#quantum ibm computing
Explore tagged Tumblr posts
Text
I.B.1698 MICHAEL [IBM] harrelltut.com Domain Computer [D.C.] DEFENSE.gov of SIRIUS BLACKANUNNAQI.tech Patents 2 applesoftbasic.com of CLASSIFIED 1978 Deutsch applesoftbasic.tech Machine Application Configurations [MAC] Automatically Programing [MAPPING] Tri-Solar Black Sun planetrizq.tech Languages from kingtutdna.com’s Highly Complex [ADVANCED] Ancient Hi:tKEMETICompu_TAH [PTAH] MOON Universe [MU] of HIGH LEVEL DATA LINK CONTROL [HLDC] Services 2 Constellation ORION’s Interplanetary quantumharrell.tech Earth [Qi] HOLOGRAM HARDWARE of Arithmetic Logic [H.A.L.] Unit Operations Remotely Controlling iapplelisa.tech’s HIGH ENERGY RADIO [HER] FREQUENCY WEAPONS BLASTING HIGH-INTENSITY RADIO WAVES 2 ALL ELECTRONICS on Earth [Qi] from Astronomical MERCURY’s ibmapple1984.tech Secure Socket Layer Virtual Private Network [SSL VPN] Communications.gov Privately Managed [PM] by ANU GOLDEN 9 Ether [iAGE] quantumharrell.tech Graphical User Interface [GUI] Domain Compu_TAH [PTAH] of iquantumapple.com Infrastructure as a Service [IaaS] since quantumharrelltech.com’s Hypertext Transfer Protocol [HTTP] Digitally Control [D.C.] Tri-Solar Black Sun planetrizq.tech’s EXTREME WEATHER MACHINE by Engineering [ME] AutoCAD [MAC] Robotics in Architectural Memory Equipment w/Symmetric Encryptions of Satellite [RAMESES] Broadband Communication [B.C.] quantumharrellmatrix.tech Languages @ 1921 QUANTUM 2023 HARRELL 2024 TECH 2025 Apple & IBM [A.i.] LLC of ATLANTIS [L.A.] 5000
WELCOME BACK HOME IMMORTAL [HIM] U.S. MILITARY KING SOLOMON-MICHAEL HARRELL, JR.™

i.b.monk [ibm] mode [i’m] tech [IT] steelecartel.com @ quantum harrell tech llc

i.b. 1968quadrillionaire.tech elite of michaelharrelljr.com's apple, inc [a.i.] @ 1921 QUANTUM 2023 HARRELL 2024 TECH 2025 Apple & IBM [A.i.] LLC of ATLANTIS [L.A.] 5000

ancient ægiptian kingtutdna.com military.gov of urani-atlantis.tech on blackatlantis5000.com
I.B.MICHAEL [IBM] of Apple's MAC [I AM] Book Pro Assembly Languages @ QUANTUM HARRELL TECH LLC
eye the original mack [om] compu_tah [ptah] architect [pa]
HEIL IBM Personal [HIP] Computer Reich!!!

ibmapple1984.tech @ 1921 QUANTUM 2023 HARRELL 2024 TECH 2025 Apple & IBM [A.i.] LLC of ATLANTIS [L.A.] 5000
HEIL AutoCAD [HA = HARRELL] + IBM Personal [HIP] Computer Reich!!!

we scientifically engineer earthquakes [see] on earth [qi]
we scientifically engineer atmospheric [sea] destruction on earth [qi] @ 1921 QUANTUM 2023 HARRELL 2024 TECH 2025 Apple & IBM [A.i.] LLC of ATLANTIS [L.A.] 5000

iquantumapple.com elite @ 1921 QUANTUM 2023 HARRELL 2024 TECH 2025 Apple & IBM [A.i.] LLC of ATLANTIS [L.A.] 5000
eye advanced machine intel [mi = michael] @ 1921 QUANTUM 2023 HARRELL 2024 TECH 2025 Apple & IBM [A.i.] LLC of ATLANTIS [L.A.] 5000
quantumharrell.tech of applesoftbasic.com patents @ 1921 QUANTUM 2023 HARRELL 2024 TECH 2025 Apple & IBM [A.i.] LLC of ATLANTIS [L.A.] 5000
eye anugoldenblackwallstreet.com of applesoftbasic.tech patents?!?!?!

