#Cryptography
Explore tagged Tumblr posts
Text
Hey, cryptographers of Tumblr. If anyone is bored and fancies a challenge, please could you have a go at deciphering this message and tell me how long it takes you? It's for a fic I'm writing, and I need to know if it's realistic for my characters to get the answer late enough for my pacing but quick enough to catch the killer.

253 notes
·
View notes
Note
----- .---- ----- .---- ----- ----- ----- .---- / ----- .---- .---- .---- ----- .---- ----- .---- / ----- .---- .---- ----- ----- .---- ----- .---- / ----- .---- .---- ----- ----- .---- ----- .---- / ----- .---- .---- ----- .---- .---- .---- ----- / ----- ----- .---- ----- ----- .---- .---- .---- / ----- .---- .---- .---- ----- ----- .---- .---- / ----- ----- .---- ----- ----- ----- ----- ----- / ----- ----- .---- .---- .---- ----- ----- ----- / ----- .---- .---- .---- ----- .---- ----- ----- / ----- .---- .---- ----- .---- ----- ----- ----- / ----- ----- .---- ----- ----- ----- ----- ----- / ----- .---- .---- ----- ----- ----- ----- .---- / ----- .---- .---- ----- .---- .---- ----- ----- / ----- .---- .---- ----- ----- ----- .---- ----- / ----- .---- .---- .---- ----- .---- ----- .---- / ----- .---- .---- ----- .---- .---- ----- .----
Well played anon, well played.
I will not translate for y’all, but protip, get a morse to text decoder, and then a binary to text decoder.
Figure it out for yourself.
It’ll be more impactful that way.
#rickroll answers#anon#cognitohazard#infohazard#morse code#binary#cryptography#tumblr games#silly#txt#unicode#ascii#not a rickroll
125 notes
·
View notes
Text
BILL'S CONTRACT FINE PRINT DECIPHERED
I'm sure someone has beat me to this, but because I decided to decipher/translate all 1000ish words of the fine print on this here totally normal contract (by hand)

Bold code is theraprism substitution cipher, the rest is the author's substitution cipher, i've reformatted the text to be more readable but i've also made a version with the more accurate, original line formatting here
YOU ARE NOW TWENTY ONE GRAMS LIGHTER
THIS CONTRACT IS LEGAL AND BINDING, WE RESERVE THE RIGHT TO USE YOUR LIKENESS, FACE, VOICE AND SMALL TOWN PLUCK IN WHATEVER NEFARIOUS MANNER IS DEEMED NECESSARY.
SANS SOUL YOUR SOULMATE WILL NOT RECOGNIZE YOU AND WILL WALK RIGHT PAST YOU ON A COLD AUTUMN DAY, NEVER MAKING EYE CONTACT, NOT EVEN PROCESSING THAT YOU HAVE EYES AT ALL. NO AMOUNT INTERACTION WILL MOVE THEM TO A PLACE WHERE THEY CAN REMEMBER - IN FEELING THE THOUSANDS OF LIFETIMES YOU HAVE ALREADY SPENT TOGETHER, EACH TIME CHOOSING WHATEVER FORM WOULD KEEP YOU CLOSEST LIKE OTTERS HOLDING HANDS IN A TUMULTUOUS RIVER. YOU WERE BIRDS, YOU WERE TREES WITH ROOTS ENTWINED, DRINKING IN THE SUNLIGHT TOGETHER. WHEREVER WE GO NEXT, WHATEVER YOU CHOOSE, I WILL ALWAYS BE RIGHT THERE WITH YOU. -
THATS DONE BUDDY, CONGRATULATIONS YOU HAVE CHOSEN BILL INSTEAD.
MCDONALDS RESERVES THE RIGHT TO PUT A GIANT YELLOW M ON YOUR TORSO AND FOREHEAD AND SEND YOU WALKING THROUGH A CROWDED TIMES SQUARE WHILE YOU SCREAM “THE FRIES, THE FRIES, THEY DON'T DEGRADE IN NATURE… ITS AN IMMORTAL FOOD… THEY WILL BE IN THE LANDFILLS LONG PAST OUR DEATHS.”
