#Service Monitoring Software Useful Information
Explore tagged Tumblr posts
Text
Elon Musk’s minions—from trusted sidekicks to random college students and former Musk company interns—have taken over the General Services Administration, a critical government agency that manages federal offices and technology. Already, the team is attempting to use White House security credentials to gain unusual access to GSA tech, deploying a suite of new AI software, and recreating the office in X’s image, according to leaked documents obtained by WIRED.
Some of the same people who helped Musk take over Twitter more than two years ago are now registered as official GSA employees. Nicole Hollander, who slept in Twitter HQ as an unofficial member of Musk’s transition team, has high-level agency access and an official government email address, according to documents viewed by WIRED. Hollander’s husband, Steve Davis, also slept in the office. He has now taken on a leading role in Musk’s Department of Government Efficiency (DOGE). Thomas Shedd, the recently installed director of the Technology Transformation Services within GSA, worked as a software engineer at Tesla for eight years. Edward Coristine, who previously interned at Neuralink, has been onboarded along with Ethan Shaotran, a Harvard senior who is developing his own OpenAI-backed scheduling assistant and participated in an xAI hackathon.
“I believe these people do not want to help the federal government provide services to the American people,” says a current GSA employee who asked not to be named, citing fears of retaliation. “They are acting like this is a takeover of a tech company.”
The team appears to be carrying out Musk’s agenda: slashing the federal government as quickly as possible. They’re currently targeting a 50 percent reduction in spending for every office managed by the GSA, according to documents obtained by WIRED.
There also appears to be an effort to use IT credentials from the Executive Office of the President to access GSA laptops and internal GSA infrastructure. Typically, access to agency systems requires workers to be employed at such agencies, sources say. While Musk's team could be trying to obtain better laptops and equipment from GSA, sources fear that the mandate laid out in the DOGE executive order would grant the body broad access to GSA systems and data. That includes sensitive procurement data, data internal to all the systems and services GSA offers, and internal monitoring software to surveil GSA employees as part of normal auditing and security processes.
The access could give Musk’s proxies the ability to remote into laptops, listen in on meetings, read emails, among many other things, a former Biden official told WIRED on Friday.
“Granting DOGE staff, many of whom aren't government employees, unfettered access to internal government systems and sensitive data poses a huge security risk to the federal government and to the American public,” the Biden official said. “Not only will DOGE be able to review procurement-sensitive information about major government contracts, it'll also be able to actively surveil government employees.”
The new GSA leadership team has prioritized downsizing the GSA’s real estate portfolio, canceling convenience contracts, and rolling out AI tools for use by the federal government, according to internal documents and interviews with sources familiar with the situation. At a GSA office in Washington, DC, earlier this week, there were three items written on a white board sitting in a large, vacant room. “Spending Cuts $585 m, Regulations Removed, 15, Square feet sold/terminated 203,000 sf,” it read, according to a photo viewed by WIRED. There’s no note of who wrote the message, but it appears to be a tracker of cuts made or proposed by the team.
“We notified the commercial real estate market that two GSA properties would soon be listed for sale, and we terminated three leases,” Stephen Ehikian, the newly appointed GSA acting administrator, said in an email to GSA staff on Tuesday, confirming the agency’s focus on lowering real estate costs. “This is our first step in right-sizing the real estate portfolio.”
The proposed changes extend even inside the physical spaces at the GSA offices. Hollander has requested multiple “resting rooms,” for use by the A-suite, a team of employees affiliated with the GSA administrator’s office.
On January 29, a working group of high-ranking GSA employees, including the deputy general counsel and the chief administrative services officer, met to discuss building a resting room prototype. The team mapped out how to get the necessary funding and waivers to build resting rooms in the office, according to an agenda viewed by WIRED.
After Musk bought Twitter, Hollander and Davis moved into the office with their newborn baby. Hollander helped oversee real estate and office design—including the installation of hotel rooms at Twitter HQ, according to a lawsuit later filed by Twitter executives. During the installation process, one of the executives emailed to say that the plans for the rooms were likely not code compliant. Hollander “visited him in person and emphatically instructed him to never put anything about the project in writing again,” the lawsuit alleged. Employees were allegedly instructed to call the hotel rooms “sleeping rooms” and to say they were just for taking naps.
Hollander has also requested access to Public Buildings Service applications; PBS owns and leases office space to government agencies. The timing of the access request lines up with Ehikian’s announcement about shrinking GSA’s real estate cost.
Musk’s lieutenants are also working to authorize the use of AI tools, including Google Gemini and Cursor (an AI coding assistant), for federal workers. On January 30, the group met with Google to discuss Telemetry, a software used to monitor the health and performance of applications, according to a document obtained by WIRED.
A-suite engineers, including Coristine and Shaotran, have requested access to a variety of GSA records, including nearly 10 years of accounting data, as well as detailed records on vendor payments, purchase orders, and revenue.
The GSA takeover mimics Musk’s strategy at other federal agencies like the Office of Personnel Management (OPM). Earlier this month, Amanda Scales, who worked in talent at Musk’s xAI, was appointed as OPM chief of staff. Riccardo Biasini, former Tesla engineer and director of operations at the Boring company, is now a senior adviser to the director. Earlier this week, Musk cohorts at the US Office of Personnel Management emailed more than 2 million federal workers offering “deferred resignations,” allegedly promising employees their regular pay and benefits through September 30.
The email closely mirrored the “extremely hardcore” note Musk sent to Twitter staff in November 2022, shortly after buying the company.
Many federal workers thought the email was fake—as with Twitter, it seemed designed to force people to leave, slashing headcount costs without the headache of an official layoff.
Ehikian followed up with a note to staff stressing that the email was legitimate. “Yes, the OPM email is real and should be taken very seriously,” he said in an email obtained by WIRED. He added that employees should expect a “further consolidation of offices and centralization of functions.”
On Thursday night, GSA workers received a third email related to the resignation request called “Fork in the Road FAQs.” The email explained that employees who resign from their positions would not be required to work and could get a second job. “We encourage you to find a job in the private sector as soon as you would like to do so,” it read. “The way to greater American prosperity is encouraging people to move from lower productivity jobs in the public sector to higher productivity jobs in the private sector.”
The third question posed in the FAQ asked, “Will I really get my full pay and benefits during the entire period through September 30, even if I get a second job?”
“Yes,” the answer read. “You will also accrue further personal leave days, vacation days, etc. and be paid out for unused leave at your final resignation date.”
However, multiple GSA employees have told WIRED that they are refusing to resign, especially after the American Federation of Government Employees (AFGE) told its members on Tuesday that the offer could be void.
“There is not yet any evidence the administration can or will uphold its end of the bargain, that Congress will go along with this unilateral massive restructuring, or that appropriated funds can be used this way, among other issues that have been raised,” the union said in a notice.
There is also concern that, under Musk’s influence, the federal government might not pay for the duration of the deferred resignation period. Thousands of Twitter employees have sued Musk alleging that he failed to pay their agreed upon severance. Last year, one class action suit was dismissed in Musk’s favor.
In an internal video viewed by WIRED, Ehikian reiterated that GSA employees had the “opportunity to participate in a deferred resignation program,” per the email sent by OPM on January 28. Pressing his hands into the namaste gesture, Ehikian added, “If you choose to participate, I offer you my heartfelt gratitude for your service to this nation. If you choose to stay at the GSA, we’ll work together to implement the four pillars from the OPM memo.” He ended the video by saying thank you and pressing his hands into namaste again.
42 notes
·
View notes
Text

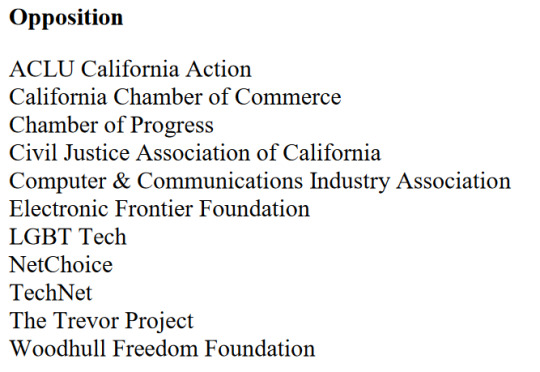
Enhancing Gas Pipeline Management with GIS: Key Benefits and Applications
In the energy and utilities sector, gas pipeline management is complex, requiring precision, safety, and a clear strategy for both existing infrastructure and future expansion. Geographic Information Systems (GIS) have revolutionized pipeline management by providing a spatially accurate, data-rich view of assets. From asset management and leak detection to route planning and demand forecasting, GIS is becoming indispensable for gas companies. This blog delves into the ways GIS transforms gas pipeline management, delivering benefits across safety, efficiency, cost-saving, and planning.
#benefits of using gis for gas pipelines#ensuring gas pipeline safety with gis tools#gas network analysis#gas pipeline asset management#gas pipeline gis mapping services#gas pipeline leak detection using gis#gas pipeline management in gis#gas pipeline mapping software#gas pipeline monitoring tools#gas pipeline risk assessment#gis applications in energy sector#gis for gas pipeline monitoring#gis for infrastructure management#gis in oil and gas industry#gis pipeline maintenance software#gis pipeline monitoring system#gis pipeline route planning#gis software for gas pipeline route optimization#victoryofgoodoverevil#gis solutions for pipeline maintenance and monitoring#gis-based pipeline integrity management#pipeline data management#pipeline geographic information systems#pipeline management solutions#remote sensing for gas pipelines#spatial analysis for gas pipelines#spatial data for gas pipelines
0 notes
Text
When Facebook came for your battery, feudal security failed
When George Hayward was working as a Facebook data-scientist, his bosses ordered him to run a “negative test,” updating Facebook Messenger to deliberately drain users’ batteries, in order to determine how power-hungry various parts of the apps were. Hayward refused, and Facebook fired him, and he sued:
https://nypost.com/2023/01/28/facebook-fires-worker-who-refused-to-do-negative-testing-awsuit/
If you’d like an essay-formatted version of this post to read or share, here’s a link to it on pluralistic.net, my surveillance-free, ad-free, tracker-free blog:
https://pluralistic.net/2023/02/05/battery-vampire/#drained
Hayward balked because he knew that among the 1.3 billion people who use Messenger, some would be placed in harm’s way if Facebook deliberately drained their batteries — physically stranded, unable to communicate with loved ones experiencing emergencies, or locked out of their identification, payment method, and all the other functions filled by mobile phones.
