#RFID tag reader
Text
Voda IQ: Advanced Fish Farm Management Software with PIT Tag Reader Integration
In the dynamic world of aquaculture, efficiency and precision are crucial for success. As the demand for sustainable and productive fish farming grows, innovative technologies are reshaping the industry. Voda IQ, a leader in fish farm management software, offers a cutting-edge solution that integrates PIT tag reader technology, revolutionizing how fish farms operate and thrive.

The Importance of Advanced Fish Farm Management
Fish farming, or aquaculture, is a rapidly growing sector, providing nearly half of the global fish supply. However, managing a fish farm is no simple task. It involves monitoring water quality, feeding schedules, health assessments, and ensuring optimal growth conditions for the fish. Traditional methods can be labor-intensive and prone to errors, making advanced management tools essential.
Voda IQ addresses these challenges by offering a comprehensive fish farm management software designed to streamline operations, reduce costs, and enhance productivity. One of the standout features of Voda IQ is its integration with PIT tag readers, a technology that brings unparalleled precision and efficiency to fish tracking and management.
What is a PIT Tag Reader?
PIT (Passive Integrated Transponder) tags are small, electronic devices that can be implanted in fish to provide unique identification. These tags are read by PIT tag readers, which use radio frequency signals to detect and retrieve data from the tags. The use of PIT tags and readers in aquaculture allows for accurate tracking of individual fish, enabling better management of fish health, growth, and breeding programs.
Benefits of Integrating PIT Tag Readers with Voda IQ
Enhanced Tracking and Data Collection
With PIT tag reader integration, Voda IQ offers fish farmers a powerful tool to monitor individual fish throughout their lifecycle. This technology allows for real-time data collection on fish movements, growth rates, and health status. By having detailed records of each fish, farmers can make informed decisions to optimize their operations.
Improved Health Management
Disease outbreaks can devastate fish farms, leading to significant economic losses. Early detection and intervention are crucial. Voda IQ's software, combined with PIT tag readers, enables continuous health monitoring of fish. Any abnormalities or signs of illness can be detected early, allowing for prompt treatment and preventing the spread of disease.
Efficient Feeding Practices
Feeding is one of the most critical aspects of fish farming, directly impacting growth rates and overall farm productivity. Overfeeding can lead to wasted resources and poor water quality, while underfeeding can stunt fish growth. Voda IQ's software can analyze data from PIT tag readers to optimize feeding schedules, ensuring each fish receives the right amount of food based on its specific needs.
Streamlined Breeding Programs
Selective breeding is essential for improving fish stock quality and achieving desirable traits such as faster growth rates and disease resistance. By tracking genetic information and breeding histories using PIT tags, Voda IQ helps farmers implement effective breeding programs. This leads to higher quality fish and more efficient production cycles.
Voda IQ's Commitment to Sustainability
Sustainability is a core value at Voda IQ. By providing fish farmers with advanced tools to optimize their operations, Voda IQ contributes to more sustainable aquaculture practices. The use of PIT tag readers reduces waste, improves resource efficiency, and minimizes environmental impact. Furthermore, better health management and disease prevention lead to healthier fish stocks and more stable ecosystems.
Getting Started with Voda IQ
Adopting Voda IQ's fish farm management software with PIT tag reader integration is a straightforward process. Here are the steps to get started:
Assessment and Consultation: Voda IQ's team of experts will assess your farm's specific needs and provide a tailored solution.
Installation and Training: The software and PIT tag readers will be installed, and comprehensive training will be provided to ensure seamless integration into your existing operations.
Ongoing Support: Voda IQ offers continuous support and updates to keep your farm running smoothly and efficiently.
Conclusion
In the ever-evolving field of aquaculture, staying ahead requires embracing innovative technologies. Voda IQ's advanced fish farm management software, integrated with PIT tag reader technology, offers a game-changing solution for fish farmers. By enhancing tracking, health management, feeding practices, and breeding programs, Voda IQ empowers farmers to achieve greater efficiency, productivity, and sustainability.
0 notes
Text
RFID Tags: Revolutionizing Identification and Tracking