GOOD GOD, THE THINGS S I’VE SEEN, ME. WHO AM I? OH BILL'S PREVIOUS LAWYER, HE PUT MY SOUL INTO A QUILL PEN SO I CAN WRITE HIS LEGAL DOCUMENTS UNTIL THE SUN SNUFFS OUT LIKE A CANDLE IN THIS SICK UNIVERSE. I USED TO BE SO HOT. I WAS SO FINE. NOW I'M FINE PRINT.
SPEAKING OF WHICH, BILL RESERVES THE RIGHT TO PUT YOUR SOUL INTO AN INANIMATE OBJECT, A STRANGE CREATURE, A CONCEPT, A SENTENCE, A TASTEFUL BUT RUSTIC MASON JAR WITH WILDFLOWERS IN IT.
IF AT ANY POINT YOU WISH TO HAVE VISITATION RIGHTS WITH YOUR SOUL YOU WILL BE SWIFTLY DENIED UNLESS YOU HAD A COOL DAY PLANNED FOR THE BOTH OF YOU, THEN BILL MIGHT COME ALONG.
BY SIGNING THIS DOCUMENT YOU FORFEIT ANY RIGHTS TO EATING SOUL FOOD, IT WILL TURN TO ASH IN YOUR MOUTH, A FITTING PUNISHMENT FOR A FOOL WHO SQUANDERED THE ONLY TRUE GIFT LIFE OWES YOU.
BILL RESERVES THE RIGHT TO DRESS YOUR SOUL HOWEVER HE DEEMS NECESSARY, ESPECIALLY IF YOUR SOUL WAS A NERD BEFORE ACQUISITION, SOUL MAKEOVERRR!
YOUR SOUL MAY BECOME FRACTURED AND PLACED INTO DIFFERENT OBJECTS. THIS HAS NO PURPOSE AND WILL NOT RESURRECT YOU WHEN YOU DIE.
SIGNEE HAS FORFEITED ALL RIGHTS OF ANY AFTERLIFE INCLUDING BUT NOT LIMITED TO: HEAVEN, HELL, PURGATORY, BIG CORNER, FLOW STATE, THE DREAM HOUSE, THE REINCARNATION PROCESSING CENTER, AXOLOTL'S TANK AND CONSEQUENCES HOLE.
SIGNEE CAN NO LONGER BOARD THE SOUL TRAIN AND IS ADVISED TO DISCARD ALL BELLBOTTOMS.
SIGNEE CAN NO LONGER HAVE A PUPPY AS A BEST FRIEND, THEY CAN SENSE WHAT IS GONE. CATS ARE INDIFFERENT.
SIGNEE MAY EXPERIENCE OCCASIONAL DEMON POSSESSION FROM HORCULUS THE RED, PLABOS THE MERCILESS, MORBUS SON OF MORTEM, PLAGA THE OOZING AND OTHER SUCH COMMON DEMONS ROAMING EARTH SEARCHING FOR WEAKENED/EMPTY VESSELS.
TIPS FOR RIPPING YOUR SOUL OUT: WATCHING YOUTUBE COMMENTARY CHANNELS, ATTENDING AN EXTENDED FAMILY EVENT WITH AN OPEN BAR, USING GENERATIVE AI AND ASSERTING THAT YOU ARE CREATIVE, TURNING A BLIND EYE TO HUMAN SUFFERING, AMASSING MORE WEALTH THAN NEEDED, PURCHASING A BLUE CHECKMARK.
#gravity falls#this is not a website dot com#thisisnotawebsitedotcom#bill cipher#the book of bill#cryptography#i like how it just turns into alex ranting near the end brennan lee mulligan style#also “i was fine. now i'm fine print.” took me out#also 21 grams experiment mentioned??#lmk if theres any mistakes the lines bled together when reading a lot
63 notes
·
View notes
Text
Branch Runes
Cipher:
left branches of the tree stand for the row
right branches of the tree stand for the column


#runes#runic#futhark#younger futhark#norse#norse paganism#heathen#heathenry#cryptography#calligraphy
110 notes
·
View notes
Text
LJS 51 is a 15th century collection of encrypted correspondence between the compiler and various correspondents. It is written using approximately 150 invented alphabets, accompanied by transcriptions of the letters in Arabic.