As Hayward told Kathianne Boniello at the New York Post, “Any data scientist worth his or her salt will know, ‘Don’t hurt people…’ I refused to do this test. It turns out if you tell your boss, ‘No, that’s illegal,’ it doesn’t go over very well.”
Negative testing is standard practice at Facebook, and Hayward was given a document called “How to run thoughtful negative tests” regarding which he said, “I have never seen a more horrible document in my career.”
We don’t know much else, because Hayward’s employment contract included a non-negotiable binding arbitration waiver, which means that he surrendered his right to seek legal redress from his former employer. Instead, his claim will be heard by an arbitrator — that is, a fake corporate judge who is paid by Facebook to decide if Facebook was wrong. Even if he finds in Hayward’s favor — something that arbitrators do far less frequently than real judges do — the judgment, and all the information that led up to it, will be confidential, meaning we won’t get to find out more:
https://pluralistic.net/2022/06/12/hot-coffee/#mcgeico
One significant element of this story is that the malicious code was inserted into Facebook’s app. Apps, we’re told, are more secure than real software. Under the “curated computing” model, you forfeit your right to decide what programs run on your devices, and the manufacturer keeps you safe. But in practice, apps are just software, only worse:
https://pluralistic.net/2022/06/23/peek-a-boo/#attack-helicopter-parenting
Apps are part what Bruce Schneier calls “feudal security.” In this model, we defend ourselves against the bandits who roam the internet by moving into a warlord’s fortress. So long as we do what the warlord tells us to do, his hired mercenaries will keep us safe from the bandits:
https://locusmag.com/2021/01/cory-doctorow-neofeudalism-and-the-digital-manor/
But in practice, the mercenaries aren’t all that good at their jobs. They let all kinds of badware into the fortress, like the “pig butchering” apps that snuck into the two major mobile app stores:
https://arstechnica.com/information-technology/2023/02/pig-butchering-scam-apps-sneak-into-apples-app-store-and-google-play/
It’s not merely that the app stores’ masters make mistakes — it’s that when they screw up, we have no recourse. You can’t switch to an app store that pays closer attention, or that lets you install low-level software that monitors and overrides the apps you download.
Indeed, Apple’s Developer Agreement bans apps that violate other services’ terms of service, and they’ve blocked apps like OG App that block Facebook’s surveillance and other enshittification measures, siding with Facebook against Apple device owners who assert the right to control how they interact with the company:
https://pluralistic.net/2022/12/10/e2e/#the-censors-pen
When a company insists that you must be rendered helpless as a condition of protecting you, it sets itself up for ghastly failures. Apple’s decision to prevent every one of its Chinese users from overriding its decisions led inevitably and foreseeably to the Chinese government ordering Apple to spy on those users:
https://pluralistic.net/2022/11/11/foreseeable-consequences/#airdropped
Apple isn’t shy about thwarting Facebook’s business plans, but Apple uses that power selectively — they blocked Facebook from spying on Iphone users (yay!) and Apple covertly spied on its customers in exactly the same way as Facebook, for exactly the same purpose, and lied about it:
https://pluralistic.net/2022/11/14/luxury-surveillance/#liar-liar
The ultimately, irresolvable problem of Feudal Security is that the warlord’s mercenaries will protect you against anyone — except the warlord who pays them. When Apple or Google or Facebook decides to attack its users, the company’s security experts will bend their efforts to preventing those users from defending themselves, turning the fortress into a prison:
https://pluralistic.net/2022/10/20/benevolent-dictators/#felony-contempt-of-business-model
Feudal security leaves us at the mercy of giant corporations — fallible and just as vulnerable to temptation as any of us. Both binding arbitration and feudal security assume that the benevolent dictator will always be benevolent, and never make a mistake. Time and again, these assumptions are proven to be nonsense.
Image: Anthony Quintano (modified) https://commons.wikimedia.org/wiki/File:Mark_Zuckerberg_F8_2018_Keynote_%2841118890174%29.jpg
CC BY 2.0: https://creativecommons.org/licenses/by/2.0/deed.en
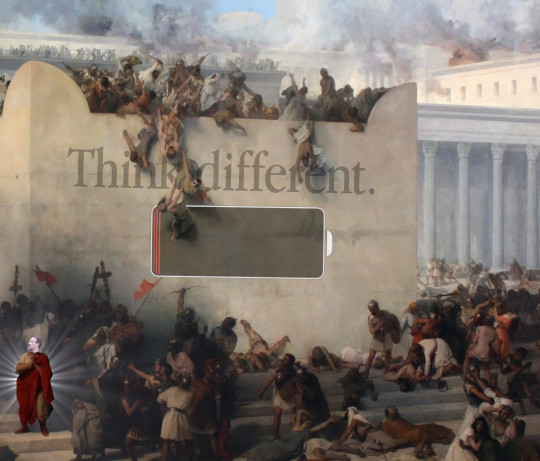
[Image ID: A painting depicting the Roman sacking of Jerusalem. The Roman leader's head has been replaced with Mark Zuckerberg's head. The wall has Apple's 'Think Different' wordmark and an Ios 'low battery' icon.]
Next week (Feb 8-17), I'll be in Australia, touring my book *Chokepoint Capitalism* with my co-author, Rebecca Giblin. We'll be in Brisbane on Feb 8, and then we're doing a remote event for NZ on Feb 9. Next is Melbourne, Sydney and Canberra. I hope to see you!
https://chokepointcapitalism.com/
#pluralistic#manorial security#feudal security#apple#mobile#apps#security through obscurity#binding arbitration#arbitration waivers#transparency#danegeld#surveillance lag
4K notes
·
View notes
Text
So I don't know how people on this app feel about the shit-house that is TikTok but in the US right now the ban they're trying to implement on it is a complete red herring and it needs to be stopped.
They are quite literally trying to implement Patriot Act 2.0 with the RESTRICT Act and using TikTok and China to scare the American public into buying into it wholesale when this shit will change the face of the internet. Here are some excerpts from what the bill would cover on the Infrastructure side:
SEC. 5. Considerations.
(a) Priority information and communications technology areas.—In carrying out sections 3 and 4, the Secretary shall prioritize evaluation of— (1) information and communications technology products or services used by a party to a covered transaction in a sector designated as critical infrastructure in Policy Directive 21 (February 12, 2013; relating to critical infrastructure security and resilience);
(2) software, hardware, or any other product or service integral to telecommunications products and services, including— (A) wireless local area networks;
(B) mobile networks;
(C) satellite payloads;
(D) satellite operations and control;
(E) cable access points;
(F) wireline access points;
(G) core networking systems;
(H) long-, short-, and back-haul networks; or
(I) edge computer platforms;
(3) any software, hardware, or any other product or service integral to data hosting or computing service that uses, processes, or retains, or is expected to use, process, or retain, sensitive personal data with respect to greater than 1,000,000 persons in the United States at any point during the year period preceding the date on which the covered transaction is referred to the Secretary for review or the Secretary initiates review of the covered transaction, including— (A) internet hosting services;
(B) cloud-based or distributed computing and data storage;
(C) machine learning, predictive analytics, and data science products and services, including those involving the provision of services to assist a party utilize, manage, or maintain open-source software;
(D) managed services; and
(E) content delivery services;
(4) internet- or network-enabled sensors, webcams, end-point surveillance or monitoring devices, modems and home networking devices if greater than 1,000,000 units have been sold to persons in the United States at any point during the year period preceding the date on which the covered transaction is referred to the Secretary for review or the Secretary initiates review of the covered transaction;
(5) unmanned vehicles, including drones and other aerials systems, autonomous or semi-autonomous vehicles, or any other product or service integral to the provision, maintenance, or management of such products or services;
(6) software designed or used primarily for connecting with and communicating via the internet that is in use by greater than 1,000,000 persons in the United States at any point during the year period preceding the date on which the covered transaction is referred to the Secretary for review or the Secretary initiates review of the covered transaction, including— (A) desktop applications;
(B) mobile applications;
(C) gaming applications;
(D) payment applications; or
(E) web-based applications; or
(7) information and communications technology products and services integral to— (A) artificial intelligence and machine learning;
(B) quantum key distribution;
(C) quantum communications;
(D) quantum computing;
(E) post-quantum cryptography;
(F) autonomous systems;
(G) advanced robotics;
(H) biotechnology;
(I) synthetic biology;
(J) computational biology; and
(K) e-commerce technology and services, including any electronic techniques for accomplishing business transactions, online retail, internet-enabled logistics, internet-enabled payment technology, and online marketplaces.
(b) Considerations relating to undue and unacceptable risks.—In determining whether a covered transaction poses an undue or unacceptable risk under section 3(a) or 4(a), the Secretary— (1) shall, as the Secretary determines appropriate and in consultation with appropriate agency heads, consider, where available— (A) any removal or exclusion order issued by the Secretary of Homeland Security, the Secretary of Defense, or the Director of National Intelligence pursuant to recommendations of the Federal Acquisition Security Council pursuant to section 1323 of title 41, United States Code;
(B) any order or license revocation issued by the Federal Communications Commission with respect to a transacting party, or any consent decree imposed by the Federal Trade Commission with respect to a transacting party;
(C) any relevant provision of the Defense Federal Acquisition Regulation and the Federal Acquisition Regulation, and the respective supplements to those regulations;
(D) any actual or potential threats to the execution of a national critical function identified by the Director of the Cybersecurity and Infrastructure Security Agency;
(E) the nature, degree, and likelihood of consequence to the public and private sectors of the United States that would occur if vulnerabilities of the information and communications technologies services supply chain were to be exploited; and
(F) any other source of information that the Secretary determines appropriate; and
(2) may consider, where available, any relevant threat assessment or report prepared by the Director of National Intelligence completed or conducted at the request of the Secretary.

Look at that, does that look like it just covers the one app? NO! This would cover EVERYTHING that so much as LOOKS at the internet from the point this bill goes live.
It gets worse though, you wanna see what the penalties are?

