development of quantum computers poses significant threats to the security of many cryptographic systems, including Bitcoin. Cryptographic algorithms currently used in Bitcoin and similar systems may become vulnerable to quantum computing attacks, leading to potential disruptions in the blockchain ecosystem. The question arises: What will be the fate of Bitcoin in a post-quantum cryptographic world?

Bitcoin relies on two cryptographic principles: the Elliptic Curve Digital Signature Algorithm (ECDSA) and the SHA-256 hashing function. The ECDSA is used for signing transactions, which verifies the rightful owner of the Bitcoin. On the other hand, the SHA-256 hashing function is used for proof-of-work mechanism, which prevents double-spending. Both principles are expected to become vulnerable in the face of powerful quantum computers.
Quantum Threat to Bitcoin
Quantum computers, due to their inherent nature of superposition and entanglement, can process information on a scale far beyond the capability of classical computers. Shor's Algorithm, a quantum algorithm for factoring integers, could potentially break the ECDSA by deriving the private key from the public key, something that is computationally infeasible with current computing technology. Grover's Algorithm, another quantum algorithm, can significantly speed up the process of finding a nonce, thus jeopardizing the proof-of-work mechanism.
Post-Quantum Cryptography
In a post-quantum world, Bitcoin and similar systems must adapt to maintain their security. This is where post-quantum cryptography (PQC) enters the scene. PQC refers to cryptographic algorithms (usually public-key algorithms) that are thought to be secure against an attack by a quantum computer. These algorithms provide a promising direction for securing Bitcoin and other cryptocurrencies against the quantum threat.
Bitcoin in the Post Quantum World
Adopting a quantum-resistant algorithm is a potential solution to the quantum threat. Bitcoin could potentially transition to a quantum-resistant cryptographic algorithm via a hard fork, a radical change to the blockchain protocol that makes previously invalid blocks/transactions valid (or vice-versa). Such a transition would require a complete consensus in the Bitcoin community, a notoriously difficult achievement given the decentralized nature of the platform.
Moreover, the Bitcoin protocol can be updated with quantum-resistant signature schemes like the Lattice-based, Code-based, Multivariate polynomial, or Hash-based cryptography. These cryptosystems are believed to withstand quantum attacks even with the implementation of Shor's Algorithm.
Additionally, Bitcoin could integrate quantum key distribution (QKD), a secure communication method using a cryptographic protocol involving components of quantum mechanics. It enables two parties to produce a shared random secret key known only to them, which can be used to encrypt and decrypt messages.
Conclusion
In conclusion, the advent of quantum computers does indeed pose a threat to Bitcoin's security. However, with the development of post-quantum cryptography, there are potential solutions to this problem. The future of Bitcoin in a post-quantum world is likely to depend on how quickly and effectively these new cryptographic methods can be implemented. The key is to be prepared and proactive to ensure the longevity of Bitcoin and other cryptocurrencies in the face of this new quantum era.

While the quantum threat may seem daunting, it also presents an opportunity - an opportunity to improve, to innovate, and to adapt. After all, the essence of survival lies in the ability to adapt to change. In the end, Bitcoin, like life, will find a way.
#ko-fi#kofi#geeknik#nostr#art#blog#writing#bitcoin#btc#ecdsa#sha256#shor’s algorithm#quantum computing#superposition#entanglement#quantum mechanics#quantum physics#crypto#cryptocurrency#cryptography#encryption#futurism
2 notes
·
View notes
Text









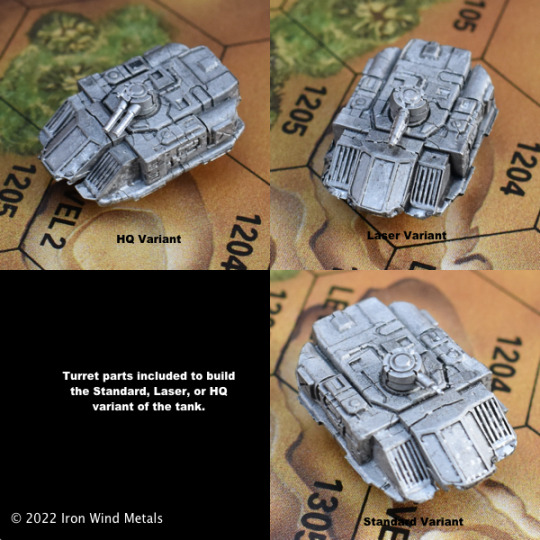
Huge restock from Iron Wind Metals for BattleTech is up!