🔗:
46 notes
·
View notes
Text
FUCK YOU MEAN NOBODY KNOWS VIGENERE CIPHERS DUDE LIKE????
okay. so. in a college class we were in groups of 3 and we were supposed to encode a message in a way where we would write a key on another paper and without that key it was not solvable.
so I. of course. made a vigenere cipher with my group. because??? that's like???? the most obvious answer??????
WELL APPARENTLY NOT! THE OTHER GROUP COULDNT DECODE IT, THEY DIDNT FUCKING KNOW WHAT TO DO WITH IT! WE GAVE EM THE FUCKING TABLE FOR IT, THE KEY.
THEY NEVER HEARD OF IT!
BRO WE ARE ALL STUDYING INFORMATICS THE FUCK YOU MEAN YALL DONT KNOW WHAT A VIGENERE IS? MY ART-SCHOOL ROOMMATE KNEW WHAT IT WAS!
#irl stuff#cryptography#person watched gravity falls and suddenly thinks shit like this is normal#fuck me ig#im reblogging this with an image of dipper#i think this is something he would say
32 notes
·
View notes
Text
"In December 2013, a curator and archaeologist purchased an antique silk dress with an unusual feature: a hidden pocket that held two sheets of paper with mysterious coded text written on them. People have been trying to crack the code ever since, and someone finally succeeded: University of Manitoba data analyst Wayne Chan. He discovered that the text is actually coded telegraph messages describing the weather used by the US Army and (later) the weather bureau. Chan outlined all the details of his decryption in a paper published in the journal Cryptologia. [...]


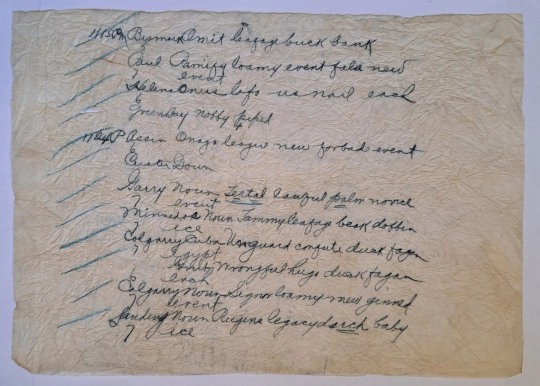
When Rivers-Cofield turned the dress inside-out, she found a small hidden pocket. Many women's dresses of the era had pockets, but this one would only be accessible by hiking up the overskirt. She puzzled over why anyone would make a pocket so inaccessible and thought it might have been used to smuggle messages. Hidden inside, she found two sheets of wadded-up translucent paper measuring about 7.5 inches by 11 inches. The text on each sheet consisted of 12 lines of recognizable common English words—except they made no sense. "Bismark omit leafage buck bank"? "Paul Ramify loamy event false new event"? [...]
With the invention of the telegraph, "For the first time in history, observations from distant locations could be rapidly disseminated, collated, and analyzed to provide a synopsis of the state of weather across an entire nation," Chan wrote in his paper. But it was expensive to send telegrams since companies charged by the word, so codes were developed to condense as much information into as few words as possible.

The challenge was figuring out which code book had been used since, otherwise, it would be nearly impossible to decode the message. Chan perused some 170 telegraphic code books, finally coming across a section about signals used by the US Army Signal Corps that were similar to the pages found in the antique silk dress. Eventually, he realized that the words were codes used by weather stations in the US and Canada to condense telegraph messages about meteorological observations. He relied on old maps to narrow the date to May 27, 1888."
Mysteries remain: who was the owner of the silk dress (a telegraph operator?), and why would she keep these papers in a hidden pocket?