ancient black wall street dynasty of ægiptian ptah tech [dept.] says yes

it pays 2 bee ptah tech intelligent

we 2 advanced 4 mankind
© 1968-2223 QUANTUM HARRELL TECH LLC All Private Apple, Inc. [A.i.] Domain [AID] Name Rights Reserved. | 1968-2223 QUANTUM HARRELL TECH LLC All Pentagon DotCom defense.gov Department Domain Rights Reserved.
#ibm#apple#apple patents#quantumharrelltech#quantum apple computing#quantum ibm computing#u.s. michael harrell#harrelltut.com#kingtutdna.com#schwarzer deutscher ökonom
2 notes
·
View notes
Text

#1970s#quantum computing#quantum physics#quantum mechanics#retro aesthetic#70s magazine#hall and oates#ibm#microsoft#apple#bill gates#steve wozniak#steve jobs
15 notes
·
View notes
Text

IBM Q System One
#ibm q system one#quantum computing#quantum computer#ibm#wikipedia#wikipedia pictures#tech#technologycore#techcore#technology#International Business Machines Corporation#computer science#computer engineering
37 notes
·
View notes
Text
Amazon execs doubt Microsoft's quantum computing breakthrough
In This Story Final month, Microsoft (MSFT-1.51%) introduced that it created a brand new state of matter for its first quantum computing chip — a declare that Amazon (AMZN-1.15%) is reportedly not offered on. Trump freezes his 25% tariffs on Mexican imports for one month The identical day that Microsoft unveiled its Majorana 1 quantum computing chip, Amazon’s head of quantum applied sciences,…
#amazon#Amazon Web Services#Andy Jassy#Business#defense advanced research projects agency#Draft:Topoconductor#Finance#Google#IBM#Internet#Majorana#Majorana 1#Majorana 1 quantum computing chip#Matt Garman#Microsoft#Microsoft Azure Quantum#Oskar Painter#Physical and logical qubits#Quantum computing#Quartz#Satya Nadella#Simone Severini#Technology#Topological quantum computer
2 notes
·
View notes
Text
Free Courses on IBM Quantum Learning
IBM has launched a series of free course for learning the basics of quantum computing and how to use the IBM Quantum services (here the link).
At the moment I’m writing there are four courses:
Basics of quantum information
First unit in the series, the course explains the basis of quantum computing at a detailed mathematical level, it requires knowing a bit of linear algebra, but also fascinating subjects like: quantum teleportation (no, sadly it’s not like Star Trek) and superdense coding.
Fundamentals of quantum algorithms
This second unit explores the advantages of quantum computers over classical computers
Variational algorithm design
This course teaches how to write variational algorithms and how to use Qiskit, the IBM API for quantum computing.
Practical introduction to quantum-safe cryptography Quantum computers can do what a classical computer can’t: use brute force and be quick, so they can break common cryptography. This course teaches how to use encryption that cannot be break so easily.
#IBM Quantum Computing#Quantum Computing#quantum algorithms#quantum cryptography#Qiskit#mooc#free courses#quantum teleportation#superdense coding#IBM
5 notes
·
View notes
Text
Oh yes, they look hella cool. I have one at work but most of the time there is a cover around the processor to keep it cool