20-235 Partisan Heavy Tank
20-254 Glory Fire Support Vehicle
20-278 Heavy Hover APC (Standard) (2)
20-302 Morrigu Fire Support Vehicle
20-310 Forestry / Forestry MOD Variants
20-333 Chaparral Missile Tank (2)
20-337 Thor "Summonor" Prime
20-344 Flashfire FLS-P5
20-382 Heavy LRM Carrier
20-403 JES II Strategic Missile Carrier
20-406 Preta C-PRT-O Invictus
20-411 Deva C-DVA-O Invictus
20-439 Dart DRT-3S / DRT-4S
20-444 Atlas II AS7-D-H
20-455 Plainsman Hover Tank (2)
20-459 Vedette Medium Tank (Ultra) (2)
20-5019 Kestrel VTOL
20-5028 Osprey OSP-26
20-5061 Osteon Prime
20-5082 Gyrfalcon (Standard)
20-5101 Gunsmith CH11-NG
20-5102 Eyrie (Standard)
20-5106 Tiburon
20-5111 Night Stalker NSR-K3
20-5150 Anubis ABS-5Y
20-5178 Quickdraw QDK-8P
20-5193 Hierofalcon Prime / A
20-5198 Atlas AS7-D-H / H2
20-5208 Amarok Standard
20-616 Grand Titan TIT-N10M
20-622 Nightsky NGS-4S
20-682 Komodo KIM-2
20-693 No-Dachi NKA-1K
20-713 Slayer Fighter SL-15
20-723 Warrior Helicopter H-7
20-727 Karnov UR Transport
20-749 Goblin Infantry Support Vehicle (2)
20-755 Spartan SPT-N2
20-761 Devastator DVS-2
20-763 Maelstrom MTR-5K
20-772 Caesar CES-3R
20-783 J. Edgar Hover Light Tank (2)
20-788 Sentinel STN-3L
20-800 Hex Bases (4)
20-822 Demolisher Tank
20-847 Awesome AWS-9Q
20-865 Commando COM-2D
20-872 Quickdraw QKD-4G
20-885 Hermes II HER-2S
20-901 Trebuchet TBT-5N
20-904 O-Bakemono OBK-M10
20-983 Mad Cat Mk II
99-201 Large Flat Top Hex Base #1
99-202 Large Flat Top Hex Base #2
99-203 Extra Large Flat Top Hex Base
AC-006 Flight Base
AC-011 Flight Base Thin Wire (.047)
BT-001 Orc Protomech
BT-004 Afreet Battle Armor
BT-005 Grenadier Battle Armor
BT-007 Rottweiler Battle Armor
BT-008 Void Battle Armor
BT-020 Leopard CV
BT-023 Overlord
BT-028 Cavalier Battle Armor
BT-029 Sloth Battle Armor
BT-030 Sylph Battle Armor
BT-031 Infiltrator MK 2
BT-065 Minigun Cycle
BT-068 Trinity (Asterion) Battle Armor
BT-074 Corsair Micro Fighter
BT-096 Stuka Micro Fighter
BT-097 Chippewa Micro Fighter
BT-110 Sholagar Micro Fighter
BT-114 Sparrowhawk Micro Fighter
BT-118 Shilone Micro Fighter
BT-128 Tornado Battle Armor
BT-133 Corona Battle Armor
BT-134 Gray Death Legion Battle Armor
BT-187 Djinn Battle Armor
BT-189 Kobold Battle Armor
BT-198 Tengu Battle Armor
BT-199 Asura Md. Battle Armor
BT-200 Shedu Assault Battle Armor
BT-201 Nephilim Assault Battle Armor
BT-207 Delphyne ProtoMech
BT-209 Se'irim Medium Battle Armor
BT-222 Tau Wraith
BT-223 Tau Zombie
BT-224 Heavy Jump Infantry
BT-237 Recon Infantry
BT-238 VTOL Infantry
BT-239 Jump Support Infantry
BT-245 Heavy Infantry - Firing
BT-260 Sprint Scout VTOL
BT-297 Ares ARS-V1A Hera
BT-299 Ares ARS-V1C Aphrodite
BT-320 Tracked APC
BT-321 Hover APC
BT-364 Gabriel Hovercraft
BT-370 Kurita Infantry (3)