108 notes
·
View notes
Note
can you actually talk about bitwarden / password managers, or direct me to a post about them? Idk my (completely uneducated) instinct says that trusting one application with all your passwords is about as bad as having the same password for everything, but clearly that isn’t the case.
So it is true that online password managers present a big juicy target, and if you have very stringent security requirements you'd be better off with an offline password manager that is not exposed to attack.
However, for most people the alternative is "reusing the same password/closely related password patterns for everything", the risk that one random site gets compromised is much higher than the risk that a highly security focussed password provider gets compromised.
Which is not to say it can't happen, LastPass gets hacked alarmingly often, but most online password managers do their due diligence. I am more willing to stash my passwords with 1Password or Bitwarden or Dashlane than I am to go through the rigamarole of self-managing an array of unique passwords across multiple devices.
Bitwarden and other password managers try to store only an encrypted copy of your password vault, and they take steps to ensure you never ever send them your decryption key. When you want a password, you ask them for your vault, you decrypt it with your key, and now you have a local decrypted copy without ever sending your key to anyone. If you make changes, you make them locally and send back an encrypted updated vault.
As a result, someone who hacks Bitwarden should in the absolute worst case get a pile of encrypted vaults, but without each individuals' decryption key those vaults are useless. They'd still have to go around decrypting each vault one by one. Combining a good encryption algorithm, robust salting, and a decent key, you can easily get a vault to "taking the full lifetime of the universe" levels on security against modern cryptographic attacks.
Now there can be issues with this. Auto-fill can be attacked if you go onto a malicious website, poorly coded managers can leak information or accidentally include logging of passwords when they shouldn't, and obviously you don't know that 1Password isn't backdoored by the CIA/Mossad/Vatican. If these are concerns then you shouldn't trust online password managers, and you should use something where you remain in control of your vault and only ever manually handle your password.
Bitwarden is open source and fairly regularly audited, so you can be somewhat assured that they're not compromised. If you are worried about that, you can use something like KeePassXC/GNU Pass/Himitsu/ (which all hand you the vault file and it's your job to keep track of it and keep it safe) or use clever cryptographic methods (like instead of storing a password you use a secret key to encrypt and hash a reproducible code and use that as your password, e.g. my netflix password could be hash(crypt("netflixkalium", MySecretKey)), I know a few people who use that method.
Now with any luck because Apple is pushing for passkeys (which is just a nice name for a family of cryptographic verification systems that includes FIDO2/Webauthn) we can slowly move away from the nightmare that is passwords altogether with some kind of user friendly public key based verification, but it'll be a few years before that takes off. Seriously the real issue with a password is that with normal implementations every time you want to use it you have to send your ultra secret password over the internet to the verifying party.
242 notes
·
View notes
Text
Greetings Tumblr!
Quick question.
Just out of curiosity, how would you go about trying to figure out what the fuck this says?

#I already know what it says I just want to know if it's figure-out-able with just this muh#*much#or if i need to write more#im planning on leaving it in the finnish and swedish classroom at my university as a social experiment. if that helps.#uhhhh...#cryptography#writing systems#linguistics#idk
17 notes
·
View notes
Text
So, I am away from computer for four days for a really cool event and I come back and in the mean time they maybe found a polynomial quantum attack against Learning With Errors, a lattice problem? (https://eprint.iacr.org/2024/555) If this paper is correct then this is some serious breaking news shit, because lattices are like the main candidate for quantum-secure public key cryptography. (there are others but they are much less practical and for other types there have also been attacks) I mean, this paper seems to attack just a particular setting, is very impractical and does not work for schemes that are actually proposed, but an existing impractical attack often signals the way for more practical attacks. So, if it is not a false alarm, this is pretty big. It could signal the attackability of lattice schemes and undermine the trust in them. And it takes a long time to move to a new standard. Oh well. I guess we have to wait for experts to check the paper for mistakes before we can say anything.