In today's fast-paced world, efficiency and accuracy are paramount. Radio Frequency Identification (RFID) tags have emerged as a game-changing technology, offering a streamlined and reliable solution for identification and tracking across a wide range of industries. These tiny tags, embedded with microchips and antennas, can store and transmit data wirelessly, enabling seamless tracking of assets, inventory, and personnel.
The Significance of RFID Tags
RFID tags have revolutionized various sectors due to their unique advantages:
Enhanced Efficiency: RFID tags eliminate the need for manual scanning or barcode reading, significantly reducing time and labor costs.
Improved Accuracy: RFID tags provide error-free identification, eliminating the potential for human error often associated with manual data entry.
Real-time Tracking: RFID tags allow for real-time tracking of assets, enabling businesses to monitor their inventory and optimize their supply chain.
Versatility: RFID tags can be attached to a wide range of objects, from clothing and electronics to livestock and vehicles, making them a versatile solution for various applications.
A World of Applications
RFID tags have permeated various industries, transforming operations and enhancing efficiency. Here are some notable examples:
Supply Chain Management: RFID tags streamline inventory management, enabling real-time tracking of goods throughout the supply chain, from manufacturing to distribution.
Access Control: RFID tags enable secure access control systems, granting authorized personnel access to restricted areas or buildings.
Asset Tracking: RFID tags are widely used to track valuable assets, such as medical equipment, library books, and industrial tools, preventing theft and loss.
Animal Tracking: RFID tags are employed for animal identification and tracking, providing valuable insights into livestock management, wildlife conservation, and research.
Retail: RFID tags enhance retail operations, enabling efficient inventory management, loss prevention, and personalized customer experiences.
SB Components: Your One-Stop Shop for RFID Tags
SB Components is a leading provider of high-quality RFID tags, catering to the diverse needs of businesses and individuals. Our extensive range of RFID tags includes a variety of frequencies, sizes, and functionalities to suit specific applications.
Whether you're looking to track inventory, manage access control, or enhance customer experiences, SB Components has the RFID tags that meet your requirements. Our expert team is always ready to assist you in selecting the right RFID tags for your unique needs.
Embrace the Future with RFID Technology
RFID tags have revolutionized identification and tracking, offering a powerful and versatile solution for businesses and individuals alike. As technology continues to advance, RFID tags are poised to play an even more significant role in streamlining operations, enhancing efficiency, and improving decision-making across industries.
To explore the vast potential of RFID tags, visit SB Components today and discover the innovative solutions that await you.
#rfid tags#rfid chip#rfid sticker#rfid nfc#rfid labels#rfid in iot#tag reader#rfid tag reader#rfid tag for car#rfid tag price#active rfid#rfid asset tracking#passive rfid tags#rfid tags for inventory#rfid decathlon#active rfid tag
0 notes
Photo