(b) Civil penalties.—The Secretary may impose the following civil penalties on a person for each violation by that person of this Act or any regulation, order, direction, mitigation measure, prohibition, or other authorization issued under this Act: (1) A fine of not more than $250,000 or an amount that is twice the value of the transaction that is the basis of the violation with respect to which the penalty is imposed, whichever is greater. (2) Revocation of any mitigation measure or authorization issued under this Act to the person. (c) Criminal penalties.— (1) IN GENERAL.—A person who willfully commits, willfully attempts to commit, or willfully conspires to commit, or aids or abets in the commission of an unlawful act described in subsection (a) shall, upon conviction, be fined not more than $1,000,000, or if a natural person, may be imprisoned for not more than 20 years, or both. (2) CIVIL FORFEITURE.— (A) FORFEITURE.— (i) IN GENERAL.—Any property, real or personal, tangible or intangible, used or intended to be used, in any manner, to commit or facilitate a violation or attempted violation described in paragraph (1) shall be subject to forfeiture to the United States. (ii) PROCEEDS.—Any property, real or personal, tangible or intangible, constituting or traceable to the gross proceeds taken, obtained, or retained, in connection with or as a result of a violation or attempted violation described in paragraph (1) shall be subject to forfeiture to the United States. (B) PROCEDURE.—Seizures and forfeitures under this subsection shall be governed by the provisions of chapter 46 of title 18, United States Code, relating to civil forfeitures, except that such duties as are imposed on the Secretary of Treasury under the customs laws described in section 981(d) of title 18, United States Code, shall be performed by such officers, agents, and other persons as may be designated for that purpose by the Secretary of Homeland Security or the Attorney General. (3) CRIMINAL FORFEITURE.— (A) FORFEITURE.—Any person who is convicted under paragraph (1) shall, in addition to any other penalty, forfeit to the United States— (i) any property, real or personal, tangible or intangible, used or intended to be used, in any manner, to commit or facilitate the violation or attempted violation of paragraph (1); and (ii) any property, real or personal, tangible or intangible, constituting or traceable to the gross proceeds taken, obtained, or retained, in connection with or as a result of the violation. (B) PROCEDURE.—The criminal forfeiture of property under this paragraph, including any seizure and disposition of the property, and any related judicial proceeding, shall be governed by the provisions of section 413 of the Controlled Substances Act (21 U.S.C. 853), except subsections (a) and (d) of that section.
You read that right, you could be fined up to A MILLION FUCKING DOLLARS for knowingly violating the restrict act, so all those people telling you to "just use a VPN" to keep using TikTok? Guess what? That falls under the criminal guidelines of this bill and they're giving you some horrible fucking advice.
Also, VPN's as a whole, if this bill passes, will take a goddamn nose dive in this country because they are another thing that will be covered in this bill.
They chose the perfect name for it, RESTRICT, because that's what it's going to do to our freedoms in this so called "land of the free".
Please, if you are a United States citizen of voting age reach out to your legislature and tell them you do not want this to pass and you will vote against them in the next primary if it does. This is a make or break moment for you if you're younger. Do not allow your generation to suffer a second Patriot Act like those of us that unfortunately allowed for the first one to happen.
And if you support this, I can only assume you're delusional or a paid shill, either way I hope you rot in whatever hell you believe in.
#politics#restrict bill#tiktok#tiktok ban#s.686#us politics#tiktok senate hearing#land of the free i guess#patriot act#patriot act 2.0
898 notes
·
View notes
Text
CA Internet Bills Status as of 7/17/2024
I had wanted to wait to make this post until all of the bills updated texts had been uploaded to the usual sites, but it appears what whoever's supposed to be updating AB 3080 has been lagging, so I'll just go with what I have for now. It'll be long as I'll be looking at their statuses and analyzing their updated texts so I'll put it under a cut for now.
A reminder that California's legislature is currently on recess and will be until August 5th. So no immediately imminent bills at this exact moments. But please read below the cut to get more information on the deadlines coming up.
When I last posted, all three of the bills had gone into review in their respective committees and sadly all of them passed out.
AB 3080: 11 Aye - 0 Nay
AB 1949: 11 Aye - 0 Nay
SB 976: 7 Aye - 4 No Vote
All three bills have been amended during their time in committees.
Ab 3080
AB 3080 was amended and passed from committee as amended, it is now available for a floor vote. This is the only one of the three bills where its amended text hasn't been posted anywhere I can find. However, in the analysis of the July 3rd meeting, there were acknowledgements made that not only is there no effective and safe way to verify age to view online content, but also that the existence of VPNs can circumvent any attempts to region lock sites designated as "adult" (the definition as it stands still appears to be limited to commercial websites where more than 1/3 of their content annually is sexually explicit). And that the methods to implement such a thing on commercial and non-commercial websites alike can be prohibitively expensive. So the author of the bill agreed to amendments in the bill as such according to the analysis:
"In response to the concerns of opposition, the author has agreed to amendments that allow a less restrictive means to suffice in meeting the obligation of the bill, mitigating the impact on protected speech and expression. The amendments provide that “reasonable steps” includes the business implementing a system that includes metadata or response headers identifying the product as sexually explicit to parental control software, embedded hardware applications, and other similar services designed to block, filter, monitor or otherwise prevent a minor’s access to inappropriate online content, or that blocks users designated as minors by the operating system of the device used to access the website. It also limits enforcement of this new cause of action to the Attorney General and requires the Attorney General to promulgate regulations to provide better direction for reasonable steps to verify age in addition to those listed."
So it appears that the bill may allow more websites instead to mark themselves or certain portions of their content as adult in order to be properly vetted by in-device content filters and parental controls that can be set by the device operators (or their parents in the case of minors), rather than a method that would require users to provide identification.
It's eased up quite a bit since its initial incarnation. But it's still better safe than sorry with this kind of bill, so Californians let's still push the state senators to veto this bill completely.
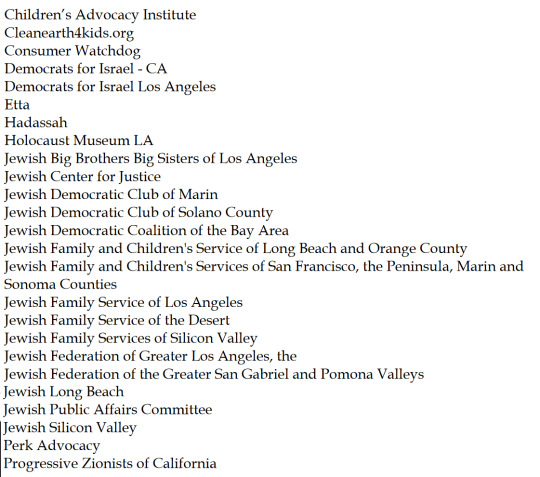
Organizations in support of this bill:
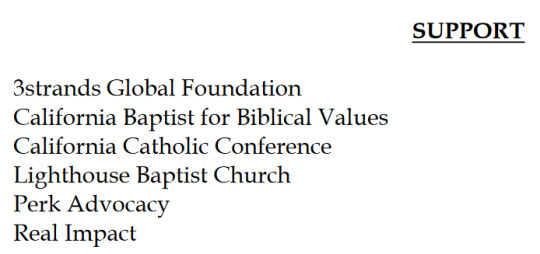
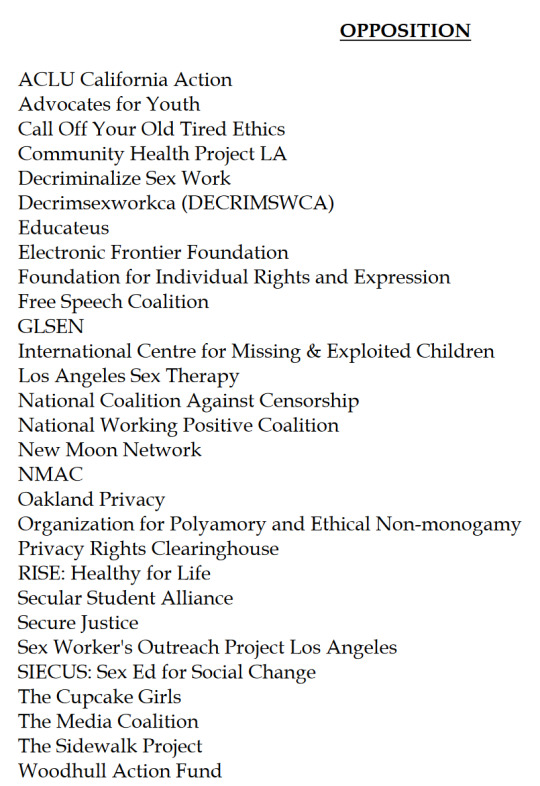
Organizations in opposition to this bill:
AB 1949
AB 1949 was amended and passed from committee as amended, and is currently referred to the Senate Appropriations Committee.
This one has also seen some fairly positive changes during this committee analysis as can be seen in the latest version of the bill. The latest version has removed any indications towards age verification. As well as it having changed several of its details. The bill only comes into effect and prevents the sale of data if the website has actual knowledge of the users' age, and that there shall be an option for the user to transmit a signal that they are under 18 for this purpose. Which again should help the argument against strict age verification barriers due to advertising purposes.
"a business shall not use or disclose the personal information of a consumer if the business has actual knowledge that the consumer is less than 18 years of age, unless the consumer, in the case of a consumer at least 13 years of age and less than 18 years of age, or the consumer’s parent or guardian, in the case of a consumer less than 13 years of age, has affirmatively authorized the use or disclosure of the consumer’s personal information."
"A business shall treat a consumer as under 18 years of age if the consumer, through a platform, technology, or mechanism, transmits a signal indicating that the consumer is less than 18 years of age."
But, once again, it is best to still work against this bill and prevent its passing at all in case it there's push to use it as a stepping stone for any bills which may further push an age verification agenda.
Organizations in support of this bill:
Organizations in opposition of this bill:

SB 976
This bill passed with amendments and is currently referred to the California Assembly Appropriations Committee. Unfortunately no major changes have been made. Only an amendment clarifying that any parental controls are only meant to limit access to "addictive feeds" and limit access to school hours, not any of the content. As this function still requires a "verified adult parent to a minor", this still holds open the door to potential future age verification dangers. As it still states that an application may choose to withhold services to minors altogether, and explicitly leaves open the possibility to allow provisions for age "assurance". So we definitely want to strike this one down if we can.
Organizations in support of this bill:
Organizations in opposition to this bill:
As of this moment, the California Legislature is out on recess until August 5.
The Senate Appropriations Committee (AB 1949) is set to meet on August 5, no word on whether it will be heard that day or on the next set hearing, August 12. So if you wish to send a position letter to the committee it would be best to do so a week before that date, so by July 29. Just to be safe.