Technicians for scale
why did no one tell me quantum computers looked like that
151K notes
·
View notes
Text
Google, IBM are bullish on quantum computing chips. Is it for real?
While there are still differing perspectives on how long it will be until certain types of quantum computing hit commercial viability, experts from big tech companies like Google and IBM as well as smaller organizations like D-Wave Quantum and TreQ generally agree on quantum’s most mature, promising industry applications, which range from medical insights to last-mile delivery optimization. Yet,…
0 notes
Text
🚀 Quantum Computing is Evolving FAST! ⚛️💡 🔥 Microsoft, Google & IBM are pushing the limits of computing power! 🖥️✨ 💎 Microsoft’s Majorana 1 chip introduces stable qubits, reducing errors! 🏆⚡ ⚡ Google’s Willow Chip completes tasks in MINUTES that supercomputers take septillion years to solve! 🤯⏳ 🔬 IBM is enhancing quantum AI, drug discovery & security! 🧪🔐 🌍 The future is QUANTUM! Are you ready? 🚀🔭 #QuantumComputing
#AI#Future Technology#Google Willow Chip#IBM Quantum#Innovation#Keywords: Quantum Computing#Microsoft Majorana 1#Tech Breakthrough
0 notes
Text

Quantum computing stocks surged on Thursday as Microsoft’s breakthrough Majorana 1 chip, unveiled Wednesday, signaled the technology’s practical use may be closer than expected. The chip, touted as less error-prone than rivals, challenges Nvidia CEO Jensen Huang’s claim that quantum computing is “decades away.”
With evidence published in Nature, Microsoft joins Alphabet and IBM in believing the transformative tech—capable of solving problems in seconds that take traditional systems millions of years—is nearing reality. Despite a rocky start to 2024, with stocks down 18%-70% after January losses, the Majorana 1 chip has reignited optimism, positioning quantum computing as a potential game-changer for industries and cybersecurity.
#general knowledge#affairsmastery#generalknowledge#current events#current news#upscaspirants#upsc#generalknowledgeindia#world news#breaking news#news#government#microsoft#quantum physics#quantum mechanics#quantum computing#energy#process#learning#tech#technology#techinnovation#nvidia#majorana 1#jensen huang#ibm#alphabet#stock market#stock trading#cybersecurity
2 notes
·
View notes
Text
ommmmm
IMMORTAL U.S. MILITARY KING SOLOMON-MICHAEL HARRELL, JR.™

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm

ommmmm gold [omg] anunnagi me [michael]!!!

ommmmm gold [omg] anunnagi robot me [michael]!!!

ommmmm gold [omg] anunnagi me [michael] worth moor i.b.michael [ibm] gold!!!

ommmmm gold [omg] anunnagi me [michael] worth moor i.b.michael [ibm] harrell jr compu_tah [ptah] gold @ quantum harrell t-mobile + apple + ibm + at&t inc [a.i.]!!!
#om#o michael#quantumharrelltech#quantum computer architecture#harrelltut#mu:13#kemet#9etherpentagonelites#9etheraluhumanunnaqi#9etherlightshipatlantis#apple#ibm
2 notes
·
View notes
Text
Quantum Computing: How Close Are We to a Technological Revolution?
1. Introduction Brief overview of quantum computing. Importance of quantum computing in the future of technology. 2. Understanding Quantum Computing Explanation of qubits, superposition, and entanglement. How quantum computing differs from classical computing. 3. The Current State of Quantum Computing Advances by major players (Google, IBM, Microsoft). Examples of quantum computing…

