#cybersecurity in defense
Explore tagged Tumblr posts
Text
World Defense Budgets: Key Players and Regional Spending Trends

The World Defense Budget Analysis Market size is estimated to be USD 2,004.7 billion in 2023 and is expected to reach USD 2,546.9 billion by 2028 at a CAGR of 4.90% from 2023 to 2028. The world defense budget has experienced substantial growth over the years, reflecting the global focus on national security, military modernization, and the evolving nature of security threats. Factors driving the growth of the defense budget include geopolitical tensions, regional conflicts, and the need to address emerging challenges such as cyber warfare and terrorism. Technological advancements and the race for military superiority have also fueled increased defense spending.
Governments across the globe are investing in advanced weaponry, modernizing their armed forces, and adopting cutting-edge technologies like artificial intelligence, unmanned systems, and cyber capabilities. Furthermore, economic growth in certain regions has given governments the financial capacity to allocate more resources to defense. Rising defense budgets are also attributed to the desire to maintain military readiness, support global military operations, and safeguard national interests. However, challenges such as budget constraints, competing domestic priorities, and public scrutiny over defense spending remain. Nevertheless, the growth of the World Defense Budget Analysis Industry is expected to continue as nations navigate the evolving security landscape and strive to ensure their defense capabilities are robust, agile, and well-equipped to address both conventional and unconventional threats.
#world defense budget#defense spending analysis#military budget growth#defense market trends#defense budget forecast#military modernization#cybersecurity in defense#defense market opportunities
0 notes
Text
The Hacker's Guidebook:
Aspiring hackers! I’ve created a guide covering core cybersecurity concepts new hackers should master before tools. I break down networking, OS internals, & hacking tactics. Recognize hacking as lifelong journey—arm yourself with the basics!
Core Concepts for Budding Cybersecurity Enthusiasts The Building Blocks of Ethical Hacking So you want to become an ethical hacker and enter the exciting world of cybersecurity. That’s awesome! However, before you dive headfirst into firing up Kali Linux and hacking everything in sight, it’s vital to build up your foundational knowledge across several InfoSec domains. Mastering the fundamentals…

View On WordPress
#attacking tools#basics of hacking#cross site scripting#Cyber Threat Defense#cybersec#cybersecurity learning#cybersecurity professional#Ethical Hacking#fundamentals#hacking basics#hacking for beginners#hacking guide#hacking networks#hacking web#how to hack#infosec#learn hacking#learn to hack#linux#malware basics#malware for hacking#metasploit#netsec#network hacking#nmap#operating systems#Pentesting#phishing#phishing attacks#Red Team
34 notes
·
View notes
Text
Toward a code-breaking quantum computer
New Post has been published on https://thedigitalinsider.com/toward-a-code-breaking-quantum-computer/
Toward a code-breaking quantum computer
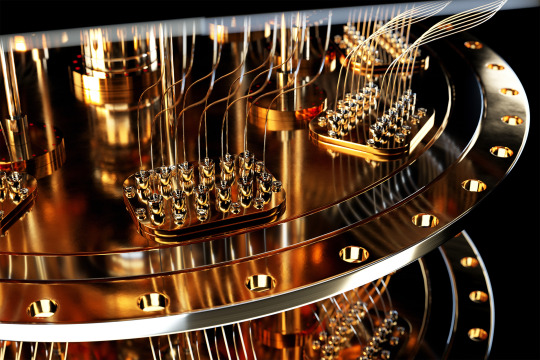
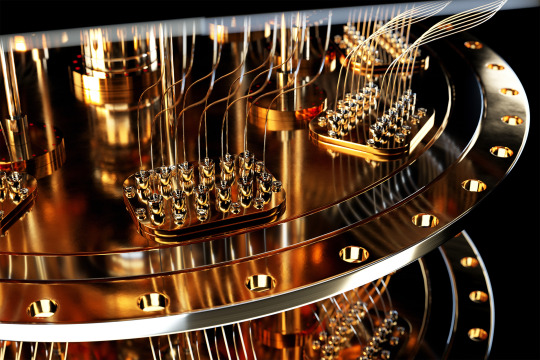
The most recent email you sent was likely encrypted using a tried-and-true method that relies on the idea that even the fastest computer would be unable to efficiently break a gigantic number into factors.