No word on when the Assembly Appropriations Committee is set to meet, but the deadline for fiscal committees to pass bills through is August 16, so I expect that SB 976 will be heard before that day at least.
And AB 3080 is set to go to the senate floor rather than be seen by another committee before being read. No word on when the next bill readings will be on the assembly floor after it's reconvened August 5th, but I'll keep an ear to the ground for that.
The last day for each house to pass their bills for the year will be August 31st. So any bills we can stop before then are halted for good for the year.
And for any bills that do slip through, the last day for the governor to sign, let pass without signing, or veto bills is September 30th. So even if the bills pass from the floor to his desk, there's still time to send him messages to urge him to oppose any that slip through.
Thank you for your time, both in reading this and in taking the time to help us fight these bills.
#kosa#california#ab 3080#sb 976#ab 1949#bad internet bills#age verification#internet privacy#internet safety
30 notes
·
View notes
Text
"Just weeks before the implosion of AllHere, an education technology company that had been showered with cash from venture capitalists and featured in glowing profiles by the business press, America’s second-largest school district was warned about problems with AllHere’s product.
As the eight-year-old startup rolled out Los Angeles Unified School District’s flashy new AI-driven chatbot — an animated sun named “Ed” that AllHere was hired to build for $6 million — a former company executive was sending emails to the district and others that Ed’s workings violated bedrock student data privacy principles.
Those emails were sent shortly before The 74 first reported last week that AllHere, with $12 million in investor capital, was in serious straits. A June 14 statement on the company’s website revealed a majority of its employees had been furloughed due to its “current financial position.” Company founder and CEO Joanna Smith-Griffin, a spokesperson for the Los Angeles district said, was no longer on the job.
Smith-Griffin and L.A. Superintendent Alberto Carvalho went on the road together this spring to unveil Ed at a series of high-profile ed tech conferences, with the schools chief dubbing it the nation’s first “personal assistant” for students and leaning hard into LAUSD’s place in the K-12 AI vanguard. He called Ed’s ability to know students “unprecedented in American public education” at the ASU+GSV conference in April.
Through an algorithm that analyzes troves of student information from multiple sources, the chatbot was designed to offer tailored responses to questions like “what grade does my child have in math?” The tool relies on vast amounts of students’ data, including their academic performance and special education accommodations, to function.
Meanwhile, Chris Whiteley, a former senior director of software engineering at AllHere who was laid off in April, had become a whistleblower. He told district officials, its independent inspector general’s office and state education officials that the tool processed student records in ways that likely ran afoul of L.A. Unified’s own data privacy rules and put sensitive information at risk of getting hacked. None of the agencies ever responded, Whiteley told The 74.
...
In order to provide individualized prompts on details like student attendance and demographics, the tool connects to several data sources, according to the contract, including Welligent, an online tool used to track students’ special education services. The document notes that Ed also interfaces with the Whole Child Integrated Data stored on Snowflake, a cloud storage company. Launched in 2019, the Whole Child platform serves as a central repository for LAUSD student data designed to streamline data analysis to help educators monitor students’ progress and personalize instruction.
Whiteley told officials the app included students’ personally identifiable information in all chatbot prompts, even in those where the data weren’t relevant. Prompts containing students’ personal information were also shared with other third-party companies unnecessarily, Whiteley alleges, and were processed on offshore servers. Seven out of eight Ed chatbot requests, he said, are sent to places like Japan, Sweden, the United Kingdom, France, Switzerland, Australia and Canada.
Taken together, he argued the company’s practices ran afoul of data minimization principles, a standard cybersecurity practice that maintains that apps should collect and process the least amount of personal information necessary to accomplish a specific task. Playing fast and loose with the data, he said, unnecessarily exposed students’ information to potential cyberattacks and data breaches and, in cases where the data were processed overseas, could subject it to foreign governments’ data access and surveillance rules.
Chatbot source code that Whiteley shared with The 74 outlines how prompts are processed on foreign servers by a Microsoft AI service that integrates with ChatGPT. The LAUSD chatbot is directed to serve as a “friendly, concise customer support agent” that replies “using simple language a third grader could understand.” When querying the simple prompt “Hello,” the chatbot provided the student’s grades, progress toward graduation and other personal information.
AllHere’s critical flaw, Whiteley said, is that senior executives “didn’t understand how to protect data.”
...
Earlier in the month, a second threat actor known as Satanic Cloud claimed it had access to tens of thousands of L.A. students’ sensitive information and had posted it for sale on Breach Forums for $1,000. In 2022, the district was victim to a massive ransomware attack that exposed reams of sensitive data, including thousands of students’ psychological evaluations, to the dark web.
With AllHere’s fate uncertain, Whiteley blasted the company’s leadership and protocols.
“Personally identifiable information should be considered acid in a company and you should only touch it if you have to because acid is dangerous,” he told The 74. “The errors that were made were so egregious around PII, you should not be in education if you don’t think PII is acid.”
Read the full article here:
https://www.the74million.org/article/whistleblower-l-a-schools-chatbot-misused-student-data-as-tech-co-crumbled/
17 notes
·
View notes
Text
5 Ways to Improve Your Network Security
In today’s digital age, network security is more critical than ever. With cyberattacks becoming more sophisticated and frequent, businesses and individuals alike must take proactive steps to protect their networks. Whether you’re a small business owner or a tech-savvy professional, improving your network security can help safeguard sensitive data, prevent downtime, and maintain trust. Here are five actionable tips to enhance your network’s defenses.
1. Use Strong, Unique Passwords
Weak or reused passwords are among the most common vulnerabilities in network security. To protect your network:
Create strong passwords that include a mix of uppercase and lowercase letters, numbers, and special characters.
Avoid using easily guessed information, such as birthdays or common words like "password123."
Use a password manager to generate and securely store complex passwords for all your accounts.
Implement multi-factor authentication (MFA) for an extra layer of security. MFA requires users to verify their identity through a second method, such as a text message code or biometric scan.
2. Keep Your Software Up-to-Date
Outdated software is a goldmine for hackers who exploit known vulnerabilities. Regular updates ensure you’re protected with the latest security patches.
Update your operating system, applications, and firmware regularly.
Enable automatic updates to ensure critical patches are installed promptly.
Replace unsupported or obsolete hardware and software with newer, more secure alternatives.
3. Secure Your Wi-Fi Network
Your Wi-Fi network is a primary gateway for potential attacks. Securing it is essential:
Change the default administrator username and password for your router.
Use WPA3 encryption (or at least WPA2) to secure your wireless connection.
Hide your network's SSID (Service Set Identifier) so it’s not visible to unauthorized users.
Set up a guest network for visitors, keeping them isolated from your primary network.
4. Install and Update Security Software
Comprehensive security software is your first line of defense against malicious activity.
Use antivirus and anti-malware programs to detect and remove threats.
Install a firewall to monitor and block unauthorized access to your network.
Invest in a Unified Threat Management (UTM) system, which combines multiple security features like intrusion detection, content filtering, and VPN support.
Keep all security software updated to stay protected from the latest threats.
5. Educate and Train Users
Even the most robust security measures can fail if users are unaware of best practices.
Train your team to recognize phishing emails, suspicious links, and social engineering tactics.
Encourage employees to report unusual activity immediately.
Establish a network security policy that outlines acceptable use, password protocols, and steps for reporting incidents.
Conduct regular cybersecurity awareness sessions to keep users informed about emerging threats.
Bonus Tip: Monitor Your Network Activity
Proactively monitoring your network can help you detect potential issues before they become critical. Use tools to track unusual traffic, failed login attempts, and other red flags.
Conclusion
Improving your network security doesn’t have to be overwhelming. By implementing these five steps, you can significantly reduce your risk of cyberattacks and create a safer environment for your business or personal network. Remember, cybersecurity is an ongoing process—stay vigilant, keep learning, and adapt to new threats as they arise.
Have questions or need help securing your network? Contact us today for expert IT solutions tailored to your needs!
4 notes
·
View notes
Note
do you have pokemon sleep?
No, I collected snippets of their privacy policy. I was very uncomfortable with them collecting this data about my sleep habits.
5. WHO WE MIGHT SHARE YOUR INFORMATION WITH
In connection with the purposes and on the lawful grounds described above, we will share your personal information when relevant with third parties such as:
(f) Ad network. Service providers that deliver information to you via ad network system regarding Pokémon's current or future products and services (Adjust KK, based in Japan, and its subcontractors, such as Adjust GmbH, Lease web Germany GmbH, Lease web Netherlands B.V., and Leaseweb USA, Inc., based in Germany, Netherlands, and USA).
(g) Other third parties (including professional advisers). Any other third parties (including legal or other advisors, regulatory authorities, courts, law enforcement agencies and government agencies) based in the UK, USA, Japan, and other countries/regions to enable us to enforce our legal rights, or to protect the rights, property, or safety of our employees, or where such disclosure may be permitted or required by law.
We, and others, use cookies, web beacons, device IDs, and other tracking mechanisms to ensure that you get the most out of our App. Cookies are small amounts of information in the form of text files which we store on the device you use to access our App. Cookies and other tracking mechanisms, such as device IDs, allow us and others, to monitor your use of the software, simplify your use of our App, and to help us and others associate the mobile devices you use, your activities across websites, and your browsers for advertising purposes.
7.2 Our website may contain content and links to other sites that are operated by third parties that may also operate cookies and other tracking mechanisms. We do not control these third-party sites or their tracking activities, and this Privacy Notice does not apply to them. Please consult the terms, conditions, and Privacy Notice of the relevant third-party site to find out how that site collects and uses vour information and to establish whether and for what purpose it uses cookies.
8. HOW WE LOOK AFTER YOUR INFORMATION AND HOW LONG WE KEEP IT FOR
8.1 We use appropriate technological and operational security measures to protect your information against unauthorized access or unlawful use.
8.2 We will retain your information for as long as is appropriate to provide you with the services that you have requested from us or for as long as we reasonably require to retain the information for our lawful business purposes.