RFID readers are used to collect data from tags for asset tracking. Reader collects data from tags even if it is far from it. The data is in form of radio waves that can not be read by humans. You can say RFID technology is very similar to bar codes. RFID readers are used in many applications like smart cards, toll booth passes, merchandise tags, monitoring heart patients, and many more. ID Tech Solution is the leading supplier and manufacturer of RFD readers in India. You can check their website to know more about RFID tag readers.
0 notes
Text
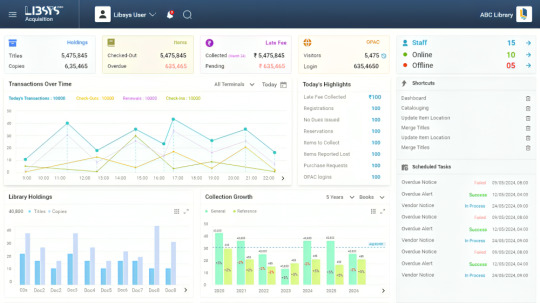
RFID library Automation for tracking, security and inventory management
LIBSYS Limited, a software as a service(SAAS) company based in Gurugram, Delhi-NCR, India, was founded in 1984 by Mr. Anil Jain to cater the needs of Identity, Tracking and Security purpose for various Indian industries. With the aim to automate the process and minimizing the human errors to zero, the Libsys offers a wide range of solutions that include Library Management Systems for institutions and government bodies, RFID based customized applications from small business to multinational organizations, Common Admission Platform and ERP for Academic Institutes, Omni-channel Retailing solution, E-Commerce Framework, CRM, Design & Architecture and other on demand solutions.
The experience of 40 years and counting along with in-depth understanding of the Indian markets, we are the proud leaders of quality and innovation. Through the experience we have, we have the ability to respond quickly to the customized client requirements with an innovative solutions that meet those needs efficiently and cost effectively. Our experience and strong mission-first work ethic has helped us develop capabilities, insights, and skills to provide the best solution one can have. Backed by our strong quality processes and rich experience in managing clients across various domains, we strive for continuous innovations in our offerings, and we take pride in being the pioneer and market leader for RFID based automation solution in India.
To name a few, software products like LIBSYS 10 LMS, LSEase, LSmart-RFID, LSRemote, LSDiscovery, LSe-RMS, symphonyX, TargetX, LSNetX (E-Com) and LSales1 CRM are the benchmarks in India serving across the domains and delivering the best operational efficiency solutions for all organizations and enterprises.
TRANSFORMING LIBRARIES
Elevate your Library
LIBSYS 10 caters to all the needs of library automation improving the efficiency of libraries and providing a delightful library experience through continuous technological innovations
Smooth Library Operations
LIBSYS 10 simplifies and automates essential library management tasks, allowing for efficient cataloging, circulation, and inventory management.
Enhanced Accessibility
Libsys 10 offers a user-friendly interface and robust search capabilities, enabling patrons to easily discover and access library resources.
Comprehensive Reporting
Libsys 10 generates detailed reports on library usage, collection statistics, and circulation trends, facilitating decision-making and resource allocation
Seamless Integration
Libsys 10 seamlessly integrates with various library systems, ensuring smooth interoperability and minimizing disruptions in existing work-flows
LIBSYS10
LIBRARY MANAGEMENT SIMPLIFIED
Step into the future
A web based library management solution to enhance the total library experience through value added features and services.
The present times demand Library Management System to deliver much more than operational efficiency. It needs to create appreciable staff satisfaction and a delightful experience for the patrons every time they interact with the system. LIBSYS is committed to delivering value to the libraries through its products. In-depth understanding of library operations, implicit needs of the patrons, and dedicated R&D efforts have guided us to deliver high-quality products that have found wide acceptance in the market space.
Its seamless work-flow enables library staff to manage library operations efficiently.
New purchase approvals, collection development, material handling, SDI services, bindery management, and a host of other functions form an integral part of the system.
MARC21 / RDA interface, Cooperative Cataloguing along with controlled authority files helps in Cataloguing on the fly.
Federated Searching brings other libraries of similar collection within your reach.
REQUEST A DEMO
MODULES
GO BEYOND THE LIBRARY
Modernize Your Library
LIBSYS 10 is a smart library management system covering all the needs of library automation in India and abroad.
Acquisition
LIBSYS 10 automated library acquisition system is capable of efficiently managing all kinds of work-flow
Cataloguing
Catalogue your records smarter and faster way with user friendly yet powerful cataloguing module.
Serial Control
Easily control and maintain your library’s serials collection in the most efficient way.
Circulation
Easy and powerful interface to handle circulation transactions, alerts, greetings, reminders, fine etc.
KEY FEATURES
Check Out Capabilities
LIBSYS 10 is a feature-rich Library Management System that empowers libraries to effectively manage their collections, streamline operations, provide enhanced services to patrons, and embrace modern technologies for a seamless library experience. Our automated acquisition system in library reduces time consuming work and enhances the overall efficiency in ordering and provides necessary management information reports.
Online Public Access Catalog (OPAC)
Digital Resource Management
Reporting and Analytics
Integration and Interoperability
Mobile Accessibility
BENEFITS
30+ YEARS
Scale Your LMS
LIBSYS 10 empowers libraries to optimize their operations, improve user satisfaction, and adapt to evolving technological advancements in the library field. It enhances the overall library experience for both librarians and patrons.
Streamlined Operations
Libsys 10 automates various library tasks, reducing manual efforts and saving time for librarians.
Efficient Resource Management
The system helps librarians effectively manage library resources, including books, journals, multimedia, and digital materials.
Enhanced User Experience
Libsys 10 enhances the experience for library patrons through its user-friendly OPAC interface.
Accessibility Anytime, Anywhere
Libsys 10's mobile accessibility ensures that library services and resources are available to patrons anytime, anywhere.
LIBSYS10
HARNESS THE POTENTIAL OF OUR LIBRARY MANAGEMENT SYSTEM!
#1 Library Management System
Unlock the Power of Efficiency and Innovation with Libsys
The present times demand Library Management System to deliver much more than operational efficiency. It needs to create appreciable staff satisfaction and a delightful experience for the patrons every time they interact with the system. LIBSYS is committed to delivering value to the libraries through its products. In-depth understanding of library operations, implicit needs of the patrons, and dedicated R&D efforts have guided us to deliver high-quality products that have found wide acceptance in the market space.
The new Web-based Library Management System ‘LIBSYS 10’ provides a greatly enhanced user experience through value-added features and services. LIBSYS 10 is built on international standards and open technologies, i.e. JAVA. It covers Acquisition, Cataloguing, Circulation, Serials, Articles Indexing, E-Books, Dean and Vendor Portals along with an enriched OPAC. Its seamless work-flow enables library staff to manage library operations efficiently. New purchase approvals, collection development, material handling, SDI services, bindery management, and a host of other functions form an integral part of the system. MARC21 / RDA interface, Cooperative Cataloguing along with controlled authority files helps in Cataloguing on the fly. Federated Searching brings other libraries of similar collection within your reach.
LIBSYS 10 gives you the opportunity to take your automated library circulation system to new heights by use of RFID / EM / Hybrid Technology. Choose LSmart / KSmart system as per your budget and requirements. Use of these technologies will help in hassle free, accurate and faster issue / return of books, inventory visibility, accuracy and efficiency, increases security function in the library, improved utilization of resources like manpower, infrastructure etc., give flexible library timings. The bottom line is that the synergy between the latest technology like RFID and libraries can create wonders resulting in empowerment of both users as well as librarians.
LIBSYS Library Management System in India has been deployed in many prestigious institutes. LIBSYS 10 caters to all the needs of library automation improving the efficiency of libraries and providing a delightful library experience through continuous technological innovations. With rich experience of more than three decades along with continuous innovation, LIBSYS has emerged as the best library management system in India.
We also undertake special projects which include multi-location library automation and RFID system implementation. The projects are executed by specialized teams comprising of experienced professionals from Library and IT domains. Our customer-focused services also include consulting to meet individual needs, organizing User meets, and providing regular software updates.
For more details connect at [email protected] or +91-0124-4894100
#rfid#rfid solutions#rfid technology#rfid reader#rfid tags#library#inventorymanagement#inventory software#assets#assetprotection#assetmanagement#tracking tag#data security#software#technology#trackinghome#cyber security#social security#cybersecurity
2 notes
·
View notes
Text
Why RFID Jewelry Tags Are Essential for Jewelry Showroom Management