Quantum computers, on the other hand, promise to rapidly crack complex cryptographic systems that a classical computer might never be able to unravel. This promise is based on a quantum factoring algorithm proposed in 1994 by Peter Shor, who is now a professor at MIT.
But while researchers have taken great strides in the last 30 years, scientists have yet to build a quantum computer powerful enough to run Shor’s algorithm.
As some researchers work to build larger quantum computers, others have been trying to improve Shor’s algorithm so it could run on a smaller quantum circuit. About a year ago, New York University computer scientist Oded Regev proposed a major theoretical improvement. His algorithm could run faster, but the circuit would require more memory.
Building off those results, MIT researchers have proposed a best-of-both-worlds approach that combines the speed of Regev’s algorithm with the memory-efficiency of Shor’s. This new algorithm is as fast as Regev’s, requires fewer quantum building blocks known as qubits, and has a higher tolerance to quantum noise, which could make it more feasible to implement in practice.
In the long run, this new algorithm could inform the development of novel encryption methods that can withstand the code-breaking power of quantum computers.
“If large-scale quantum computers ever get built, then factoring is toast and we have to find something else to use for cryptography. But how real is this threat? Can we make quantum factoring practical? Our work could potentially bring us one step closer to a practical implementation,” says Vinod Vaikuntanathan, the Ford Foundation Professor of Engineering, a member of the Computer Science and Artificial Intelligence Laboratory (CSAIL), and senior author of a paper describing the algorithm.
The paper’s lead author is Seyoon Ragavan, a graduate student in the MIT Department of Electrical Engineering and Computer Science. The research will be presented at the 2024 International Cryptology Conference.
Cracking cryptography
To securely transmit messages over the internet, service providers like email clients and messaging apps typically rely on RSA, an encryption scheme invented by MIT researchers Ron Rivest, Adi Shamir, and Leonard Adleman in the 1970s (hence the name “RSA”). The system is based on the idea that factoring a 2,048-bit integer (a number with 617 digits) is too hard for a computer to do in a reasonable amount of time.
That idea was flipped on its head in 1994 when Shor, then working at Bell Labs, introduced an algorithm which proved that a quantum computer could factor quickly enough to break RSA cryptography.
“That was a turning point. But in 1994, nobody knew how to build a large enough quantum computer. And we’re still pretty far from there. Some people wonder if they will ever be built,” says Vaikuntanathan.
It is estimated that a quantum computer would need about 20 million qubits to run Shor’s algorithm. Right now, the largest quantum computers have around 1,100 qubits.
A quantum computer performs computations using quantum circuits, just like a classical computer uses classical circuits. Each quantum circuit is composed of a series of operations known as quantum gates. These quantum gates utilize qubits, which are the smallest building blocks of a quantum computer, to perform calculations.
But quantum gates introduce noise, so having fewer gates would improve a machine’s performance. Researchers have been striving to enhance Shor’s algorithm so it could be run on a smaller circuit with fewer quantum gates.
That is precisely what Regev did with the circuit he proposed a year ago.
“That was big news because it was the first real improvement to Shor’s circuit from 1994,” Vaikuntanathan says.
The quantum circuit Shor proposed has a size proportional to the square of the number being factored. That means if one were to factor a 2,048-bit integer, the circuit would need millions of gates.
Regev’s circuit requires significantly fewer quantum gates, but it needs many more qubits to provide enough memory. This presents a new problem.
“In a sense, some types of qubits are like apples or oranges. If you keep them around, they decay over time. You want to minimize the number of qubits you need to keep around,” explains Vaikuntanathan.
He heard Regev speak about his results at a workshop last August. At the end of his talk, Regev posed a question: Could someone improve his circuit so it needs fewer qubits? Vaikuntanathan and Ragavan took up that question.