BT-372 Savannah Master Hovercraft
BT-373 Centaur Protomech
BT-374 Roc Protomech
BT-376 Minotaur Protomech
BT-381 Basic Inner Sphere Battle Armor (3)
BT-383 Longinus Battle Armor (3)
BT-384 Achileus Battle Armor (3)
BT-388 Salamander Battle Armor (3)
BT-391 Fenrir Battle Armor (1)
BT-408 Loki II A
BT-413 Marauder Battle Armor
BT-425 Uziel UZL-8S
BT-427 Balac Strike VTOL (Standard) & (LRM)
BT-436 Buraq (Standard) Battle Armor
BT-460 Saxon APC Standard / Laser / HQ
BT-470 Sojourner C
BT-476 Ares ARS-V1E Apollo
FT-015 Lynx LNX-9C
OP-060 Masakari H Right Arm
Tripod Six Pack
battletech #alphastrike #ironwindmetals #battletechalphastrike #miniatures #catalystgamelabs #battlemech #battletechminiatures #battletechpaintingandcustoms #mecha #tabletop #tabletopgames #tabletopgaming #wargaming #wargames #hobby #scifi #sciencefiction #miniaturepainting #mech #hovertank #6mmminis #6mmscifi #feldherr #dougram #gundam #robotech #armypainter #thearmypainter #chessex
4 notes
·
View notes
Text
Me writing QKD
My readers making connections and going crazy with the deep lore of my writing
Me who planned nothing and just typed out whatever random string of words my brain whispered to me today

5K notes
·
View notes
Text
Satellite Optical Ground Station Market Expands Rapidly as Optical Ground Terminals Replace RF Technologies

Market Overview
The Satellite Optical Ground Station Market is undergoing a transformative evolution, powered by advancements in free-space optics, quantum communication, and laser-based data transfer. These ground stations serve as critical communication hubs for satellite systems, enabling high-speed, secure, and interference-resistant data exchange between satellites and Earth. Unlike traditional radio frequency-based systems, optical ground stations offer vastly improved bandwidth and speed, making them ideal for next-generation applications in space research, Earth observation, military defense, and commercial telecommunications.
As global satellite constellations grow in size and complexity, the demand for more efficient and capable ground infrastructure is surging. From low Earth orbit (LEO) satellites to deep space missions, optical ground stations are becoming indispensable components in modern space communication networks.
Click to Request a Sample of this Report for Additional Market Insights:
https://www.globalinsightservices.com/request-sample/?id=GIS25908
Market Dynamics
Several dynamic factors are influencing the growth trajectory of the satellite optical ground station market. A key driver is the increasing number of satellite launches for both commercial and government purposes. The need for faster, more secure communication links is prompting investments in optical ground station infrastructure.