Jewelry showrooms, known for displaying high-value and exquisite pieces, face unique challenges regarding inventory management, security, and efficient customer service. Managing hundreds or even thousands of high-end items manually can be overwhelming, time-consuming, and prone to human error. Enter RFID (Radio Frequency Identification) technology, transforming jewelry showrooms' operation. RFID jewelry tags are revolutionizing showroom management by providing seamless tracking, improving security, and offering real-time inventory updates.
The Role of RFID Tags in Jewelry Showrooms
RFID tags, when applied to jewelry pieces, contain a tiny chip and antenna that transmit data wirelessly to a reader. This technology has seen widespread adoption across various industries, and in jewelry showrooms, RFID systems offer tremendous benefits. These RFID jewelry tags can be attached to individual pieces like rings, necklaces, and watches, allowing the system to track their precise location within the store.
One of the most compelling features of RFID technology is that it can automatically scan multiple tags simultaneously, even through barriers like glass. This means that entire sections of jewelry can be tracked and counted instantly, providing real-time updates on the showroom’s inventory.
Key benefits of RFID Tags for jewelry stores:
1. Real-Time Inventory Management
One of the primary reasons RFID jewelry tags have become essential is their ability to provide real-time inventory updates. In traditional inventory systems, counting high-value items like jewelry is a manual and labor-intensive process. Employees must often scan each piece individually, which increases the risk of errors, missed items, or inconsistencies.
With RFID tags, the system can automatically track each piece’s exact location and status. Whether a piece has been moved from a display case, returned to storage, or sold to a customer, the system updates in real time. Say goodbye to manual counting and rest easy knowing that your inventory is always accurate. As a result, jewelry showrooms can significantly reduce time spent on inventory management, freeing up staff to focus on providing personalized customer service.
2. Enhanced Security and Theft Prevention
Jewelry showrooms are often targeted for theft because of the high value of the items on display. Keeping a close eye on every piece at all times is nearly impossible, but RFID jewelry tags offer a robust security solution. RFID systems allow showroom managers to monitor the movement of jewelry in real time, setting off alerts if any piece is moved without authorization or taken outside the designated zone.
The technology can also track who accessed the item and when helping create a traceable record of each piece’s movement within the showroom. This makes it easier to identify and prevent theft or unauthorized handling. RFID tags also offer an additional layer of protection when coupled with anti-theft alarms and security cameras, making it far more difficult for criminals to steal high-value items unnoticed.
3. Improved Customer Experience
In addition to improving security and inventory control, RFID technology can significantly enhance the overall customer experience. When a customer visits a jewelry showroom, they expect personalized service, and with RFID jewelry tags, staff can deliver just that. Showroom employees can quickly locate any piece of jewelry in the store by scanning the RFID system. This rapid retrieval saves time, especially during busy periods, allowing employees to provide better and faster service to customers.
Furthermore, RFID technology can be integrated into customer-facing systems, offering personalized recommendations or detailed product information with just a tap. For example, when a customer shows interest in a particular piece, the RFID tag can instantly pull up detailed information about the jewelry, such as its design, materials, pricing, and available sizes. This speeds up the sales process and enhances the overall shopping experience by offering quick, relevant information tailored to the customer’s needs.
4. Seamless Inventory Audits
Regular inventory audits are necessary to ensure the showroom’s stock matches sales records. However, manually auditing jewelry can be both time-consuming and prone to errors, especially when dealing with high-value collections. RFID jewelry tags simplify this process significantly.
Instead of manually counting each piece and matching it against records, RFID readers can scan an entire collection in a matter of minutes. This not only improves accuracy but also reduces the time required for audits from hours or even days to just a fraction of that time. Jewelry showrooms can conduct more frequent audits without interrupting daily operations, ensuring that inventory data is always up-to-date and accurate.
5. Efficient Product Tracking
Tracking individual pieces of jewelry is one of the biggest challenges in showroom management. Pieces may be moved frequently between display cases, stock rooms, and customers, making it hard to keep track of their exact location at any given time. RFID tags allow showroom managers to know precisely where each item is, whether it's in a display case, out for cleaning, or being shown to a potential buyer.
This efficient tracking system reduces the chances of items being misplaced, saving time and reducing the risk of losses. It also provides valuable insights into which pieces are more frequently handled or requested, helping managers optimize their display strategies to showcase the most popular items.
6. Scalability for Growing Businesses
As a jewelry business grows, managing larger inventories can become increasingly challenging. RFID jewelry tags offer a scalable solution that grows with the business. Whether a showroom has a few hundred or several thousand pieces, the RFID system can handle the increased volume without losing efficiency. This makes it an excellent long-term investment for businesses looking to expand their product offerings or open multiple locations.
Conclusion The adoption of RFID jewelry tags is transforming jewelry showroom management, providing benefits that go beyond simple tracking. From real-time inventory management and improved security to enhanced customer experiences and efficient audits, RFID technology is becoming an essential tool for modern jewelry businesses. As the jewelry industry continues to evolve, RFID tags offer a reliable, scalable, and secure solution for managing high-value items with ease. Embracing this technology not only boosts operational efficiency but also helps create a seamless, personalized experience for customers, ensuring success in today’s competitive retail landscape.
#rfid technology#rfid solutions#rfid tags#RFID Jewelry Tags#UHF RFID Tags#rfid reader#inventory management#rfid tags manufacturers#handheld scanner
0 notes
Text
RFID Technology
The Pervasive Use of RFID Technology: Convenience at a Cost