Quantum ping-pong
To factor a very large number, a quantum circuit would need to run many times, performing operations that involve computing powers, like 2 to the power of 100.
But computing such large powers is costly and difficult to perform on a quantum computer, since quantum computers can only perform reversible operations. Squaring a number is not a reversible operation, so each time a number is squared, more quantum memory must be added to compute the next square.
The MIT researchers found a clever way to compute exponents using a series of Fibonacci numbers that requires simple multiplication, which is reversible, rather than squaring. Their method needs just two quantum memory units to compute any exponent.
“It is kind of like a ping-pong game, where we start with a number and then bounce back and forth, multiplying between two quantum memory registers,” Vaikuntanathan adds.
They also tackled the challenge of error correction. The circuits proposed by Shor and Regev require every quantum operation to be correct for their algorithm to work, Vaikuntanathan says. But error-free quantum gates would be infeasible on a real machine.
They overcame this problem using a technique to filter out corrupt results and only process the right ones.
The end-result is a circuit that is significantly more memory-efficient. Plus, their error correction technique would make the algorithm more practical to deploy.
“The authors resolve the two most important bottlenecks in the earlier quantum factoring algorithm. Although still not immediately practical, their work brings quantum factoring algorithms closer to reality,” adds Regev.
In the future, the researchers hope to make their algorithm even more efficient and, someday, use it to test factoring on a real quantum circuit.
“The elephant-in-the-room question after this work is: Does it actually bring us closer to breaking RSA cryptography? That is not clear just yet; these improvements currently only kick in when the integers are much larger than 2,048 bits. Can we push this algorithm and make it more feasible than Shor’s even for 2,048-bit integers?” says Ragavan.
This work is funded by an Akamai Presidential Fellowship, the U.S. Defense Advanced Research Projects Agency, the National Science Foundation, the MIT-IBM Watson AI Lab, a Thornton Family Faculty Research Innovation Fellowship, and a Simons Investigator Award.
#2024#ai#akamai#algorithm#Algorithms#approach#apps#artificial#Artificial Intelligence#author#Building#challenge#classical#code#computer#Computer Science#Computer Science and Artificial Intelligence Laboratory (CSAIL)#Computer science and technology#computers#computing#conference#cryptography#cybersecurity#defense#Defense Advanced Research Projects Agency (DARPA)#development#efficiency#Electrical Engineering&Computer Science (eecs)#elephant#email
5 notes
·
View notes
Text
#Tags:Advanced Persistent Threats (APTs)#AI in Cybersecurity#Cloud Security#Cyber Defense Strategies#Cyber Threat Trends 2025#Cybersecurity#Data Breaches#Digital Resilience#facts#Incident Response#IoT Security#life#Malware#Podcast#Ransomware#Ransomware-as-a-Service#serious#straight forward#Threat Intelligence#truth#upfront#website#Worms
1 note
·
View note
Text
GPS Spoofing: New Digital Risk in Civilian Airspace
In 2023, not less than 20 civilian plane flying via the Center East have been misled by their onboard GPS models into flying close to Iranian airspace with out clearance—conditions that would have provoked a world incident. These planes have been victims of GPS spoofing, during which misleading alerts from the bottom, disguised as reliable alerts from GPS satellites in orbit, trick an plane’s…
0 notes
Text
#Zeroday#cybersecurity#AIpowered#defense#machinelearning#Fulcrum Digital#electronicsnews#technologynews
0 notes
Video
youtube
The Biggest Cybersecurity Threat in 2025 - AI-Driven Attacks
0 notes
Text
✌Detailed Analysis of "The Army Operating Concept: Win in a Complex World"
“Strategizing for a Complex World: A depiction of modern military forces engaging in multi-domain operations, navigating hybrid threats, and leveraging advanced technology for global stability.” Read the Original Document at https://t.me/ABOVETOPSECRETXXL/45945 The U.S. Army’s “The Army Operating Concept: Win in a Complex World (TRADOC Pamphlet 525-3-1)” outlines the framework for how the Army…

View On WordPress
0 notes
Text
youtube
#youtube#militarytraining#cybersecurity awards#CIO Awards#Defense Information Systems Agency#Department of Defense#technology awards#cybersecurity#information technology#DOD events#leadership awards#government technology#military technology#defense technology#2024 DOD CIO Awards Ceremony.