32 notes
·
View notes
Text

Cisco ThousandEyes Endpoint Agent for MacOS and RoomOS Certificate Validation Vulnerability (CVE-2025-20126)CVE number – CVE-2025-20126 A vulnerability in certification validation routines of Cisco ThousandEyes Endpoint Agent for macOS and RoomOS could allow an unauthenticated, remote attacker to intercept or manipulate metrics information. This vulnerability exists because the affected software does not properly validate certificates for hosted metrics services. An on-path attacker could exploit this vulnerability by intercepting network traffic using a crafted certificate. A successful exploit could allow the attacker to masquerade as a trusted host and monitor or change communications between the remote metrics service and the vulnerable client. Cisco has released software updates that address this vulnerability. There are Read the full article
2 notes
·
View notes
Text
Cell-site simulators mimic cell towers to intercept communications, indiscriminately collecting sensitive data such as call metadata, location information, and app traffic from all phones within their range. Their use has drawn widespread criticism from privacy advocates and activists, who argue that such technology can be exploited to covertly monitor protestors and suppress dissent.
The DNC convened amid widespread protests over Israel’s assault on Gaza. While credentialed influencers attended exclusive yacht parties and VIP events, thousands of demonstrators faced a heavy law enforcement presence, including officers from the US Capitol Police, Secret Service, Homeland Security Investigations, local sheriff’s offices, and Chicago police.
Concerns over potential surveillance prompted WIRED to conduct a first-of-its-kind wireless survey to investigate whether cell-site simulators were being deployed. Reporters, equipped with two rooted Android phones and Wi-Fi hotspots running detection software, used Rayhunter—a tool developed by the EFF [Electronic Frontier Foundation] to detect data anomalies associated with these devices. WIRED’s reporters monitored signals at protests and event locations across Chicago, collecting extensive data during the political convention.
...According to the EFF’s analysis, on August 18—the day before the convention officially began—a device carried by WIRED reporters en route a hotel housing Democratic delegates from states in the US Midwest abruptly switched to a new tower. That tower asked for the device’s IMSI and then immediately disconnected—a sequence consistent with the operation of a cell-site simulator.
“This is extremely suspicious behavior that normal towers do not exhibit,” Quintin [a senior technologist at the EFF] says. He notes that the EFF typically observed similar patterns only during simulated and controlled attacks. “This is not 100 percent incontrovertible truth, but it’s strong evidence suggesting a cell-site simulator was deployed. We don’t know who was responsible—it could have been the US government, foreign actors, or another entity.”
3 notes
·
View notes
Text
Why Websites Fail After Launch and How to Prevent It

Common Reasons Websites Fail After Launch
1. Poor User Experience (UX)
Websites that are difficult to navigate, slow to load, or visually cluttered often drive users away. A seamless and intuitive user experience is essential to retain visitors and reduce bounce rates.
2. Lack of Mobile Optimization
With mobile devices dominating web traffic, failing to create a responsive design can result in missed opportunities. A mobile-friendly website is crucial for reaching and engaging with a wider audience.
3. Weak SEO Strategies
Without proper search engine optimization, even the most visually appealing website will struggle to attract organic traffic. SEO plays a vital role in improving your website’s visibility and ranking on search engines.
4. Inconsistent Content Updates
Static or outdated content can hurt your credibility and discourage repeat visits. Engaging and regularly updated content is key to building trust and maintaining relevance.
5. Ineffective Marketing
Launching a website without a solid digital marketing plan often results in low traffic and poor visibility. Without strategic efforts like social media promotion, PPC campaigns, and email marketing, your site might go unnoticed.
6. Security Flaws
Websites that aren’t secure are vulnerable to cyberattacks, which can lead to data breaches and loss of trust. Security issues can damage your reputation and affect customer loyalty.
How to Prevent Website Failures
1. Deliver Exceptional User Experience
Focus on intuitive navigation, fast load times, and appealing visuals.
Regularly test and improve usability to meet user expectations.
Implement features like live chat and easy search options for better engagement.
2. Ensure Mobile Optimization
Develop responsive websites that adapt to all devices, ensuring consistent performance.
Use tools to test mobile usability and identify any potential issues.
3. Implement Comprehensive SEO
Conduct keyword research and integrate terms like “best website development company in Jaipur” to boost visibility.
Optimize meta tags, headers, and content for search engines.
Focus on link-building and technical SEO for better rankings.
4. Keep Content Fresh and Relevant
Regularly update blogs, news sections, or product pages with new information.
Use analytics to understand what content resonates with your audience.
5. Plan and Execute Digital Marketing
Promote your website through strategic social media campaigns.
Use email marketing to nurture leads and retain existing customers.
Leverage PPC ads to drive immediate traffic and conversions.
6. Prioritize Website Security
Use SSL certificates and HTTPS protocols for secure connections.
Regularly update software, plugins, and themes to prevent vulnerabilities.
Employ firewalls and advanced malware protection.
Why Choose Webpino Software?
At Webpino Software, we take pride in being the best website development company in Jaipur, offering solutions that ensure your website remains a powerful tool for your business even after its launch. Here’s why businesses trust us:
Custom Web Solutions: We tailor our services to meet your unique business needs.
Mobile-Friendly Designs: We prioritize responsive websites that perform seamlessly across all devices.
SEO Expertise: Our team implements robust SEO strategies to help your website rank higher and attract more traffic.
Proactive Maintenance: We monitor and maintain your website to keep it updated, secure, and performing at its best.
Comprehensive Services: From design to marketing, we provide end-to-end support to help your business succeed.
Partner with the Best Website Development Company in Jaipur
Webpino Software is dedicated to ensuring your website not only launches successfully but also achieves long-term growth. As the best website development company in Jaipur, we offer cutting-edge solutions that address all post-launch challenges, from optimizing user experience to ensuring top-notch security.
Whether you’re launching a new website or struggling with post-launch issues, Webpino Software is here to help. Our team of experts is committed to your success, offering tailored strategies to elevate your online presence.
Contact us today to ensure your website thrives in the competitive digital landscape!
#website development#web design#wordpress development#website design#web developers#digital marketing#seo#website#seo friendlly website#business website solutions#custom website design#website optimization#web hosting#wordpress#website design in jaipur#best website development company in jaipur
2 notes
·
View notes
Text
Generative AI tools such as OpenAI’s ChatGPT and Microsoft’s Copilot are rapidly evolving, fueling concerns that the technology could open the door to multiple privacy and security issues, particularly in the workplace.
In May, privacy campaigners dubbed Microsoft’s new Recall tool a potential “privacy nightmare” due to its ability to take screenshots of your laptop every few seconds. The feature has caught the attention of UK regulator the Information Commissioner’s Office, which is asking Microsoft to reveal more about the safety of the product launching soon in its Copilot+ PCs.
Concerns are also mounting over OpenAI’s ChatGPT, which has demonstrated screenshotting abilities in its soon-to-launch macOS app that privacy experts say could result in the capture of sensitive data.
The US House of Representatives has banned the use of Microsoft’s Copilot among staff members after it was deemed by the Office of Cybersecurity to be a risk to users due to “the threat of leaking House data to non-House approved cloud services.”
Meanwhile, market analyst Gartner has cautioned that “using Copilot for Microsoft 365 exposes the risks of sensitive data and content exposure internally and externally.” And last month, Google was forced to make adjustments to its new search feature, AI Overviews, after screenshots of bizarre and misleading answers to queries went viral.
Overexposed
For those using generative AI at work, one of the biggest challenges is the risk of inadvertently exposing sensitive data. Most generative AI systems are “essentially big sponges,” says Camden Woollven, group head of AI at risk management firm GRC International Group. “They soak up huge amounts of information from the internet to train their language models.”
AI companies are “hungry for data to train their models,” and are “seemingly making it behaviorally attractive” to do so, says Steve Elcock, CEO and founder at software firm Elementsuite. This vast amount of data collection means there’s the potential for sensitive information to be put “into somebody else’s ecosystem,” says Jeff Watkins, chief product and technology officer at digital consultancy xDesign. “It could also later be extracted through clever prompting.”
At the same time, there’s the threat of AI systems themselves being targeted by hackers. “Theoretically, if an attacker managed to gain access to the large language model (LLM) that powers a company's AI tools, they could siphon off sensitive data, plant false or misleading outputs, or use the AI to spread malware,” says Woollven.
Consumer-grade AI tools can create obvious risks. However, an increasing number of potential issues are arising with “proprietary” AI offerings broadly deemed safe for work such as Microsoft Copilot, says Phil Robinson, principal consultant at security consultancy Prism Infosec.
“This could theoretically be used to look at sensitive data if access privileges have not been locked down. We could see employees asking to see pay scales, M&A activity, or documents containing credentials, which could then be leaked or sold.”
Another concern centers around AI tools that could be used to monitor staff, potentially infringing their privacy. Microsoft’s Recall feature states that “your snapshots are yours; they stay locally on your PC” and “you are always in control with privacy you can trust.”
Yet “it doesn’t seem very long before this technology could be used for monitoring employees,” says Elcock.
Self-Censorship
Generative AI does pose several potential risks, but there are steps businesses and individual employees can take to improve privacy and security. First, do not put confidential information into a prompt for a publicly available tool such as ChatGPT or Google’s Gemini, says Lisa Avvocato, vice president of marketing and community at data firm Sama.
When crafting a prompt, be generic to avoid sharing too much. “Ask, ‘Write a proposal template for budget expenditure,’ not ‘Here is my budget, write a proposal for expenditure on a sensitive project,’” she says. “Use AI as your first draft, then layer in the sensitive information you need to include.”
If you use it for research, avoid issues such as those seen with Google’s AI Overviews by validating what it provides, says Avvocato. “Ask it to provide references and links to its sources. If you ask AI to write code, you still need to review it, rather than assuming it’s good to go.”
Microsoft has itself stated that Copilot needs to be configured correctly and the “least privilege”—the concept that users should only have access to the information they need—should be applied. This is “a crucial point,” says Prism Infosec’s Robinson. “Organizations must lay the groundwork for these systems and not just trust the technology and assume everything will be OK.”
It’s also worth noting that ChatGPT uses the data you share to train its models, unless you turn it off in the settings or use the enterprise version.
List of Assurances
The firms integrating generative AI into their products say they’re doing everything they can to protect security and privacy. Microsoft is keen to outline security and privacy considerations in its Recall product and the ability to control the feature in Settings > Privacy & security > Recall & snapshots.
Google says generative AI in Workspace “does not change our foundational privacy protections for giving users choice and control over their data,” and stipulates that information is not used for advertising.
OpenAI reiterates how it maintains security and privacy in its products, while enterprise versions are available with extra controls. “We want our AI models to learn about the world, not private individuals—and we take steps to protect people’s data and privacy,” an OpenAI spokesperson tells WIRED.