What is RFID Technology?
RFID technology automatically recognizes and tracks tags affixed to things using electromagnetic fields. These tags can be found as close as a few millimeters or as far away as several meters away from RFID readers, which can read the electrically stored information on them. RFID tags are much more flexible for a variety of applications than barcodes since they may be read without a direct line of sight.
RFID tags come in two primary varieties: passive and active. While active RFID tags have their own power source and can communicate data over greater distances, passive RFID tags depend on the energy from the RFID reader to power the tag and transfer data. RFID is widely utilized in the retail, transportation, logistics, healthcare, and even personal identity systems such as credit cards and passports.
The Convenience of RFID Technology
Unquestionably, RFID technology has improved convenience in a lot of areas of life. RFID tags, for example, facilitate faster checkout times and more effective inventory control in the retail industry. Stock levels can be automatically monitored by stores, which lowers the possibility of out-of-stock merchandise and improves inventory forecasting. On the other hand, customers gain from quicker transactions and shorter checkout lines.
RFID technology is essential for controlling toll collection, operating public transit, and even tracking automobiles for fleet management in the transportation industry. For instance, RFID tags put to vehicles enable automated toll collection, saving drivers from having to pull over and make the payment by hand. In addition to saving time, this lessens traffic jams.
Another industry where RFID technology has shown to be quite beneficial is healthcare. RFID tags are utilized in pharmaceutical inventory management, patient monitoring, and medical equipment tracking. RFID technology lowers the possibility of mistakes in hospitals, such as giving the wrong prescription or misplacing vital medical equipment. This increases overall healthcare facility efficiency while simultaneously improving patient safety.
To Get RFID Technology:JOIN NOW
The Dark Side of RFID Technology
Despite the obvious advantages of RFID technology, there are drawbacks to its extensive application, especially in terms of security and privacy. The same ease of use that draws so many people to RFID technology also renders it vulnerable to abuse and exploitation.
Privacy Concerns
The possibility of illegal access to personal data is one of the biggest issues with RFID technology. RFID tags are frequently incorporated into everyday objects that individuals carry with them, including credit cards, passports, and even clothes. There is a chance that nefarious actors could obtain private information as RFID tags can be read from a distance without the owner’s knowledge or consent.
Think of a situation at a busy mall, for instance. Without your knowledge, someone using a covert RFID reader at the mall may be able to scan the RFID tags on your passport or credit cards and obtain personal information. Fraud or identity theft could then be perpetrated using this information. While RFID tags usually have a restricted range, technological advancements have allowed some RFID readers to read data at longer ranges, which raises the possibility of unwanted access.
Furthermore, there are other applications for RFID technology that people might not even be aware of. For example, retailers employ RFID tags to monitor customer activity, such as the length of time a customer spends in a specific area of the store or the products they pick up and inspect. Although this information is useful for marketing, the collecting and analysis of personal data without express agreement creates serious privacy concerns.
Security Risks
RFID technology poses a number of security vulnerabilities in addition to privacy issues. Among the most well-known is the risk of RFID tag spoofing or cloning. RFID tags use wireless technology to transfer data, which makes it feasible for a malevolent actor to intercept and copy the signal, producing a cloned tag that can be used fraudulently.
For example, if a credit card includes RFID capabilities, it is possible for an attacker to copy the RFID tag on the card and use it to make fraudulent payments. Similar to this, an attacker may copy an RFID badge in an access control system and enter restricted areas without authorization. Attacks of this nature have serious repercussions, especially in places like financial institutions and government buildings where security is vital.
The possibility of denial-of-service (DoS) attacks is another security concern connected to RFID technology. A denial-of-service (DoS) assault occurs when a malevolent party floods an RFID system with signals, preventing it from operating as intended. This might cause serious delays or even put lives in danger by interfering with vital operations in industries like transportation and healthcare.
Mitigating the Risks of RFID Technology
Although RFID technology carries some risks, people and organizations can take a number of precautions to lessen these risks and safeguard their security and privacy.
Enhancing Privacy
The adoption of RFID-blocking materials is one of the best ways to handle privacy concerns. Wallets, sleeves, and bags that block RFID signals are made to prevent unwanted RFID tag scanning. These goods are made of a unique substance that obstructs the radio frequencies needed to read RFID tags, stopping unwanted access to private data.
Apart from adopting physical security measures, people can also reduce the quantity of personal data that is kept on RFID-capable gadgets. To lower the possibility of unwanted access, certain credit card firms, for instance, provide customers the choice to turn off the RFID feature on their cards. Personal privacy can also be greatly enhanced by being aware of the RFID technology incorporated into commonplace objects and by adopting the necessary safety measures.
On the other hand, businesses should put in place stringent data privacy guidelines and make sure that any data collected using RFID technology is done so openly and with the participants’ consent. Retailers and other companies must to educate clients in a straightforward manner about how their data is being used, and if at all feasible, allow them the opportunity to opt out.
Strengthening Security
Investing in encryption and authentication measures is recommended for enterprises to mitigate the security risks connected with RFID technology. The data transmitted by RFID tags is protected from illegal access via encryption, and only authorized RFID readers can access the data thanks to authentication measures.
The use of RFID kill codes is a crucial additional security measure. An RFID tag can be rendered unreadable by permanently deactivating it using a kill code. When there is a chance of unwanted entry or when an RFID tag is no longer required, this can be helpful.
Companies should regularly evaluate the security of their RFID systems in order to find and fix any flaws. This entails making sure that all RFID systems and devices are up to date with the most recent security patches and testing for popular attack vectors like cloning and spoofing.
To Get RFID Technology:JOIN NOW
The Future of RFID Technology
RFID applications are expected to grow much more as the technology develops, posing both new possibilities and difficulties. RFID technology is anticipated to be important in the development of the Internet of Things (IoT), which will allow common things to connect and communicate with each other effortlessly.
But as RFID technology becomes more widely used, strong privacy and security safeguards will also become more important. Like with any technology, the secret is to take a balanced strategy that takes into account both the possible expenses and the convenience of RFID in order to maximize its benefits while limiting its hazards.
Conclusion
Without a doubt, RFID technology has changed many facets of our life and provided unmatched convenience in a variety of sectors, including healthcare and retail. But there is a price for this convenience, especially when it comes to security and privacy. As RFID technology spreads, it is critical to maintain vigilance and take the necessary precautions to guard against potential risks.
We may continue to reap the rewards of this useful tool while protecting our security and personal data by being aware of the hazards connected with RFID technology and putting mitigation measures in place. In an increasingly connected world, it is imperative that we strike a balance between adopting new technologies and preserving the security and privacy that are fundamental to our well-being.
To Get RFID Technology:JOIN NOW
1 note
·
View note
Text
Understanding RFID Protectors: A Comprehensive Guide to Safeguarding Your Personal Information
It is more important than ever to protect our personal information in today’s increasingly digital environment. The risk of unwanted access to our private information has increased with the popularity of contactless payment cards, electronic passports, and other products based on RFID (Radio Frequency Identification) technology. This is the situation in which RFID shields are useful. These straightforward yet powerful gadgets are becoming necessary tools for everyone trying to protect their data from online dangers. We’ll discuss what RFID protectors are, how they function, and why you might need one in this post.
What is RFID Technology?
RFID, or radio frequency identification, is a technology that automatically recognizes and tracks tags affixed to items using electromagnetic fields. These tags have the capacity to hold a variety of data, including your credit card number, passport information, and even health information. RFID is a common technology found in numerous products, such as:
Credit and Debit Cards: A lot of cards now have RFID chips installed, enabling contactless transactions.
Passports: More recent passports come with inbuilt RFID chips that hold biometric and personal data.
Access Cards: To regulate access, a lot of offices and structures employ RFID-enabled access cards.
RFID technology carries some concerns even though it is convenient. Since RFID tags may be read without physical contact, your information could be accessed without your knowledge by someone with the appropriate tools.
Note: Secure your data with a simple shield — because in today’s world, peace of mind is priceless.