0 notes
Text
The Cybersecurity Maturity Model Certification (CMMC) Program – Defense Contractors Must Rapidly Prepare and Implement
The Department of Defense (DoD) has officially launched the Cybersecurity Maturity Model Certification (CMMC) Program, which requires federal contractors and subcontractors across the Defense Industrial Base (DIB) to comply with strict cybersecurity standards. The CMMC program aims to protect Federal Contract Information (FCI) and Controlled Unclassified Information (CUI) in DoD contracts from…
#C3PAOs#CMMC#CMMC Third Party Assessor Organizations#Controlled Unclassified Information#CUI#cyber threats#Cybersecurity Maturity Model Certification#cybersecurity standards#Defense Industrial Base#Department of Defense#DIB#DOD#FAR#FCI#Federal Acquisition Regulation#Federal Contract Information#federal contractors#Subcontractors
0 notes
Text

Playing the NOVA Cybersecurity Lab game was a real eye-opener for me about the challenges and strategies involved in staying safe online. As I went through the different levels, I started to understand that cybersecurity isn’t just about having strong passwords or avoiding shady links—it’s about building a layered defense to keep personal and organizational data safe.
The game took me through a coding challenge, which showed me how even small programming errors can be exploited by attackers, and a password-cracking challenge that made me realize how quickly weak passwords can be cracked. I also learned about social engineering, where attackers try to trick people into giving away sensitive information. This made me see how much of cybersecurity is actually about human psychology and awareness, not just technical skills.
As I earned stars and coins to “buy” defenses for my fictional company, it became clear how important it is to invest in multiple security measures rather than relying on a single line of defense. Overall, the game gave me a practical and more intuitive understanding of cybersecurity, and I now feel more prepared to spot potential threats in my digital life.
1 note
·
View note
Text
10 Essential Security Measures to Protect Your Website from Hackers and Malware
In today’s digital world, keeping your website safe is a big worry for Aussie businesses. Sadly, Australia loses heaps of money every year fixing the damage from hackers1. With 56% of WordPress site attacks coming from old plugins2, it’s clear we need to act fast to protect our online stuff and customer info. This guide gives you 10 key steps to keep your website safe from malware and cyber…
#Cyber Threat Mitigation#Cybersecurity Protection#Hacker Defense Tactics#Malware Prevention Strategies#Web Security Best Practices#Website Security Measures
0 notes
Text
GenAI Is Transforming Cybersecurity
New Post has been published on https://thedigitalinsider.com/genai-is-transforming-cybersecurity/
GenAI Is Transforming Cybersecurity


The cybersecurity industry has always faced an uphill battle, and the challenges today are steeper and more widespread than ever before.
Though organizations are adopting more and more digital tools to optimize operations and increase efficiency, they are simultaneously increasing their attack surface – the extent of vulnerable entry points hackers might exploit – making them more susceptible to rising cyber threats, even as their defenses improve. Even worse, organizations are having to face this rapidly growing array of threats amid a shortage of skilled cybersecurity professionals.
Fortunately, innovations in artificial intelligence, especially Generative AI (GenAI), are offering solutions to some of the cybersecurity industry’s most complex problems. But we’ve only scratched the surface – while GenAI’s role in cybersecurity is expected to grow exponentially in coming years, there remain untapped opportunities where this technology could further enhance progress.
Current Applications and Benefits of GenAI in Cybersecurity
One of GenAI’s most significant areas of impact on the cybersecurity industry is in its ability to provide automated insights that were previously unattainable.
The initial stages of data processing, filtering and labeling are still often performed by older generations of machine learning, which excel at processing and analyzing vast amounts of data, such as sorting through huge sets of vulnerability alerts and identifying potential anomalies. GenAI’s true advantage lies in what happens afterwards.