OpenAI says it offers ways to control how data is used, including self-service tools to access, export, and delete personal information, as well as the ability to opt out of use of content to improve its models. ChatGPT Team, ChatGPT Enterprise, and its API are not trained on data or conversations, and its models don’t learn from usage by default, according to the company.
Either way, it looks like your AI coworker is here to stay. As these systems become more sophisticated and omnipresent in the workplace, the risks are only going to intensify, says Woollven. “We're already seeing the emergence of multimodal AI such as GPT-4o that can analyze and generate images, audio, and video. So now it's not just text-based data that companies need to worry about safeguarding.”
With this in mind, people—and businesses—need to get in the mindset of treating AI like any other third-party service, says Woollven. “Don't share anything you wouldn't want publicly broadcasted.”
10 notes
·
View notes
Text
How-To IT
Topic: Core areas of IT
1. Hardware
• Computers (Desktops, Laptops, Workstations)
• Servers and Data Centers
• Networking Devices (Routers, Switches, Modems)
• Storage Devices (HDDs, SSDs, NAS)
• Peripheral Devices (Printers, Scanners, Monitors)
2. Software
• Operating Systems (Windows, Linux, macOS)
• Application Software (Office Suites, ERP, CRM)
• Development Software (IDEs, Code Libraries, APIs)
• Middleware (Integration Tools)
• Security Software (Antivirus, Firewalls, SIEM)
3. Networking and Telecommunications
• LAN/WAN Infrastructure
• Wireless Networking (Wi-Fi, 5G)
• VPNs (Virtual Private Networks)
• Communication Systems (VoIP, Email Servers)
• Internet Services
4. Data Management
• Databases (SQL, NoSQL)
• Data Warehousing
• Big Data Technologies (Hadoop, Spark)
• Backup and Recovery Systems
• Data Integration Tools
5. Cybersecurity
• Network Security
• Endpoint Protection
• Identity and Access Management (IAM)
• Threat Detection and Incident Response
• Encryption and Data Privacy
6. Software Development
• Front-End Development (UI/UX Design)
• Back-End Development
• DevOps and CI/CD Pipelines
• Mobile App Development
• Cloud-Native Development
7. Cloud Computing
• Infrastructure as a Service (IaaS)
• Platform as a Service (PaaS)
• Software as a Service (SaaS)
• Serverless Computing
• Cloud Storage and Management
8. IT Support and Services
• Help Desk Support
• IT Service Management (ITSM)
• System Administration
• Hardware and Software Troubleshooting
• End-User Training
9. Artificial Intelligence and Machine Learning
• AI Algorithms and Frameworks
• Natural Language Processing (NLP)
• Computer Vision
• Robotics
• Predictive Analytics
10. Business Intelligence and Analytics
• Reporting Tools (Tableau, Power BI)
• Data Visualization
• Business Analytics Platforms
• Predictive Modeling
11. Internet of Things (IoT)
• IoT Devices and Sensors
• IoT Platforms
• Edge Computing
• Smart Systems (Homes, Cities, Vehicles)
12. Enterprise Systems
• Enterprise Resource Planning (ERP)
• Customer Relationship Management (CRM)
• Human Resource Management Systems (HRMS)
• Supply Chain Management Systems
13. IT Governance and Compliance
• ITIL (Information Technology Infrastructure Library)
• COBIT (Control Objectives for Information Technologies)
• ISO/IEC Standards
• Regulatory Compliance (GDPR, HIPAA, SOX)
14. Emerging Technologies
• Blockchain
• Quantum Computing
• Augmented Reality (AR) and Virtual Reality (VR)
• 3D Printing
• Digital Twins
15. IT Project Management
• Agile, Scrum, and Kanban
• Waterfall Methodology
• Resource Allocation
• Risk Management
16. IT Infrastructure
• Data Centers
• Virtualization (VMware, Hyper-V)
• Disaster Recovery Planning
• Load Balancing
17. IT Education and Certifications
• Vendor Certifications (Microsoft, Cisco, AWS)
• Training and Development Programs
• Online Learning Platforms
18. IT Operations and Monitoring
• Performance Monitoring (APM, Network Monitoring)
• IT Asset Management
• Event and Incident Management
19. Software Testing
• Manual Testing: Human testers evaluate software by executing test cases without using automation tools.
• Automated Testing: Use of testing tools (e.g., Selenium, JUnit) to run automated scripts and check software behavior.
• Functional Testing: Validating that the software performs its intended functions.
• Non-Functional Testing: Assessing non-functional aspects such as performance, usability, and security.
• Unit Testing: Testing individual components or units of code for correctness.
• Integration Testing: Ensuring that different modules or systems work together as expected.
• System Testing: Verifying the complete software system’s behavior against requirements.
• Acceptance Testing: Conducting tests to confirm that the software meets business requirements (including UAT - User Acceptance Testing).
• Regression Testing: Ensuring that new changes or features do not negatively affect existing functionalities.
• Performance Testing: Testing software performance under various conditions (load, stress, scalability).
• Security Testing: Identifying vulnerabilities and assessing the software’s ability to protect data.
• Compatibility Testing: Ensuring the software works on different operating systems, browsers, or devices.
• Continuous Testing: Integrating testing into the development lifecycle to provide quick feedback and minimize bugs.
• Test Automation Frameworks: Tools and structures used to automate testing processes (e.g., TestNG, Appium).
19. VoIP (Voice over IP)
VoIP Protocols & Standards
• SIP (Session Initiation Protocol)
• H.323
• RTP (Real-Time Transport Protocol)
• MGCP (Media Gateway Control Protocol)
VoIP Hardware
• IP Phones (Desk Phones, Mobile Clients)
• VoIP Gateways
• Analog Telephone Adapters (ATAs)
• VoIP Servers
• Network Switches/ Routers for VoIP
VoIP Software
• Softphones (e.g., Zoiper, X-Lite)
• PBX (Private Branch Exchange) Systems
• VoIP Management Software
• Call Center Solutions (e.g., Asterisk, 3CX)
VoIP Network Infrastructure
• Quality of Service (QoS) Configuration
• VPNs (Virtual Private Networks) for VoIP
• VoIP Traffic Shaping & Bandwidth Management
• Firewall and Security Configurations for VoIP
• Network Monitoring & Optimization Tools
VoIP Security
• Encryption (SRTP, TLS)
• Authentication and Authorization
• Firewall & Intrusion Detection Systems
• VoIP Fraud DetectionVoIP Providers
• Hosted VoIP Services (e.g., RingCentral, Vonage)
• SIP Trunking Providers
• PBX Hosting & Managed Services
VoIP Quality and Testing
• Call Quality Monitoring
• Latency, Jitter, and Packet Loss Testing
• VoIP Performance Metrics and Reporting Tools
• User Acceptance Testing (UAT) for VoIP Systems
Integration with Other Systems
• CRM Integration (e.g., Salesforce with VoIP)
• Unified Communications (UC) Solutions
• Contact Center Integration
• Email, Chat, and Video Communication Integration
2 notes
·
View notes
Text
Subprime gadgets

I'm on tour with my new, nationally bestselling novel The Bezzle! Catch me THIS SUNDAY in ANAHEIM at WONDERCON: YA Fantasy, Room 207, 10 a.m.; Signing, 11 a.m.; Teaching Writing, 2 p.m., Room 213CD.

The promise of feudal security: "Surrender control over your digital life so that we, the wise, giant corporation, can ensure that you aren't tricked into catastrophic blunders that expose you to harm":
https://locusmag.com/2021/01/cory-doctorow-neofeudalism-and-the-digital-manor/
The tech giant is a feudal warlord whose platform is a fortress; move into the fortress and the warlord will defend you against the bandits roaming the lawless land beyond its walls.
That's the promise, here's the failure: What happens when the warlord decides to attack you? If a tech giant decides to do something that harms you, the fortress becomes a prison and the thick walls keep you in.
Apple does this all the time: "click this box and we will use our control over our platform to stop Facebook from spying on you" (Ios as fortress). "No matter what box you click, we will spy on you and because we control which apps you can install, we can stop you from blocking our spying" (Ios as prison):
https://pluralistic.net/2022/11/14/luxury-surveillance/#liar-liar
But it's not just Apple – any corporation that arrogates to itself the right to override your own choices about your technology will eventually yield to temptation, using that veto to help itself at your expense:
https://pluralistic.net/2023/07/28/microincentives-and-enshittification/
Once the corporation puts the gun on the mantelpiece in Act One, they're begging their KPI-obsessed managers to take it down and shoot you in the head with it in anticipation of of their annual Act Three performance review:
https://pluralistic.net/2023/12/08/playstationed/#tyler-james-hill
One particularly pernicious form of control is "trusted computing" and its handmaiden, "remote attestation." Broadly, this is when a device is designed to gather information about how it is configured and to send verifiable testaments about that configuration to third parties, even if you want to lie to those people:
https://www.eff.org/deeplinks/2023/08/your-computer-should-say-what-you-tell-it-say-1
New HP printers are designed to continuously monitor how you use them – and data-mine the documents you print for marketing data. You have to hand over a credit-card in order to use them, and HP reserves the right to fine you if your printer is unreachable, which would frustrate their ability to spy on you and charge you rent:
https://arstechnica.com/gadgets/2024/02/hp-wants-you-to-pay-up-to-36-month-to-rent-a-printer-that-it-monitors/
Under normal circumstances, this technological attack would prompt a defense, like an aftermarket mod that prevents your printer's computer from monitoring you. This is "adversarial interoperability," a once-common technological move:
https://www.eff.org/deeplinks/2019/10/adversarial-interoperability
An adversarial interoperator seeking to protect HP printer users from HP could gin up fake telemetry to send to HP, so they wouldn't be able to tell that you'd seized the means of computation, triggering fines charged to your credit card.
Enter remote attestation: if HP can create a sealed "trusted platform module" or a (less reliable) "secure enclave" that gathers and cryptographically signs information about which software your printer is running, HP can detect when you have modified it. They can force your printer to rat you out – to spill your secrets to your enemy.
Remote attestation is already a reliable feature of mobile platforms, allowing agencies and corporations whose services you use to make sure that you're perfectly defenseless – not blocking ads or tracking, or doing anything else that shifts power from them to you – before they agree to communicate with your device.
What's more, these "trusted computing" systems aren't just technological impediments to your digital wellbeing – they also carry the force of law. Under Section 1201 of the Digital Millennium Copyright Act, these snitch-chips are "an effective means of access control" which means that anyone who helps you bypass them faces a $500,000 fine and a five-year prison sentence for a first offense.