The Risks of RFID Technology
The possibility of “skimming,” or unauthorized access to your data, is the main concern connected with RFID technology. Skimming is the process of using a gadget to intercept an RFID chip’s signal and obtain the data that is stored on it. This might result in:
Identity Theft: Your name, address, social security number, and other personal information may be taken and used to open phony accounts.
Financial Theft: Should someone manage to obtain your credit card details, they may use them to make fraudulent transactions or even take money out of your account.
Privacy Invasion: You run the risk of having sensitive information, like medical records or trip itinerary, obtained and exploited against you from RFID-enabled products.
Because of these dangers, it’s critical to keep your RFID-enabled products safe from harm.
What is an RFID Protector?
An RFID protector, sometimes referred to as an RFID blocking card, wallet, or sleeve, is a tool made to stop unwanted access to your data by blocking the electromagnetic fields utilized in RFID technology. The materials used to make these guards put an obstruction between the RFID chip and any possible skimming equipment. Typical varieties of RFID shields consist of:
RFID Blocking Wallets: Wallets with integrated RFID blocking technology are known as RFID blocking wallets. They have an additional layer of security but still look and work like standard wallets.
RFID sleeves: You can slip your passports or credit cards into these slender, protective sleeves. They are simple to carry and small in weight.
RFID blocking cards: You can carry these cards in your wallet with your regular cards. By emitting a signal that interferes with RFID signals, they prevent skimmers from accessing your personal information.