Once data has been preprocessed and scoped, GenAI can step in to provide advanced reasoning capabilities that go beyond what previous-generation AI can achieve. GenAI tools offer deeper contextualization, more accurate predictions, and nuanced insights that are unattainable with older technologies.
For instance, after a large dataset – say, millions of documents – is processed, filtered and labeled through other means, GenAI provides an additional layer of analysis, validation and context on top of the curated data, determining their relevance, urgency, and potential security risks. It can even iterate on its understanding, generating additional context by looking at other data sources, refining its decision-making capabilities over time. This layered approach goes beyond simply processing data and shifts the focus to advanced reasoning and adaptive analysis.
Challenges and Limitations
Despite the recent improvements, many challenges remain when it comes to integrating GenAI into existing cybersecurity solutions.
First, AI’s capabilities are often embraced with unrealistic expectations, leading to the risk of over-reliance and under-engineering. AI is neither magical nor perfect. It’s no secret that GenAI often produces inaccurate results due to biased data inputs or incorrect outputs, known as hallucinations.
These systems require rigorous engineering to be accurate and effective and must be viewed as one element of a broader cybersecurity framework, rather than a total replacement. In more casual situations or non-professional uses of GenAI, hallucinations can be inconsequential, even comedic. But in the world of cybersecurity, hallucinations and biased results can have catastrophic consequences that can lead to accidental exposure of critical assets, breaches, and extensive reputational and financial damage.
Untapped Opportunities: AI with Agency
Challenges shouldn’t deter organizations from embracing AI solutions. Technology is still evolving and opportunities for AI to enhance cybersecurity will continue to grow.
GenAI’s ability to reason and draw insights from data will become more advanced in the coming years, including recognizing trends and suggesting actions. Today, we’re already seeing the impact advanced AI is having by simplifying and expediting processes by proactively suggesting actions and strategic next steps, allowing teams to focus less on planning and more on productivity. As GenAI’s reasoning capabilities continue to improve and can better mimic the thought process of security analysts, it will act as an extension of human expertise, making complex cyber more efficient.
In a security posture evaluation, an AI agent can act with true agency, autonomously making contextual decisions as it explores interconnected systems—such as Okta, GitHub, Jenkins, and AWS. Rather than relying on static rules, the AI agent dynamically makes its way through the ecosystem, identifying patterns, adjusting priorities, and focusing on areas with heightened security risks. For instance, the agent might identify a vector where permissions in Okta allow developers broad access through GitHub to Jenkins, and finally to AWS. Recognizing this path as a potential risk for insecure code reaching production, the agent can autonomously decide to probe further, focusing on specific permissions, workflows, and security controls that could be weak points.
By incorporating retrieval-augmented generation (RAG), the agent leverages both external and internal data sources—drawing from recent vulnerability reports, best practices, and even the organization’s specific configurations to shape its exploration. When RAG surfaces insights on common security gaps in CI/CD pipelines, for instance, the agent can incorporate this knowledge into its analysis, adjusting its decisions in real time to emphasize those areas where risk factors converge.
Additionally, fine-tuning can enhance the AI agent’s autonomy by tailoring its decision-making to the unique environment it operates in. Typically, fin-tuning is performed using specialized data that applies across a wide range of use cases rather than data from a specific customer’s environment. However, in certain cases such as single tenant products, fine-tuning may be applied to a specific customer’s data to allow the agent to internalize specific security nuances, making its choices even more informed and nuanced over time. This approach enables the agent to learn from past security assessments, refining its understanding of how to prioritize particular vectors, such as those involving direct connections from development environments to production.
With the combination of agency, RAG, and fine-tuning, this agent moves beyond traditional detection to proactive and adaptive analysis, mirroring the decision-making processes of skilled human analysts. This creates a more nuanced, context-aware approach to security, where AI doesn’t just react but anticipates risks and adjusts accordingly, much like a human expert might.