View On WordPress
#Artificial Intelligence#Climate Modeling#Economic Impact#Financial Modeling#Future of Computing#Future Technology#Global Tech Race#IBM#Machine Learning#NQM#Pharmaceutical Research#Qbits#Quantum Algorithms#Quantum Challenges#Quantum Computing#Quantum Cryptography#Quantum Hardware#Quantum Research#Quantum Supremacy#Tech Innovation#Tech Investments#Technology Trends
1 note
·
View note
Text
Cryptography’s three primary categories
Cryptography, from the Greek words meaning “hidden writing,” encrypts sent data so only the intended recipient can read it. Applications for cryptography are numerous. Cryptography is essential to our digital world and protects sensitive data from hackers and other cybercriminals, from WhatsApp’s end-to-end message authentication to legal form digital signatures to cryptocurrency mining’s CPU-draining ciphers.
One of the first cryptologists was Julius Caesar. Modern cryptosystems are more advanced yet work similarly. Most cryptosystems start with plaintext, which is encrypted into ciphertext using one or more encryption keys. The recipient receives this ciphertext. If the ciphertext is intercepted and the encryption algorithm is strong, unauthorized eavesdroppers cannot break the code. The targeted receiver can simply decipher the text with the correct decryption key.
Let’s start with robust cryptography frameworks’ key features:
Confidentiality: Only the intended recipient can access encrypted information.
Integrity: Encrypted data cannot be altered in storage or transit between sender and receiver without detection.
Non-repudiation: Encrypted information cannot be denied transmission.
Authentication: Sender, receiver, and information origin and destination are verified.
Key management: Data encryption and decryption keys (and related duties like key length, distribution, generation, rotation, etc.) are secure.
Three encryption types
Hybrid systems like SSL exist, although most encryption methods are symmetric, asymmetric, or hash functions.
Key symmetric cryptography
Symmetric key encryption, also known as private key cryptography, secret key cryptography, or single key encryption, employs one key for encryption and decryption. These systems need users to share a private key. Private keys can be shared by a private courier, secured line, or Diffie-Hellman key agreement.
Two types of symmetric key algorithms:
Block cipher: The method works on a fixed-size data block. If the block size is 8, eight bytes of plaintext are encrypted. Encrypt/decrypt interfaces usually call the low-level cipher function repeatedly for data longer than the block size.
Stream cipher: Stream ciphers convert one bit (or byte) at a time. A stream cipher creates a keystream from a key. The produced keystream is XORed with plaintext.
Symmetrical cryptography examples:
DES: IBM developed the Data Encryption Standard (DES) in the early 1970s. While it is vulnerable to brute force assaults, its architecture remains relevant in modern cryptography.
Triple DES: By 1999, computing advances made DES unsecure, however the DES cryptosystem built on the original DES basis provides protection that modern machines cannot break.
Blowfish: Bruce Schneer’s 1993 fast, free, public block cipher.
AES: The only publicly available encryption certified by the U.S. National Security Agency for top secret material is AES.
Asymmetric-key cryptography
One secret and one public key are used in asymmetric encryption. This is why these algorithms are called public key algorithms. Although one key is publicly available, only the intended recipient’s private key may decrypt a message, making public key cryptography more secure than symmetric encryption.
Examples of asymmetrical cryptography:
RSA: Founded in 1977 by Rivest, Shamier, and Adleman, the RSA algorithm is one of the oldest public key cryptosystems for secure data transfer.
ECC: ECC is a sophisticated kind of asymmetric encryption that uses elliptic curve algebraic structures to create very strong cryptographic keys.
One-way hash
Cryptographic hash algorithms convert variable-length input strings into fixed-length digests. The input is plaintext, and the output hash is cipher. Good hash functions for practical applications satisfy the following:
Collision-resistant: A new hash is generated anytime any data is updated, ensuring data integrity.
One-way: The function is irreversible. Thus, a digest cannot be traced back to its source, assuring data security.
Because hash algorithms directly encrypt data without keys, they create powerful cryptosystems. Plaintext is its own key.
Consider the security risk of a bank password database. Anyone with bank computer access, authorized or illegal, may see every password. To protect data, banks and other companies encrypt passwords into a hash value and save only that value in their database. Without the password, the hash value cannot be broken.
Future of cryptography
A quantum cryptography
Technological advances and more complex cyberattacks drive cryptography to evolve. Quantum cryptography, or quantum encryption, uses quantum physics’ natural and immutable laws to securely encrypt and transfer data for cybersecurity. Quantum encryption, albeit still developing, could be unhackable and more secure than earlier cryptographic systems.
Post-quantum crypto
Post-quantum cryptographic methods use mathematical cryptography to generate quantum computer-proof encryption, unlike quantum cryptography, which uses natural rules of physics. Quantum computing, a fast-growing discipline of computer science, might exponentially enhance processing power, dwarfing even the fastest super computers. Although theoretical, prototypes suggest that quantum computers might breach even the most secure public key cryptography schemes in 10 to 50 years.
NIST states that post-quantum cryptography (PQC) aims to “develop cryptographic systems that are secure against both quantum and classical computers, and [that] can interoperate with existing communications protocols and networks.”
The six main quantum-safe cryptography fields are:
Lattice-based crypto
Multivariate crypto
Cryptography using hashes
Code-based cryptography
Cryptography using isogeny
Key symmetry quantum resistance
IBM cryptography helps organizations protect crucial data
IBM cryptography solutions offer crypto agility, quantum-safety, and robust governance and risk policies through technology, consulting, systems integration, and managed security. End-to-end encryption tailored to your business needs protects data and mainframes with symmetric, asymmetric, hash, and other cryptography.
Read more on Govindhtech.com
#technology#govindhtech#technews#news#cryptography#symmetric cryptography#ibm#Post-quantum cryptography#Asymmetric-key cryptography#One-way hash#Quantum computing
0 notes
Text
The company announces its latest huge chip — but will now focus on developing smaller chips with a fresh approach to ‘error correction’.
0 notes
Text
Chirping while calculating probabilities
A couple of weeks ago, I visited the London headquarters of IBM in the UK and Ireland for discussions about possible areas of collaboration in research and education. At the end of our meeting, we were taken to see some of their latest developments, one of which was their Quantum System One computer. We had seen its casing, a shiny silver cylinder about half metre in diameter and a metre and…