How Does an RFID Protector Work?
Materials that can obstruct or jumble the electromagnetic fields needed to read RFID tags are utilized in RFID protectors. These substances, which are frequently composed of metals like copper or aluminum, enclose the RFID chip in a Faraday cage. A Faraday cage is a device that, by dispersing charge throughout the cage, blocks electromagnetic fields and keeps them from reaching the objects inside.
An RFID protector will cover an RFID-enabled device, like a credit card, from external electromagnetic fields when the protector is placed within it. This implies that your information will be protected even if someone tries to access it by using a skimming device to scan your card.
Why You Might Need an RFID Protector
While not necessary for everyone, an RFID protector can offer additional security and peace of mind for some. The following are some explanations on why you should use an RFID shield:
1. Frequent Traveler
If you travel a lot, especially abroad, you probably have an RFID chip in your passport. Your personal and travel information can be protected from unwanted access with an RFID protector, which is especially crucial in crowded places like train stations and airports.
2. Concerned About Identity Theft
An RFID protector can offer an additional degree of protection if identity theft is a worry. Your driver’s license, credit cards, and any other RFID-enabled objects you carry with you can all be better protected.
3. Regular Use of Contactless Payment Cards
Use of contactless payment cards increases your vulnerability to skimming. Your financial information is protected and fraudulent transactions can be avoided with the use of an RFID protector.
4. Carrying Sensitive Information
An RFID protector can help keep sensitive information safe if you carry any things containing RFID chips that hold data, such as access cards or medical records.
Types of RFID Protectors
There are various kinds of RFID protectors available, and each has benefits of its own. Here are a few of the most well-liked choices:
1. RFID Blocking Wallets
These wallets are available in a variety of designs and materials, including as leather and synthetic fabrics, and have integrated RFID-blocking technology. Because they combine the features of a standard wallet with the extra security of RFID protection, RFID-blocking wallets are practical.
2. RFID Sleeves
RFID sleeves are thin, light covers that fit over individual credit cards and identification cards. For those who wish to safeguard particular goods without changing their entire wallet, they are perfect. RFID sleeves are simple to use and reasonably priced.
Note: Secure your data with a simple shield — because in today’s world, peace of mind is priceless.
3. RFID Blocking Cards
The purpose of RFID blocking cards is to fit them in your wallet with your other cards. Any attempt to scan your cards is interfered with by a signal they generate. If you want to maintain the security of RFID blocking but still want to use your existing wallet, these cards are a suitable choice.
4. RFID Blocking Purses and Bags

How to Choose the Right RFID Protector
How to Choose the Right RFID Protector
Take into account the following elements while selecting an RFID protector:
1. Quality of Material
The RFID protector’s material quality is very important. Seek for shields composed of premium metals such as copper or aluminum, which are renowned for their potent electromagnetic shielding capabilities.
2. Size and Compatibility
Make sure the items you wish to protect are the proper size for the RFID protection. For example, seek for an RFID wallet or sleeve made specifically to handle passports if you need to protect one.
3. Style and Design
RFID guards are available in a range of shapes and sizes, from beautiful and traditional to sleek and contemporary. Select the option that best fits your tastes and style.
4. Durability
It’s critical to select an RFID protector that is robust and resistant to normal wear and tear because you will be utilizing it on a regular basis.
5. Brand Reputation

Common Myths About RFID Protectors
There are a number of false beliefs and misunderstandings regarding RFID shields that could be confusing. Let’s address a few of the most prevalent ones:
1. Myth: Only Expensive RFID Protectors Work
Factual statement: Efficacy cannot always be determined by price. Numerous reasonably priced RFID protectors are equally effective as more costly ones. The secret is to seek excellent content and reviews.
2. Myth: RFID Skimming is Extremely Common
Factual statement: RFID skimming is not as frequent as some people think, yet it is still a possible hazard. But there is still a chance, particularly for frequent travelers and those who use contactless transactions.
3. Myth: All RFID Chips Are Vulnerable to Skimming
Factual statement: Not every RFID chip is susceptible to skimming. Modern technologies employ encrypted transmissions, which are considerably more difficult to intercept. Many older RFID chips are still susceptible, though.
4. Myth: You Can Use Any Metal Object as an RFID Protector

Final Thoughts
RFID protectors provide a quick and easy solution to protect our data in a time when unlawful access to our personal information is becoming more common. An RFID protector can give you extra security and peace of mind whether you’re worried about identity theft, travel frequently, or use contactless payment cards on a regular basis. To make sure the RFID protector you select suits your demands, take into account the product’s type, quality, and durability. Even while RFID skimming isn’t the most frequent type of data theft, it’s still a risk that should be avoided, particularly as RFID technology spreads. Purchasing a trustworthy RFID protector is a simple action that can significantly impact the security of your personal data. By remaining knowledgeable, When exercising prudence, you can take advantage of RFID technology’s convenience without having to worry about possible risks.