Moreover, rising concerns over cyber threats have led to a heightened interest in Quantum Key Distribution (QKD) and other secure optical communication technologies. These innovations allow for virtually unhackable communications, which is especially crucial in military and defense sectors.
However, the market does face certain challenges. Weather dependency is a significant drawback, as cloud cover and atmospheric conditions can disrupt optical signals. Additionally, the high cost of installation, upgradation, and maintenance of optical stations poses a barrier for small-scale operators.
Still, advancements in hybrid systems and adaptive optics are addressing these challenges, making optical ground stations more reliable and commercially viable.
Key Players Analysis
A number of key players are spearheading innovations and market penetration in the satellite optical ground station space. Companies like Airbus, Thales Alenia Space, Mynaric, Tesat-Spacecom, and Ball Aerospace are leading the charge with cutting-edge products and services. These players are heavily investing in R&D to enhance the performance of transceivers, photodetectors, beam steering devices, and modulators.
Startups and smaller firms are also entering the landscape, contributing specialized components like optical lenses and filters or niche services such as consultation and customized upgradation. This competitive landscape is fueling both innovation and affordability.
Regional Analysis
Geographically, North America dominates the satellite optical ground station market due to substantial government funding, advanced technological ecosystems, and strategic defense initiatives. The United States, in particular, is at the forefront, with a strong presence of space agencies, commercial satellite operators, and defense contractors.
Europe follows closely, with countries like Germany, France, and the UK investing in collaborative projects through the European Space Agency (ESA). The region also benefits from growing commercial interest in optical satellite communication.
Asia Pacific is witnessing rapid growth, driven by increasing satellite launches from China, India, and Japan. The region's expanding space programs and commercial ventures are catalyzing investments in ground-based, ship-based, and airborne optical communication systems.
Latin America and the Middle East & Africa are emerging markets, albeit at a slower pace. These regions are beginning to recognize the benefits of optical communication for national security, remote sensing, and disaster management.
Recent News & Developments
Recent years have seen a flurry of technological breakthroughs and strategic collaborations in the satellite optical ground station industry. For instance, Mynaric and NASA have partnered on multiple deep space laser communication projects. Meanwhile, companies are also exploring hybrid models that combine RF and optical technologies for enhanced reliability.
Another notable development includes the use of Quantum Key Distribution (QKD) in optical ground stations, aiming to provide ultra-secure communications for military and financial data transfers.
The growth in installation and maintenance services further signals a maturing market, with companies offering tailored consultation and upgradation services to meet evolving operational needs.
Browse Full Report @ https://www.globalinsightservices.com/reports/satellite-optical-ground-station-market/
Scope of the Report
The satellite optical ground station market encompasses a wide array of technologies, products, and applications. It includes fixed and mobile optical ground stations, supported by components like beam steering devices and optical filters. Product categories range from transceivers and receivers to modulators and demodulators, while services span installation, maintenance, consultation, and upgradation.
Applications cut across multiple domains—telecommunications, Earth observation, deep space communication, scientific research, and military and defense. Deployment modes vary from ground-based to ship-based and airborne, catering to different mission profiles. The market serves a diverse clientele including government agencies, commercial enterprises, and research institutions.
With increasing reliance on data transmission and signal processing, the satellite optical ground station market is poised for significant growth. As technology continues to evolve and the global demand for secure, high-speed satellite communication increases, this market holds vast potential for innovation, expansion, and long-term sustainability.
Discover Additional Market Insights from Global Insight Services:
Septic Solutions Market:
https://www.globalinsightservices.com/reports/septic-solutions-market/
Artillery Ammunition Market:
https://www.globalinsightservices.com/reports/artillery-ammunition-market/
Concrete Pump Market:
https://www.globalinsightservices.com/reports/concrete-pump-market/
Spring Energized Seals Market:
https://www.globalinsightservices.com/reports/spring-energized-seals-market/
Die Bonder Equipment Market:
https://www.globalinsightservices.com/reports/die-bonder-equipment-market/
0 notes