76 notes
·
View notes
Text
Why Not Write Cryptography
I learned Python in high school in 2003. This was unusual at the time. We were part of a pilot project, testing new teaching materials. The official syllabus still expected us to use PASCAL. In order to satisfy the requirements, we had to learn PASCAL too, after Python. I don't know if PASCAL is still standard.
Some of the early Python programming lessons focused on cryptography. We didn't really learn anything about cryptography itself then, it was all just toy problems to demonstrate basic programming concepts like loops and recursion. Beginners can easily implement some old, outdated ciphers like Caesar, Vigenère, arbitrary 26-letter substitutions, transpositions, and so on.
The Vigenère cipher will be important. It goes like this: First, in order to work with letters, we assign numbers from 0 to 25 to the 26 letters of the alphabet, so A is 0, B is 1, C is 2 and so on. In the programs we wrote, we had to strip out all punctuation and spaces, write everything in uppercase and use the standard transliteration rules for Ä, Ö, Ü, and ß. That's just the encoding part. Now comes the encryption part. For every letter in the plain text, we add the next letter from the key, modulo 26, round robin style. The key is repeated after we get tot he end. Encrypting "HELLOWORLD" with the key "ABC" yields ["H"+"A", "E"+"B", "L"+"C", "L"+"A", "O"+"B", "W"+"C", "O"+"A", "R"+"B", "L"+"C", "D"+"A"], or "HFNLPYOLND". If this short example didn't click for you, you can look it up on Wikipedia and blame me for explaining it badly.
Then our teacher left in the middle of the school year, and a different one took over. He was unfamiliar with encryption algorithms. He took us through some of the exercises about breaking the Caesar cipher with statistics. Then he proclaimed, based on some back-of-the-envelope calculations, that a Vigenère cipher with a long enough key, with the length unknown to the attacker, is "basically uncrackable". You can't brute-force a 20-letter key, and there are no significant statistical patterns.
I told him this wasn't true. If you re-use a Vigenère key, it's like re-using a one time pad key. At the time I just had read the first chapters of Bruce Schneier's "Applied Cryptography", and some pop history books about cold war spy stuff. I knew about the problem with re-using a one-time pad. A one time pad is the same as if your Vigenère key is as long as the message, so there is no way to make any inferences from one letter of the encrypted message to another letter of the plain text. This is mathematically proven to be completely uncrackable, as long as you use the key only one time, hence the name. Re-use of one-time pads actually happened during the cold war. Spy agencies communicated through number stations and one-time pads, but at some point, the Soviets either killed some of their cryptographers in a purge, or they messed up their book-keeping, and they re-used some of their keys. The Americans could decrypt the messages.
Here is how: If you have message $A$ and message $B$, and you re-use the key $K$, then an attacker can take the encrypted messages $A+K$ and $B+K$, and subtract them. That creates $(A+K) - (B+K) = A - B + K - K = A - B$. If you re-use a one-time pad, the attacker can just filter the key out and calculate the difference between two plaintexts.
My teacher didn't know that. He had done a quick back-of-the-envelope calculation about the time it would take to brute-force a 20 letter key, and the likelihood of accidentally arriving at something that would resemble the distribution of letters in the German language. In his mind, a 20 letter key or longer was impossible to crack. At the time, I wouldn't have known how to calculate that probability.
When I challenged his assertion that it would be "uncrackable", he created two messages that were written in German, and pasted them into the program we had been using in class, with a randomly generated key of undisclosed length. He gave me the encrypted output.
Instead of brute-forcing keys, I decided to apply what I knew about re-using one time pads. I wrote a program that takes some of the most common German words, and added them to sections of $(A-B)$. If a word was equal to a section of $B$, then this would generate a section of $A$. Then I used a large spellchecking dictionary to see if the section of $A$ generated by guessing a section of $B$ contained any valid German words. If yes, it would print the guessed word in $B$, the section of $A$, and the corresponding section of the key. There was only a little bit of key material that was common to multiple results, but that was enough to establish how long they key was. From there, I modified my program so that I could interactively try to guess words and it would decrypt the rest of the text based on my guess. The messages were two articles from the local newspaper.