1 note
·
View note
Text
0 notes
Text
Find document, Files all at once

Introducing File Tracker – your ultimate solution to the frustrating hunt for missing files.
Say goodbye to endless searches and hello to instant access with our streamlined IoT technology. With File Tracker, locating important documents is a breeze, thanks to the user-friendly interface and seamless cross-device compatibility.
Don't let file chaos slow you down. Try File Tracking system today and experience the ease of efficient file management.
#file tracking#rfid tags#file management#file tracking software#file tracking system#tracking tag#barcode tracking#rfid solutions#rfid technology#rfid#office file#barcodescanners#rfid reader#mobile scanner
0 notes
Text
5 Facts You Need To Know About Active RFID Readers

In the rapidly evolving world of RFID technology, Active RFID readers stand out for their exceptional capabilities. Whether you’re new to RFID or looking to upgrade your system, understanding the benefits and features of active RFID readers can help you make informed decisions. Here are five essential facts about Active RFID readers that you need to know.
0 notes
Text
#alphatechsusa#cafeteria keypads#cafeteria pin pads#school cafeteria keypads#school lunch keypads#school cafeteria pin pads#alphatechs usa#keypads#cafeteria keypad#custom keypads#rfid#rfid tags#rfid technology#rfid reader#rfid solutions
0 notes
Text

Paradip Port, a pivotal maritime hub, is embracing the future of port operations with ID Tech, a leader in advanced automation. In a transformative collaboration, Paradip Port is leveraging ID Tech's cutting-edge solutions to usher in the era of Port 4.0 innovation. This partnership marks a significant milestone in the port's journey towards modernization and efficiency.
D Tech is a leading provider of advanced technology solutions that enable businesses to achieve greater efficiency, productivity, and profitability. With a focus on innovation and quality, ID Tech provides customized solutions that meet the unique needs of its customers. For more information on the innovative uses of RFID technology, please visit our website at https://www.idsolutionsindia.com/
0 notes
Text

UHF/RFID Reader
UHF/RFID Reader
for :
Logistics
Warehouse
Inventory
Etc.
0 notes
Text
Implementing an RFID library management system can revolutionize how libraries operate, offering efficiency, accuracy, and convenience for both librarians and patrons. Here's a breakdown of the components and benefits of such a system:
Components of an RFID Library Management System:
RFID Tags: Each book is affixed with an RFID tag containing unique identification information.
RFID Readers: Installed at strategic locations such as entrance/exit gates, self-checkout stations, and shelves, RFID readers communicate with the tags wirelessly.
Database Management System: Stores information about each book, including its title, author, location, and status (e.g., available, checked out).
Software Interface: Provides a user-friendly interface for librarians to manage the system, including adding new books, updating records, and generating reports. It also includes a front-end for patrons to easily check out and return books.
Security System: Integrates with the RFID system to detect unauthorized removal of library materials.
Benefits of RFID Library Management Systems:
Automation: RFID systems automate many tasks, reducing the manual workload for librarians. This includes inventory management, self-checkout, and security monitoring.
Efficiency: With RFID technology, multiple books can be scanned simultaneously, drastically reducing the time needed for tasks like inventorying shelves or checking out multiple items.
Accuracy: RFID systems are highly accurate in identifying and tracking items. This reduces errors in inventory management and ensures that books are properly checked out and returned.
Improved Patron Experience: Self-checkout stations and faster checkout processes enhance the overall experience for library patrons, reducing waiting times and improving satisfaction.
Enhanced Security: RFID tags can be integrated with security gates to prevent theft. If a book hasn't been properly checked out, the system can trigger an alarm when it passes through the gate.
Data Insights: The system collects data on book circulation, popular titles, and patron behavior. Librarians can use this information to make informed decisions about collection development and resource allocation.
Accessibility: RFID systems can be integrated with accessibility features such as audio instructions and tactile interfaces, making the library more inclusive for patrons with disabilities.
Remote Management: Librarians can access the system remotely, allowing them to perform tasks such as inventory management or generating reports from anywhere with an internet connection.
Overall, implementing an RFID library management system can streamline operations, improve accuracy, and enhance the overall library experience for both staff and patrons.
For more details visit: https://www.libsys.co.in/ or write @ [email protected] or +911244894100
#rfid solutions#rfid technology#rfid tags#rfid reader#rfid protector#tracking software#library#library management system#the smartarts library#public libraries#library automation#inventory software#inventorymanagement#inventory management#stock management software
1 note
·
View note