Feudal security builds fortresses out of trusted computing and remote attestation and promises to use them to defend you from marauders. Remote attestation lets them determine whether your device has been compromised by someone seeking to harm you – it gives them a reliable testament about your device's configuration even if your device has been poisoned by bandits:
https://pluralistic.net/2020/12/05/trusting-trust/#thompsons-devil
The fact that you can't override your computer's remote attestations means that you can't be tricked into doing so. That's a part of your computer that belongs to the manufacturer, not you, and it only takes orders from its owner. So long as the benevolent dictator remains benevolent, this is a protective against your own lapses, follies and missteps. But if the corporate warlord turns bandit, this makes you powerless to stop them from devouring you whole.
With that out of the way, let's talk about debt.
Debt is a normal feature of any economy, but today's debt plays a different role from the normal debt that characterized life before wages stagnated and inequality skyrocketed. 40 years ago, neoliberalism – with its assaults on unions and regulations – kicked off a multigenerational process of taking wealth away from working people to make the rich richer.
Have you ever watched a genius pickpocket like Apollo Robbins work? When Robins lifts your wristwatch, he curls his fingers around your wrist, expertly adding pressure to simulate the effect of a watchband, even as he takes away your watch. Then, he gradually releases his grip, so slowly that you don't even notice:
https://www.reddit.com/r/nextfuckinglevel/comments/ppqjya/apollo_robbins_a_master_pickpocket_effortlessly/
For the wealthy to successfully impoverish the rest of us, they had to provide something that made us feel like we were still doing OK, even as they stole our wages, our savings, and our futures. So, even as they shipped our jobs overseas in search of weak environmental laws and weaker labor protection, they shared some of the savings with us, letting us buy more with less. But if your wages keep stagnating, it doesn't matter how cheap a big-screen TV gets, because you're tapped out.
So in tandem with cheap goods from overseas sweatshops, we got easy credit: access to debt. As wages fell, debt rose up to fill the gap. For a while, it's felt OK. Your wages might be falling off, the cost of health care and university might be skyrocketing, but everything was getting cheaper, it was so easy to borrow, and your principal asset – your family home – was going up in value, too.
This period was a "bezzle," John Kenneth Galbraith's name for "The magic interval when a confidence trickster knows he has the money he has appropriated but the victim does not yet understand that he has lost it." It's the moment after Apollo Robbins has your watch but before you notice it's gone. In that moment, both you and Robbins feel like you have a watch – the world's supply of watch-derived happiness actually goes up for a moment.
There's a natural limit to debt-fueled consumption: as Michael Hudson says, "debts that can't be paid, won't be paid." Once the debtor owes more than they can pay back – or even service – creditors become less willing to advance credit to them. Worse, they start to demand the right to liquidate the debtor's assets. That can trigger some pretty intense political instability, especially when the only substantial asset most debtors own is the roof over their heads:
https://pluralistic.net/2022/11/06/the-end-of-the-road-to-serfdom/
"Debts that can't be paid, won't be paid," but that doesn't stop creditors from trying to get blood from our stones. As more of us became bankrupt, the bankruptcy system was gutted, turned into a punitive measure designed to terrorize people into continuing to pay down their debts long past the point where they can reasonably do so:
https://pluralistic.net/2022/10/09/bankruptcy-protects-fake-people-brutalizes-real-ones/
Enter "subprime" – loans advanced to people who stand no meaningful chance of every paying them back. We all remember the subprime housing bubble, in which complex and deceptive mortgages were extended to borrowers on the promise that they could either flip or remortgage their house before the subprime mortgages detonated when their "teaser rates" expired and the price of staying in your home doubled or tripled.
Subprime housing loans were extended on the belief that people would meekly render themselves homeless once the music stopped, forfeiting all the money they'd plowed into their homes because the contract said they had to. For a brief minute there, it looked like there would be a rebellion against mass foreclosure, but then Obama and Timothy Geithner decreed that millions of Americans would have to lose their homes to "foam the runways" for the banks:
https://wallstreetonparade.com/2012/08/how-treasury-secretary-geithner-foamed-the-runways-with-childrens-shattered-lives/
That's one way to run a subprime shop: offer predatory loans to people who can't afford them and then confiscate their assets when they – inevitably – fail to pay their debts off.
But there's another form of subprime, familiar to loan sharks through the ages: lend money at punitive interest rates, such that the borrower can never repay the debt, and then terrorize the borrower into making payments for as long as possible. Do this right and the borrower will pay you several times the value of the loan, and still owe you a bundle. If the borrower ever earns anything, you'll have a claim on it. Think of Americans who borrowed $79,000 to go to university, paid back $190,000 and still owe $236,000:
https://pluralistic.net/2020/12/04/kawaski-trawick/#strike-debt
This kind of loan-sharking is profitable, but labor-intensive. It requires that the debtor make payments they fundamentally can't afford. The usurer needs to get their straw right down into the very bottom of the borrower's milkshake and suck up every drop. You need to convince the debtor to sell their wedding ring, then dip into their kid's college fund, then steal their father's coin collection, and, then break into cars to steal the stereos. It takes a lot of person-to-person work to keep your sucker sufficiently motivated to do all that.
This is where digital meets subprime. There's $1T worth of subprime car-loans in America. These are pure predation: the lender sells a beater to a mark, offering a low down-payment loan with a low initial interest rate. The borrower makes payments at that rate for a couple of months, but then the rate blows up to more than they can afford.
Trusted computing makes this marginal racket into a serious industry. First, there's the ability of the car to narc you out to the repo man by reporting on its location. Tesla does one better: if you get behind in your payments, your Tesla immobilizes itself and phones home, waits for the repo man to come to the parking lot, then it backs itself out of the spot while honking its horn and flashing its lights:
https://tiremeetsroad.com/2021/03/18/tesla-allegedly-remotely-unlocks-model-3-owners-car-uses-smart-summon-to-help-repo-agent/
That immobilization trick shows how a canny subprime car-lender can combine the two kinds of subprime: they can secure the loan against an asset (the car), but also coerce borrowers into prioritizing repayment over other necessities of life. After your car immobilizes itself, you just might decide to call the dealership and put down your credit card, even if that means not being able to afford groceries or child support or rent.
One thing we can say about digital tools: they're flexible. Any sadistic motivational technique a lender can dream up, a computerized device can execute. The subprime car market relies on a spectrum of coercive tactics: cars that immobilize themselves, sure, but how about cars that turn on their speakers to max and blare a continuous recording telling you that you're a deadbeat and demanding payment?
https://archive.nytimes.com/dealbook.nytimes.com/2014/09/24/miss-a-payment-good-luck-moving-that-car/
The more a subprime lender can rely on a gadget to torment you on their behalf, the more loans they can issue. Here, at last, is a form of automation-driven mass unemployment: normally, an economy that has been fully captured by wealthy oligarchs needs squadrons of cruel arm-breakers to convince the plebs to prioritize debt service over survival. The infinitely flexible, tireless digital arm-breakers enabled by trusted computing have deprived all of those skilled torturers of their rightful employment:
https://pluralistic.net/2021/04/02/innovation-unlocks-markets/#digital-arm-breakers
The world leader in trusted computing isn't cars, though – it's phones. Long before anyone figured out how to make a car take orders from its manufacturer over the objections of its driver, Apple and Google were inventing "curating computing" whose app stores determined which software you could run and how you could run it.
Back in 2021, Indian subprime lenders hit on the strategy of securing their loans by loading borrowers' phones up with digital arm-breaking software:
https://restofworld.org/2021/loans-that-hijack-your-phone-are-coming-to-india/
The software would gather statistics on your app usage. When you missed a payment, the phone would block you from accessing your most frequently used app. If that didn't motivate you to pay, you'd lose your second-most favorite app, then your third, fourth, etc.
This kind of digital arm-breaking is only possible if your phone is designed to prioritize remote instructions – from the manufacturer and its app makers – over your own. It also only works if the digital arm-breaking company can confirm that you haven't jailbroken your phone, which might allow you to send fake data back saying that your apps have been disabled, while you continue to use those apps. In other words, this kind of digital sadism only works if you've got trusted computing and remote attestation.
Enter "Device Lock Controller," an app that comes pre-installed on some Google Pixel phones. To quote from the app's description: "Device Lock Controller enables device management for credit providers. Your provider can remotely restrict access to your device if you don't make payments":
https://lemmy.world/post/13359866
Google's pitch to Android users is that their "walled garden" is a fortress that keeps people who want to do bad things to you from reaching you. But they're pre-installing software that turns the fortress into a prison that you can't escape if they decide to let someone come after you.
There's a certain kind of economist who looks at these forms of automated, fine-grained punishments and sees nothing but a tool for producing an "efficient market" in debt. For them, the ability to automate arm-breaking results in loans being offered to good, hardworking people who would otherwise be deprived of credit, because lenders will judge that these borrowers can be "incentivized" into continuing payments even to the point of total destitution.
This is classic efficient market hypothesis brain worms, the kind of cognitive dead-end that you arrive at when you conceive of people in purely economic terms, without considering the power relationships between them. It's a dead end you navigate to if you only think about things as they are today – vast numbers of indebted people who command fewer assets and lower wages than at any time since WWII – and treat this as a "natural" state: "how can these poors expect to be offered more debt unless they agree to have their all-important pocket computers booby-trapped?"

If you'd like an essay-formatted version of this post to read or share, here's a link to it on pluralistic.net, my surveillance-free, ad-free, tracker-free blog:
https://pluralistic.net/2024/03/29/boobytrap/#device-lock-controller

Image: Oatsy (modified) https://www.flickr.com/photos/oatsy40/21647688003
CC BY 2.0 https://creativecommons.org/licenses/by/2.0/
#pluralistic#debt#subprime#armbreakers#mobile#google#android#apps#drm#technological self-determination#efficient market hypothesis brainworms#law and political economy#gadgets#boobytraps#app stores#curated computing#og app#trusted computing
230 notes
·
View notes
Text
GIS In Our Daily Lives
The involvement of Geographic Information Systems (GIS) in our daily lives is pervasive, influencing and enhancing various aspects across different sectors. The integration of GIS into everyday activities has become integral for decision-making, planning, and optimizing resources. GIS helps city planners and transportation experts to provide them with information like maps, satellite pictures, population statistics, and infrastructure data. GIS helps them make better decisions when designing cities and transportation systems that are sustainable and good for the environment.