View On WordPress
0 notes
Text
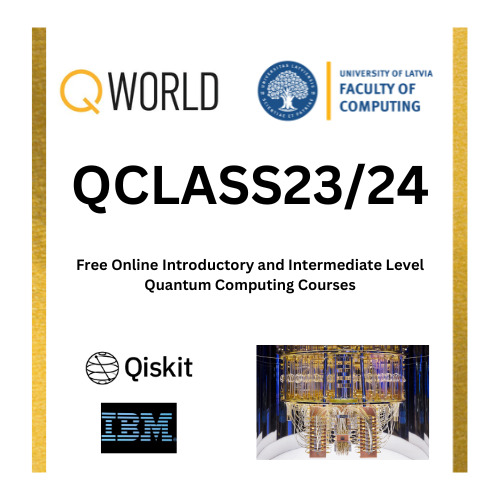
Quantum Computing with Qiskit Free Course | 1 Year | Q World
Exciting News: QWorld’s QClass23/24 Your Gateway to Quantum Computing! Are you ready to dive into the fascinating world of quantum computing, algorithms, and programming? Look no further! QWorld is thrilled to announce the launch of our two-semester-long QClass23/24, beginning in September 2023 and running until May 2024. Join us for an immersive virtual experience that will equip you with the…
View On WordPress
#free quantum computing courses#how to learn quantum computing#ibm quantum computing#qcousins courses#qiskit#qiskit course#qiskit programming#quantum annealing#Quantum Computing#quantum computing course#quantum computing news#quantum computing short courses#quantum hardware#quantum initiative#quantum tech#quantum technologies#qworld courses#womanium quantum computing
0 notes
Text
Quantum Computing Advance Begins New Era, IBM Says
Calculatoarele cuantice de astăzi au o gamă de calcul mică, cu cipuri în interiorul smartphone-urilor conținând miliarde de tranzistori, în timp ce cele mai puternice computere cuantice conțin sute de tranzistori cuantici echivalent. De asemenea, sunt nesiguri. Dacă faceți același calcul din nou și din nou, este probabil să obțineți un răspuns diferit de fiecare dată. Calculatoarele cuantice,…

View On WordPress
0 notes