AI-Driven Alert Prioritization
Another area where AI-based approaches can make a significant impact is in reducing alert fatigue. AI could help reduce alert fatigue by collaboratively filtering and prioritizing alerts based on the specific structure and risks within an organization. Rather than applying a blanket approach to all security events, these AI agents analyze each activity within its broader context and communicate with one another to surface alerts that indicate genuine security concerns.
For example, instead of triggering alerts on all access permission changes, one agent might identify a sensitive area impacted by a modification, while another assesses the history of similar changes to gauge risk. Together, these agents focus on configurations or activities that truly elevate security risks, helping security teams avoid noise from lower-priority events.
By continuously learning from both external threat intelligence and internal patterns, this system of agents adapts to emerging risks and trends across the organization. With a shared understanding of contextual factors, the agents can refine alerting in real time, shifting from a flood of notifications to a streamlined flow that highlights critical insights.
This collaborative, context-sensitive approach enables security teams to concentrate on high-priority issues, reducing the cognitive load of managing alerts and enhancing operational efficiency. By adopting a network of agents that communicate and adapt based on nuanced, real-time factors, organizations can make meaningful strides in mitigating the challenges of alert fatigue, ultimately elevating the effectiveness of security operations.
The Future of Cybersecurity
As the digital landscape grows, so does the sophistication and frequency of cyberthreats. The integration of GenAI into cybersecurity strategies is already proving transformative in meeting these new threats.
But these tools are not a cure-all for all of the cyber industry’s challenges. Organizations must be aware of GenAI’s limitations and therefore take an approach where AI complements human expertise rather than replaces it. Those who adopt AI cybersecurity tools with an open mind and strategic eye will help shape the future of industry into something more effective and secure than ever before.
#agent#agents#ai#ai agent#AI AGENTS#alerts#Analysis#anomalies#applications#approach#artificial#Artificial Intelligence#assets#Attack surface#AWS#CI/CD#code#collaborative#cyber#Cyber Threats#cybersecurity#cybersecurity framework#cybersecurity tools#data#data processing#data sources#defenses#detection#developers#development
0 notes
Text
#CISA#Critical Infrastructure Protection#Cyber Defense#Cyber Incident Response#Cyber Threats#Cybersecurity#Cybersecurity Framework#facts#Government Policy#life#National Cyber Incident Response Plan#National Cyber Strategy#Podcast#Public-Private Collaboration#Ransomware#serious#straight forward#truth#upfront#website
0 notes
Text
Defending the Digital Realm: The Critical Role of Cybersecurity

In today’s highly connected digital age, cybersecurity has shifted from a secondary concern to a top priority. As cyber threats continue to rise in both volume and complexity, individuals, businesses, and governments alike face unprecedented risks, including severe data breaches, financial losses, and damage to their reputations. The need for robust cybersecurity practices has never been more pressing. With that in mind, here are some essential strategies to help safeguard your digital assets.
To start, encouraging the creation of strong passwords can motivate readers to take that critical first step in securing their accounts. A combination of letters, numbers, and symbols creates a powerful first line of defense against unauthorized access.
Phishing scams are another significant threat in today’s digital landscape. These schemes are designed to trick people into sharing sensitive information. By helping readers recognize the warning signs of these increasingly advanced scams, you can equip them to navigate the digital world more safely.
Additionally, emphasizing the importance of regular software updates and reliable antivirus protection is vital. These measures help close security gaps and bolster defenses against potential cyber threats. By stressing the necessity of strong passwords, a keen awareness of phishing scams, and the habit of keeping software up to date, we can significantly enhance our digital security.
Ultimately, knowledge and proactive measures are our best tools for safely navigating the ever-evolving cyber landscape. Remember, vigilance and awareness are essential to staying secure in today’s digital world.
#Cybersecurity solutions#Data protection#Network security#Cyber threat detection#Security software#IT security services#Cyber defense#Threat prevention#Secure business solutions#Cybersecurity experts
0 notes
Video
youtube
The AI Honeypot - A Modern Reality in Cybersecurity
#youtube#Cybersecurity AI Honeypot Hackers Technology Defense Labyrinth Networks Hacking Innovation insight
0 notes