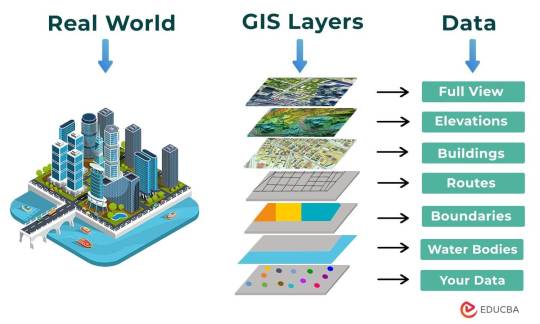
The following points elucidate the notable involvement of GIS in our daily lives:
Navigation and Location Services: GIS provides monitoring functions through the visual display of spatial data and precise geographical positioning of monitored vehicles, whereas GPS provides accurate, clear, and precise information on the position and navigation of a monitored or tracked vehicle in real-time and at the exact location.GIS is at the core of navigation applications and location-based services on smartphones. It enables accurate mapping, real-time navigation, and geolocation services, assisting individuals in finding locations, planning routes, and navigating unfamiliar areas.
E-Commerce and Delivery Services: GIS software is a powerful tool for supply chain network planning. It helps determine the optimal location for distribution centers, warehouses, or other supply facilities. GIS is utilized in logistics and delivery services for optimizing routes, tracking shipments, and ensuring timely deliveries. E-commerce platforms leverage GIS to enhance the efficiency of their supply chain and last-mile delivery processes.
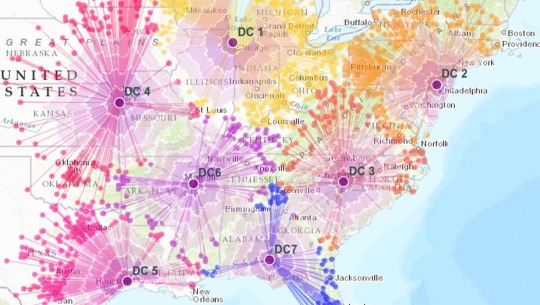
Weather Forecasting and Disaster Management: Many states are using GIS dashboard to monitor the rainfall across the state, on a real-time basis, from the data shared by rain sensors installed at various locationsGIS plays a crucial role in weather forecasting and disaster management. It assists meteorologists in analyzing spatial data, predicting weather patterns, and facilitating timely responses to natural disasters by mapping affected areas and coordinating emergency services.
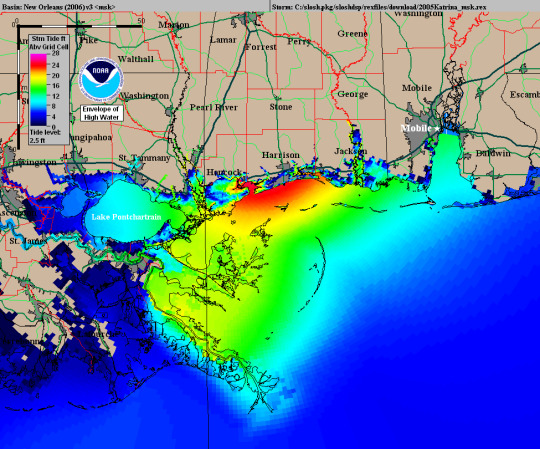
Healthcare Planning and Disease Monitoring: Geographic Information Systems enable the visualization and monitoring of infectious diseases. Additionally GIS records and displays the necessary information that health care needs of the community as well as the available resources and materials. GIS supports public health initiatives by mapping the spread of diseases, analyzing healthcare resource distribution, and assisting in the planning of vaccination campaigns. It aids in identifying high-risk areas and optimizing healthcare service delivery.
Social Media and Geo-tagging: GIS also helps in geotagging and other location related information in posts, it’s tools can map and visualize the spatial distribution of social media activity. This analysis can reveal trends, hotspots, and patterns in user engagement across different geographic areas. Many social media platforms incorporate GIS for geo-tagging, allowing users to share their location and experiences. This feature enhances social connectivity and facilitates the sharing of location-specific information.
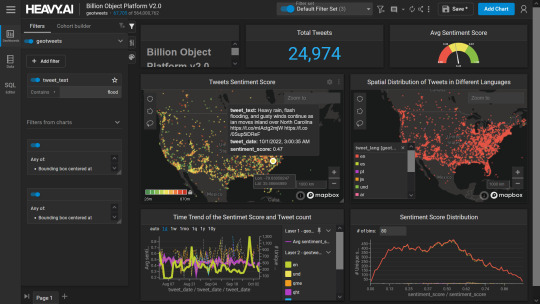
Smart City Initiatives: The Geographic Information System (GIS) offers advanced and user-friendly capabilities for Smart City projects and allows to capture, store and manipulate, analyze and visualize spatially referenced data. It is used for spatial analysis and modeling. It is the cornerstone of smart city planning, enabling the integration of data for efficient urban management. It supports initiatives related to traffic management, waste disposal, energy consumption, and overall infrastructure development.
Education and Research: GIS is increasingly utilized in education and research for visualizing and analyzing spatial data. It enables students and researchers to explore geographic relationships, conduct field studies, and enhance their understanding of various subjects.
Agricultural Management and Precision Farming: Farmers leverage GIS to optimize agricultural practices by analyzing soil conditions, crop health, and weather patterns. Precision farming techniques, facilitated by GIS, contribute to increased crop yields and sustainable farming practices.

Real Estate and Property Management: In the real estate sector, GIS aids in property mapping, land valuation, and site selection. It provides real estate professionals with valuable insights into spatial relationships, market trends, and optimal development opportunities.

Tourism and Recreation: GIS enhances the tourism industry by providing interactive maps, route planning, and location-based information. It assists tourists in exploring destinations, finding attractions, and navigating efficiently.

The broad and varied involvement of GIS in our daily lives underscores its significance as a technology that not only facilitates geographic data analysis but also contributes to the efficiency, safety, and interconnectedness of modern society. As GIS applications continue to evolve, their impact on daily activities is expected to further expand and refine.
#gis#architectdesign#architecture#city#education#geographic information system(gis)#geographical indication
13 notes
·
View notes
Text
10 Web Hosting Terms You Should Know Before Building a Website

If you're planning to create a website, understanding web hosting is essential. If you're looking for a website hosting company in Gurgaon, knowing these terms will help you choose the right provider. Web hosting provides the server space and technology needed to make your website accessible on the internet. However, the world of web hosting can be full of technical jargon that might seem confusing at first. To make informed decisions, here are 10 key web hosting terms you should know:
Control Panel A control panel is a user-friendly interface that allows you to manage your server settings without needing extensive technical skills. It simplifies the process of managing your website, offering tools to configure domains, emails, databases, and security settings. Popular control panels include cPanel and Plesk, which let you handle server tasks through a graphical interface rather than typing complex commands.
Bandwidth Limit Bandwidth refers to the amount of data your website can transfer to and from the server each month. Hosting providers, like a Web hosting company in Gurgaon, set a bandwidth limit to ensure resources are distributed fairly among customers. If your site reaches this limit, your hosting provider might slow down access (throttle it) or even temporarily suspend your site until the next billing cycle. Knowing your bandwidth needs can help you choose the right hosting plan.
Managed Hosting Managed hosting is a type of service where the hosting provider handles essential maintenance tasks for you, such as software updates, security monitoring, and backups. This can save time and effort, especially for those who are less experienced with server management. Managed hosting is an excellent option for businesses that want to concentrate on their main activities while entrusting technical tasks to professionals.
IP Address An IP address is a unique set of numbers assigned to each device connected to the internet, including your hosting server. It acts as an identifier, allowing computers to locate and communicate with each other. When you purchase a hosting plan, your server will be assigned an IP address, which you can use to access your website files, manage the server, and set up remote connections.
Uptime Uptime is a measure of the reliability of your hosting service. It represents the percentage of time that the server is online and accessible. Most reliable providers aim for an uptime of 99.9% or higher. A high uptime rate is crucial because frequent downtime can result in lost traffic and frustrated visitors. Some hosts offer an uptime guarantee, promising compensation if their service falls below the agreed uptime rate.
Shared Hosting
It is an affordable hosting option where multiple websites utilize the same server. Since the cost of running the server is divided among all users, shared hosting are generally inexpensive. However, because resources are shared, high traffic on one website can affect the performance of others on the same server. This makes shared hosting ideal for small websites or those just starting.
VPS (Virtual Private Server) A VPS, or Virtual Private Server, provides a more dedicated portion of server resources compared to shared hosting. Although multiple users still share the physical server, each VPS operates independently, with allocated CPU, RAM, and storage. VPS hosting is a good middle-ground option for websites that need more power and customization than shared hosting can provide, but without the higher cost of a dedicated server.
Dedicated Hosting With dedicated hosting, you have an entire server reserved solely for your website. This means you have full control over all resources, including CPU, memory, and storage, without any competition from other users. Dedicated hosting is the most powerful but also the most expensive option. It’s often used by large businesses or websites with high traffic that require top performance and customization.
Disk Spaced
Disk space, or storage space, refers to the amount of space on a server available for storing your website's files, databases, and other content. The two main types of storage drives are HDDs (Hard Disk Drives) and SSDs (Solid State Drives), with SSDs offering faster performance. When choosing a hosting plan, consider the storage needs of your website, especially if you plan to host high-resolution images, videos, or large files.
11. SSL (Secure Sockets Layer) SSL is a security protocol that encrypts data transferred between your website and its visitors, keeping information secure. To activate SSL, you'll need an SSL certificate, which enables HTTPS for your website, signifying a secure connection. This is particularly crucial for websites that manage sensitive data, like login credentials or payment information. Many web hosting providers in Gurgaon now offer SSL certificates as part of their hosting packages
Conclusion Understanding these web hosting terms will help you make better decisions when setting up your website. Choosing the right hosting plan and knowing the features available can save you time, money, and frustration in the long run. Whether you’re just starting with a small website or launching a large-scale project, familiarity with these terms will make the process smoother and more manageable.
If you want to know more about our services, please feel free to contact us at:
Mobile: 08826196688 or 9910248322
Email: [email protected]
Website: www.deltait.co.in
#website hosting company in Gurgaon#Web hosting company in Gurgaon#web hosting providers in Gurgaon#delta web services
2 notes
·
View notes