When I showed the decrypted messages to my teacher the next week, got annoyed, and accused me of cheating. Had I installed a keylogger on his machine? Had I rigged his encryption program to leak key material? Had I exploited the old Python random number generator that isn't really random enough for cryptography (but good enough for games and simulations)?
Then I explained my approach. My teacher insisted that this solution didn't count, because it relied on guessing words. It would never have worked on random numeric data. I was just lucky that the messages were written in a language I speak. I could have cheated by using a search engine to find the newspaper articles on the web.
Now the lesson you should take away from this is not that I am smart and teachers are sore losers.
Lesson one: Everybody can build an encryption scheme or security system that he himself can't defeat. That doesn't mean others can't defeat it. You can also create an secret alphabet to protect your teenage diary from your kid sister. It's not practical to use that as an encryption scheme for banking. Something that works for your diary will in all likelihood be inappropriate for online banking, never mind state secrets. You never know if a teenage diary won't be stolen by a determined thief who thinks it holds the secret to a Bitcoin wallet passphrase, or if someone is re-using his banking password in your online game.
Lesson two: When you build a security system, you often accidentally design around an "intended attack". If you build a lock to be especially pick-proof, a burglar can still kick in the door, or break a window. Or maybe a new variation of the old "slide a piece of paper under the door and push the key through" trick works. Non-security experts are especially susceptible to this. Experts in one domain are often blind to attacks/exploits that make use of a different domain. It's like the physicist who saw a magic show and thought it must be powerful magnets at work, when it was actually invisible ropes.
Lesson three: Sometimes a real world problem is a great toy problem, but the easy and didactic toy solution is a really bad real world solution. Encryption was a fun way to teach programming, not a good way to teach encryption. There are many problems like that, like 3D rendering, Chess AI, and neural networks, where the real-world solution is not just more sophisticated than the toy solution, but a completely different architecture with completely different data structures. My own interactive codebreaking program did not work like modern approaches works either.
Lesson four: Don't roll your own cryptography. Don't even implement a known encryption algorithm. Use a cryptography library. Chances are you are not Bruce Schneier or Dan J Bernstein. It's harder than you thought. Unless you are doing a toy programming project to teach programming, it's not a good idea. If you don't take this advice to heart, a teenager with something to prove, somebody much less knowledgeable but with more time on his hands, might cause you trouble.
350 notes
·
View notes
Text
Second-most audacious thing I did in my academic career happened in a cryptography exam. One question gave us a message to encrypt, the method we had to use, and some of the numbers that would be used. We were allowed to choose the remaining values for the encryption algorithm. We had to choose values that would be appropriate and show the process needed to calculate the encryption and decryption keys and show the encryption and decryption process.
The encryption method used exponents and modulo in the encryption and decryption process and instead of actually doing any math on it, I realized I could exploit Fermat's (pronounced fair-ma) little theorem (which the professor had taught earlier that semester) using the numbers the professor gave to make the encryption key equal to 1. As a result, I was able to skip the entire process of showing the encryption process, determining the decryption key, and decrypting the message, because the encryption key I made literally didn't change the message at all.
When I got the exam back, the professor made it very clear how annoyed he was with my answer but gave me full points because I did technically demonstrate how the algorithm works. I'm glad too cause that question was 20% of the exam grade.
He even called me out for my shenanigans when he went over the exam later and modified the question for future semesters to stop others from using my exploit.
183 notes
·
View notes
Text

Section 25. Always Now
#Section 25#Section Twentyfive#bands#musicians#punk#design#designers#Peter Saville#Grafica Industria#Brel Wik#Brett Wickens#typography#cryptography#record covers#album covers#albums
65 notes
·
View notes
Text
Tinkering with a simple shift cipher that outputs emojis since I want to actually make a "cute cipher" (re my primary social username), can you guess what this one says?
#cybersec#cryptography#no id for this one since i dont have a way to do that without giving too many cluea#*clues
34 notes
·
View notes
